Cybersecurity Threats in the Healthcare and Public Health Sector
Info: 22639 words (91 pages) Dissertation
Published: 15th Dec 2021
CYBERSECURITY STAT: AN EXAMINATION OF THREATS, POSTURES, AND ENFORCEMENT IN THE HEALTHCARE AND PUBLIC HEALTH SECTOR
Abstract
The purpose of this research was to examine cybersecurity in the Healthcare and Public Health sector (HPH). This research is important in the protection and security of the HPH sector, which affects national security. In 2016, the greatest threat to the HPH sector was ransomware. The examiner researched the evolution of ransomware and its targeted attacks on the HPH sector. This examination attempted to identify its next potential target. In other critical infrastructure sectors, a potential “trickle-down” pattern from large enterprise to small-medium businesses (SMB) was identified and applied to the HPH sector. By applying this pattern, the examiner identified challenges SMB providers face in securing their systems from these threats.
A challenge in defending against these threats is the lack of quality mandated postures within the HPH sector. This research examined mandated postures and identified their ineffectiveness and inefficiency. The examiner also identified voluntary frameworks and tools, which can assist providers in meeting mandates, while maintaining better quality postures at lower costs. The examiner attributed the lack of provider awareness and the lack of provider-implemented quality postures to a lack of enforcement.
This research resulted in a lower-cost proposal for a restructure of the HPH sector by implementing better quality mandated postures and proactive enforcement. This research concluded that the HPH sector must shift from a reactive state to a proactive state to strengthen its security and resiliency.
Keywords: Cybersecurity, Healthcare, Christopher M. Riddell.
Click to expand Table of Contents
Table of Contents
Statement of the Problem……………………………………1
Literature Review……………………………………….7
Ransoms from Physical Space to Cyberspace……………………..8
The Evolution of Ransomware………………………………9
Ransomware in the HPH Sector…………………………….14
Challenges SMB Providers Face……………………………16
Attacker motives………………………………….16
Tools…………………………………………17
Medical Devices………………………………….19
Finances………………………………………21
Postures………………………………………….22
Health Insurance Portability and Accountability Act……………..24
National Health Information Technology Coordinator…………….27
Health Information Technology for Economic and Clinical Health Act…..29
National Institute of Standards and Technology Framework…………32
Health Information Trust Alliance………………………..35
Enforcement………………………………………..37
The Department of Health and Human Services………………..39
HIPAA enforcement………………………………..39
Proactive enforcement proposal…………………………41
Health Care Industry Cybersecurity Task Force………………..46
Commission on Enhancing National Cybersecurity………………47
Discussion of the Findings………………………………….48
Future Research and Recommendations………………………….56
Conclusion…………………………………………..58
References…………………………………………..60
Appendix A – Locky Ransomware Top Affected Industries………………67
LIST OF ILLUSTRATIVE MATERIALS
Figure 1 – Growth in ransomware variants since December 2015………………..13
Figure 2 – Locky ransomware top affected industries………………………67
Cybersecurity Stat: An Examination of Threats, Postures, and Enforcement in the Healthcare and Public Health Sector
The increase in successful ransomware attacks in 2016 was a wakeup call to the Healthcare and Public Health (HPH) sector regarding cybersecurity and risk management. The Commission on Enhancing National Cybersecurity (CENC) recommended that “sector-specific agencies (SSA) and industry associations and organizations should collaborate to develop a program to review past public cyberattacks to identify lessons learned from the event, including a focus on application to small-medium businesses (SMB)” (2016, p. 22). The purpose of this research was to examine the cybersecurity threats and postures of the HPH sector to bring awareness to SMB providers, and to propose to the HPH sector a restructure to ensure proactive cybersecurity standards. This research will answer the questions: What threats and challenges do SMB providers face? What low-cost/no-cost postures are available to defend against these threats? How should the sector restructure to handle these threats?
The HPH sector is a critical area of American infrastructure of which nearly every person is a part. Every individual who had an operation, filled a prescription, went to an annual checkup, or paid for insurance had personal identifying information (PII) collected. In a 2016 Healthcare Information and Management Systems Society (HIMSS) Cybersecurity Survey, 80% of the 150 surveyed HPH providers admitted to experiencing a recent “significant security incident” (p. 5). These security incidents put the data of nearly every individual at risk. Therefore, it is important for providers to be aware of the threats that they face and the adverse effects that could result due to a breach of their system.
The Obama administration aimed to provide better quality healthcare to America. “Over the next 20 years, data analytics will play a powerful role; its greatest impact will be less retrospective (what happened), and more predictive (what might happen) and prescriptive (what could happen)” (CGI Group, Inc., 2015, para. 1). For the HPH sector to become more predictive and prescriptive, they need to collect data to diagnose and treat symptoms during their early stages or, based on family history, before symptoms even start.
The HPH sector stores, shares, and makes that data available across the sector for quicker and easier access. This data includes the most unique and private information: name, address, telephone number, email address, date of birth, social security number, Medicare/Medicaid/insurance identification number, financial information, prescriptions, diagnoses, employment information, emergency contact information, family relations, etc. Essentially, “your hospital has a greater and broader amount of your private data than your employer or your bank does” (Institute for Critical Infrastructure Technology [ICIT], 2016, p. 6).
The HPH sector is a one-stop shop for attackers. The use of more electronic services in HPH organizations increases connectivity and creates instant accessibility and availability to PII, which is valued as a high commodity by cyberattackers (CGI Group, Inc., 2015, para. 4). Unauthorized access to and theft of PII can result in future social engineering and fraud schemes by attackers. Nation-states and organized cyber gangs can gain information on any and every individual through theft of this data, or physically hurt an individual by denying access to this data. These incidents could even potentially threaten human lives in the future.
Cyberattacks are on the rise. By April 2016, “ransomware was one of the greatest threats on the Internet” (KnowBe4, 2016, Timeline 2016 section). Stu Sjouwerman (2017) reported for KnowBe4 that the HPH sector was the largest target of ransomware (para. 1). “The HPH sector is the most targeted, yet unprepared, sector within our Nation’s critical infrastructure” (ICIT, 2016, p.83). The effects of ransomware on the HPH sector posed a risk to system networks and even human lives, blurring the gap between cyberspace and the real world.
The 2016 ransomware attacks targeted large acute care centers and denied them access to patient information unless the ransom was paid. Some paid the ransoms, and others utilized their risk management plan’s contingency procedures to continue operating while the systems were restored from uninfected backups. Unfortunately, aside from conducting forensic analysis afterward, “law enforcement is largely absent” and unable to disrupt these types of attacks during their occurrences, leaving HPH providers to fend for themselves (Leetaru, 2016, para. 5).
Network security extends to medical devices, such as pacemakers and insulin pumps, which are all being connected to the Internet of Things (IoT). These devices, which assist in keeping patients alive, have been breached due to cybersecurity vulnerabilities. Although these breaches have only occurred in lab settings, the experimentation proves that the possibility of breaches occurring outside the lab exists. “Cybersecurity attacks have the potential to yield disastrous results for HPH providers and society as a whole” (HIMSS, 2016, p.14). Therefore, a proactive response to ensure these vulnerabilities are closed is required. It is the responsibility of the HPH sector to ensure its own security from the manufacturer level to the end-user, or providing-entity, level to defend against possible medical device tampering. Those who do not ensure updated security measures on their systems and devices could potentially face costly legal consequences and risk their own patients’ lives.
Postures are implemented to assist in the security of these systems and devices. The Louisiana Department of Health (LDH), formerly the Department of Health and Hospitals (DHH), Medicaid Provider Manual specifies no standards to cybersecurity specifically but advises providers to refer to the Health Insurance Portability and Accountability Act (HIPAA). Providers must “provide safeguards to prevent unauthorized access to protected healthcare information” (DHH, 2016, p. 3). Furthermore, “providers that maintain electronic records must develop and implement a policy to comply with applicable state and federal laws and rules and regulations to ensure each record is valid and secure” (DHH, 2016, p. 4).
Every HPH entity is required to comply with HIPAA. Some of the standards described in HIPAA are required, while others are only addressable – meaning, it is at the discretion of the entity how and whether to implement the standard. Other cybersecurity industry postures, which can include policies, standards, guidelines, and frameworks, are only voluntary. Without stronger required postures, many HPH providers only satisfy the minimum requirements for compliance and “still fail to do the basics” (CENC, 2016, p. 7). Even with minimum compliance, providers still risk leaving their systems and devices open to vulnerabilities. SMB providers are especially vulnerable, specifically those without the financial resources to hire experts for network setups and maintenance; these are the “low-hanging fruit” of the HPH sector.
Many industry members consider HIPAA to be outdated, inefficient, and ineffective. In “How the Lack of Prescriptive Technical Granularity in HIPAA has Compromised Patient Privacy,” industry member, Tim Wafa (2010), argues that HIPAA legislation is flawed due to its overly flexible and broad standards, which cause more confusion to providers than clarity. Other industry members agree that HIPAA is not the definitive security standard. David Finn, Health IT Officer for Symantec, “emphasized that organizations need to stop relying on annual HIPAA compliance risk assessments as measures of data security” (Symantec & HIMSS Analytics, 2016, p. 4). Various voluntary postures are also available for HPH providers to guide and assist them in building secure networks and conducting business safely. These other postures can be utilized in addition to the HIPAA mandates.
While agencies, such as the Centers for Medicare and Medicaid Services (CMS), recognize the need for better postures, they lack giving providers the direction for implementation and continue leaving the matter broad and flexible, causing more confusion among providers. On September 16, 2016, in the “Emergency Preparedness Requirements for Medicare and Medicaid Participating Providers and Suppliers Final Rule” (2016), CMS required “facilities to perform a risk assessment that uses an “all-hazards” approach prior to establishing an emergency plan” (p. 63,861). The Rule established emergency preparedness requirements through a four-element program consisting of risk assessment, policies and procedures, communication plan, training and testing. In the risk assessment section, CMS considers the types of hazards most likely to occur. These include, but are not limited to, “care-related emergencies; equipment and power failures; interruptions in communications, including cyber-attacks; loss of a portion or all of a facility; and, interruptions in the normal supply of essentials, such as water and food” (Emergency Preparedness Requirements for Medicare and Medicaid Participating Providers and Suppliers Final Rule, 2016, pp. 63,861-63,862).
A comment was addressed regarding the inclusion of cybersecurity in the communication planning section of the program. CMS responded stating: “we are allowing facilities flexibility in how they formulate and operationalize the requirements of the communication plan. We have not included specific requirements on cybersecurity and redundancy” (Emergency Preparedness Requirements for Medicare and Medicaid Participating Providers and Suppliers Final Rule, 2016, p. 63,888). Although no specific cybersecurity requirements were implemented for Medicare and Medicaid participating providers, the final rule was effective November 15, 2016, and implementation of the rule is a requirement for providers by November 15, 2017.
In accordance with Presidential Policy Directive-21 (PPD-21), “Critical Infrastructure Security and Resilience,” the Department of Health and Human Services (HHS) is the sector-specific agency (SSA) for the HPH sector. According to the Department of Homeland Security’s (DHS) “Healthcare and Public Health Sector Specific Plan” (2016), HHS is “responsible for managing and coordinating broad-based sector security and resilience activities” and “for bringing together leaders in business and government to prepare for and protect against all hazards facing the Sector” (p. 14). HHS, via their Office for Civil Rights (HHS-OCR), is looking to the National Institute of Standards and Technology (NIST) Framework to assist in applying these standards through the “HIPAA Security Rule Crosswalk to NIST Cybersecurity Framework” (2016).
NIST was constructed to be a flexible framework so that it could be applied to any sector of critical infrastructure. Industry members, such as Ken Durbin, CISSP Strategist: CRM and Threat Intel from Symantec, perceive NIST as “becoming the golden standard for due diligence” in the HPH sector (Kleoppel & Durbin, 2017, 18:40). NIST (2014) states that “organizations may choose to handle risk in different ways, including mitigating, transferring, avoiding, or accepting the risk, depending on the potential impact to the delivery of critical services” (p. 5). However, when NIST is applied to the HPH sector, providers face potential liability when they choose to accept risk.
The current state of the HPH sector is already allowing the acceptation of risk, which is a reason why ransomware attacks have become so successful. The difference between the HPH sector and some other sectors of critical infrastructure is that the data circulating throughout the HPH sector on nearly every individual is too sensitive to accept any type of risk. A credit card number can be replaced, but a patient’s PII or life cannot be replaced.
HPH sector “umbrella” agencies, such as HHS, CMS, and LDH/DHH, put the responsibility of specific cybersecurity postures on the provider. However, it is still the responsibility of HHS, as the SSA, to oversee the guidance of cybersecurity for providers. It is also the responsibility of HHS to oversee and enforce implementation of standard specifics so that the providers may focus on their main priority of providing quality healthcare to those in need.
The recent attacks on the HPH sector are proof that the current mandated postures in place, such as simply referring to HIPAA, are not enough. Furthermore, for years, industry members from Wafa (2010) to Finn (2016) have communicated why they are not enough. The broadness and flexibility of the current mandated postures leave HPH providers confused, more vulnerable, and at risk to the current threat landscape. The industry agencies recognize these vulnerabilities and the need for better postures. However, they do not provide HPH providers with the necessary guidance and mandates for implementing better quality postures. This puts the HPH sector, and furthermore the nation, at risk.
Therefore, it is important for the HPH sector to take its own advice and apply it to cybersecurity. It must implement cybersecurity which is “less retrospective, and more predictive and prescriptive” (CGI Group, Inc., 2015, para. 1). That is, as healthcare becomes more proactive, cybersecurity must become more proactive too. It must continue updating its reactive postures while striving for more proactive postures. These proactive postures must be implemented sector-wide immediately.
Literature Review
The HPH sector is one of the most targeted sectors for cyberattacks due to its insecure networks, vulnerable systems, and the amount of valuable sensitive data it stores and transmits. According to SecurityScorecard’s 2016 Annual Healthcare Industry Cybersecurity Report, the HPH sector suffered 22 major public data breaches between August 1, 2015, and August 1, 2016, ranking it fifth for the most breaches among all other industries (p. 19). The threats the HPH sector faces includes advanced persistent threats, brute force, denial of services, and domain name system poisoning attacks, negligent and malicious insider activity, and attacks involving phishing and spearphishing, social engineering, SQL injection, virus and malware, and wireless jamming or interference attacks. However, in 2016, the HPH sector was the greatest target of ransomware attacks (Sjouwerman, 2017, para. 1).
The 2016 SecurityScorecard report divided the HPH sector into three subsectors, which included healthcare manufacturing, health insurance, and medical treatment. SecurityScorecard’s analysis (2016) showed medical treatment to be the most heavily targeted subsector, with 96% of all detected ransomware targeting acute and non-acute medical treatment centers (p. 18). By examining ransomware and its effects, providers can better understand the challenges they face in defending against these sophisticated attacks.
Ransoms from Physical Space to Cyberspace
On July 1, 1874, four-year-old Charley Ross and his brother were playing in the front yard of his family’s home when they were convinced by strangers to take a ride for candy. Charley’s brother was left at a store but Charley was never seen again. Charley’s father received ransom notes from the kidnappers demanding $20,000 for the child’s return and threatened his life if police intervened. Charley’s father, who was thought to be wealthy, was in debt. With help from police, he made several attempts to pay the ransom, but the kidnappers never appeared. The Charley Ross incident is recorded as the “first kidnapping for ransom case in the United States” (Independence Hall Association, 1995, para. 1).
This crime has been translated from the physical space and implemented in cyberspace. In her book, Cybercrime: Criminal Threats from Cyberspace (2010), Susan W. Brenner discusses the act of committing old crimes in a new space (cyberspace).The act of holding something for ransom is one of those old crimes that has been progressively translated into the realm of cyberspace through ransomware. Microsoft’s Alexs Pena (2016) defines ransomware as “a type of malicious software (malware) or virus that prevents user access to devices, files, or applications, by requiring the victim to pay a ransom in the form of money or information to regain access” (para. 1). The evolution of this crime’s malicious intent from the physical space to cyberspace demonstrates how criminals progressively utilize technology to commit traditional crimes in cyberspace.
Ransomware infections cause loss of access to data, devices, and networks, and possibly theft of data. When a device is infected, the ransomware renders the data or the device inaccessible or unusable by either denying access to the files or denying access to the system altogether. While some ransomware only locks the user out of the files, resulting in a loss of data access to the user, other types of ransomware also steal the data (Ducklin, 2016, para. 26). Even if the user pays the ransom to regain access, the attacker may still gain copies of the intellectual data for use in future social engineering schemes or other nefarious activities, such as selling the data on the Dark Web – the “black market” of the Internet.
The Evolution of Ransomware
The history of ransomware dates to 1989 and the AIDS Information Trojan, also known as the PC Cyborg. “This ransomware not only demonstrated the concept but also integrated with some of the well-known techniques used by malware authors” (Giri & Jyoti, 2006, p. 2). Before the Internet was widely used, the ransomware was copied onto floppy disks and distributed to attendees of the World Health Organization’s International AIDS Conference. Once the malware was installed on a system, it replaced the autoexec.bat file and counted the number of system reboots. After recording ninety system reboots, the Trojan encrypted all files contained in the C drive and hid them, rendering the device unusable. The ransomware displayed a message to the user to mail $189 to a Panama post office box to recover the locked files. KnowBe4 (2016), named one of the top 500 cybersecurity training companies, termed this strain as “generation one” of ransomware (Timeline 1989 section, para. 1).
Seventeen years later, the Archiveus Trojan was the first ransomware to utilize RSA encryption. Archiveus affected Microsoft Windows operating systems. The malware copied all files contained in the user’s My Documents folder and encrypted them, then deleted the original files. The malware directed its victim to a specific website, where they were required to purchase products to obtain the decrypting password. (Hayashi, 2007, “Technical Details,” para. 5)
The WinLock malware was a type of ransomware that did not utilize encryption. Instead, the malware locked out users by displaying pornographic images and required the user to send a premium SMS message at a $10 rate. After sending the message, the victim received a code to unlock the system. This malware mostly circulated around Russia but earned the attackers over $16 million in one month (Leyden, 2010, para. 3).
The year 2012 was the “coming of age” for ransomware with the first large scale ransomware outbreaks. Malware authors utilized anonymous payment services through the malware toolkit Citadel, which allowed malicious users to pay-per-install and infect systems for a fee (KnowBe4, 2016, Timeline 2012 section, para. 1). Citadel targeted users of online banking. Running alongside Citadel was Reveton. Reveton was a variant of Citadel, which attempted to extort victims through fraudulent criminal fines of child pornography. Once the malware installed on the system through a drive-by download website, a message displayed notifying the victim that their “IP address was identified by the Federal Bureau of Investigations (FBI) as visiting child pornography and other illegal content” (FBI Internet Computer Complaint Center, 2012, para. 1). To regain access, the ransomware required the victim to utilize prepaid money card services to pay a “fine” to the Department of Justice (DOJ). However, even though the victim regained access to their computer from Reveton, the Citadel malware continued to operate in the background. By July 2012, “ransomware detections increased to more than 200,000 samples or more than 2,000 per day” (KnowBe4, 2016, Timeline 2012 section, para. 5).
The year 2013 saw the emergence of Cryptolocker in addition to ransomware targeting Apple and Android devices. Cryptolocker was the first cryptographic malware spread through compromised website downloads and malicious email attachments (KnowBe4, 2016, Timeline 2013 section, para. 4). Cryptolocker encrypted files with specific file extensions using a 2048-bit RSA key pair and deleted the original files (KnowBe4, 2016, Timeline 2013 section, para.5). If payment was not received within a pre-determined time, the victim received another opportunity to unlock their files by paying a higher ransom amount and was threatened with destruction of the private key.
In March 2014, CryptoWall, an evolution of CryptoDefense, was released. Dell’s SecureWorks Counter Threat Unit (2014), at the time, considered CryptoWall to be “the largest and most destructive ransomware threat on the Internet and they expected this threat to continue growing” (para. 1). This malware utilized a Java vulnerability, which affected more than 600,000 systems, by infecting popular domains, such as Facebook and Disney, with malicious advertisements (KnowBe4, 2016, Timeline 2014 section, para. 2). By the end of 2014, Symantec reported a 700% increase in the crypto-style ransomware when malware authors required victims to install Tor, an anonymizing software, to remit payments (Symantec, 2014, p. 3).
May 2015 saw the emergence of ransomware-as-a-service, such as Tox, and sleeper ransomware, such as Locker. Tox is a Tor website created “for criminals by criminals,” where prospective attackers can create their own ransomware for free, and the “site takes a 20% kickback of every Bitcoin ransom payment” received (KnowBe4, 2016, Timeline 2015 section, para. 3). In addition, Locker was released and identified as another type of malware called sleeper ransomware. The malware was installed on a target system and sat dormant until a specified time. At that time, any infected system containing the malware woke up and encrypted its files. The victim received a ransom note which read, “Warning: any attempt to remove, damage, or even investigate the Locker software will lead to immediate destruction of your private key on our server!” (Sjouwerman, 2015, para. 7). Along with deleting shadow files, Locker also identified virtual machines and terminated if detected.
TorrentLocker, TeslaCrypt V2.0, and LockerPin emerged in 2015. The TorrentLocker ransomware campaign “rebuilt whole websites of energy companies, government organizations, and large enterprises to spread ransomware through Google Drive” (KnowBe4, 2016, Timeline 2015 section, para. 7). TeslaCrypt V2.0 targeted game-related file types, and LockerPin, an Android ransomware, could reset the PIN and deny access to mobile devices.
By the end of 2015, ransomware became a sophisticated type of malware as infection rates increased. Namestnikov (2015) reported for Kaspersky Labs that ransomware infections doubled from 2014 (p. 14). In addition, Pajares and Oliver (2015) reported analysis for Trend Micro showing malware groups moving to SMB targets as they generally do not implement the same defenses utilized by large enterprises (para. 1). At the October 21, 2015, Cybersecurity Summit, Joseph Bonavolonta, Assistant Special Agent in Charge of FBI Cyber and Counterintelligence in Boston, was quoted as advising companies to just pay the ransom if infected, because “the ransomware is that good” (Roberts, 2015, para.3).
The sophistication of ransomware continued to grow throughout 2016. Ransomware development in languages, such as JavaScript, HTML, and CSS, allowed ransomware to be non-operating-system-specific; this means the malware can infect across all platforms. In addition, malware authors began hiding the ransomware payload in infected Word files. As depicted in Figure 1, the first three months of 2016 showed a significant increase in ransomware evolutions and the variety of variants released into the wild. Cyber criminals collected $209 million during these three months, putting ransomware “on pace to be a $1 billion a year crime” (KnowBe4, 2016, Timeline 2016 section, para. 10).
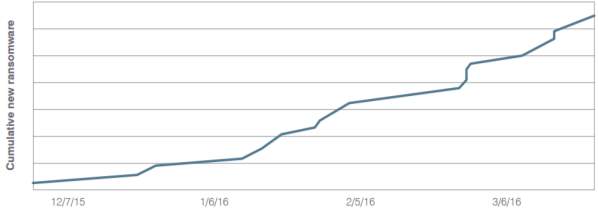
Figure 1. Growth in ransomware variants since December 2015 (ProofPoint, Inc., 2016, p. 9).
Many cyberattacks are now run by organized cybercrime gangs. These attacks developed at a much faster rate due to the “formation of an active underground economy, where stolen goods and illegal services are bought and sold in a professional manner,” and “where all the tools needed to conduct an attack are for sale” (Robb, 2016, p. 2). This evolution, coupled with the ease in which social engineering advances an attack, pushed ransomware into becoming one of the greatest threats on the Internet by April 2016. The year 2016 also marked the greatest targeted attacks within the HPH sector, where ransomware services and stolen electronic health records (EHRs) were being sold in this underground market.
Ransomware in the HPH Sector
The HPH sector received multiple warnings that their cybersecurity was inadequate to protect against the current threat landscape. In 2014, the FBI “warned HPH providers that the industry is not as resilient to cyber intrusions compared to the financial and retail sectors, therefore the possibility of increased cyber intrusions is likely” (CGI Group, Inc., 2015, pg.1). In addition, “the FBI warned HPH providers that their cybersecurity systems were not robust enough to resist hacker threats” (Gomez & Konschak, 2015, pg. 2). This cycle continued to 2015, when the Health Information Trust Alliance (HITRUST) found that “today’s approach to cybersecurity is predominantly reactive and inefficient” (Gomez & Konschak, 2015, pg. 2). Even with multiple warnings, the HPH sector still fell victim to sophisticated ransomware attacks.
On February 5, 2016, Locky infected Hollywood Presbyterian Medical Center, located in Los Angeles, CA. The ransomware was delivered through socially engineered emails that were disguised as invoices. Each email contained an attached Word document with malicious macros. When the recipient opened the attachment, the text was unreadable, and the recipient was prompted to enable macros. Upon enabling macros, the malware downloaded, installed, and executed the malicious Locky software. Files were encrypted and renamed, and the affected users were denied access to the locked data. A ransom note replaced the desktop with instructions on how to regain access to the locked files. To obtain the decryptor, users were required to access the Tor network, obtain bitcoin currency, and send the ransomed amount of bitcoin to a specified address.
The Locky ransomware was the largest campaign to target the HPH sector. Levene, Yates, and Downs (2016) reported analysis for Palo Alto Networks showing that when the Locky ransomware was released, it infected over 400,000 workstations (para. 8). In March 2016, Locky hit the MedStar Hospital chain, which operated hospitals in the Washington, DC, and Maryland areas. Approximately 30,000 staff and about 6,000 affiliate physicians were affected by Locky, requiring MedStar to take all systems offline and resort back to pen and paper (Phillips, 2016, para. 1). Methodist Hospital, located in Kentucky and operated by Prime Healthcare Management, Inc., also shut down systems before paying the ransom. Gallagher (2016) reported the attack also disrupted services of other hospitals and care providers who shared systems within its network (para. 6). King’s Daughters’ Health, located in Indiana, was another victim of the Locky infection. In July 2016, UCLA Health System computer networks may have had as many as 4.5 million patient records accessed (Winton, 2016, para. 15).
The Locky ransomware campaign became the wakeup call the HPH sector needed. Chong (2016) reported analysis for FireEye (see Appendix A), which showed the HPH sector was the top-affected industry by the Locky ransomware (para. 1). Although Locky was a large campaign that greatly affected the HPH sector, there are many other ransomware strains which continue to go unreported. According to Bob Chaput of Clearwater Compliance, FBI estimates show that only 10% of ransomware attacks are reported (Finn & Chaput, 2017, 10:38). Only when ransomware is reported, can a potential solution to the threat be harnessed.
Over the last 28 years, ransomware evolved from a primitive to a sophisticated type of malware. The effects of ransomware have peaked in recent years “due to the ease in which such extortion translates directly to money; and it has enjoyed a renaissance of sorts with the confluence of improved targeting, the all-digital workplace, and bitcoin to provide secure anonymized funds transfers” (Leetaru, 2016, para. 1). The examination of its evolution demonstrated how malware authors progressed in the development of ransomware and each of its iterations. According to the 2016 HIMSS Cybersecurity Survey, when 150 HPH organizations were asked to rate their IT infrastructure in the protection and detection against ransomware, only 68.1% had confidence in their infrastructure’s defense against it (p. 8).
Challenges SMB Providers Face
SMB providers face many challenges in the security of the data and systems they utilize to provide patients with faster and higher quality healthcare. Attackers have recognized the value of the data available within the HPH sector. Sophisticated attacks, such as ransomware, provide cyberattackers the opportunity to extort money by threatening patient lives. New threats evolve daily and extend further through their different strains or variants. New technology integrates with old technology into one complex network that must be secure while remaining accessible to providers. Generally, SMB providers also have fewer assets and financials than larger providers, and, therefore, they lack the ability to implement higher and more costly standards and expertise. These challenges create a “perfect storm” for SMB providers and great opportunities for attackers to take advantage.
Attacker motives
The HPH sector and SMB providers are especially affected by the change in attacker motives. In the past five years, cyberattacks on HPH systems have increased 125% (Symantec & HIMSS Analytics, 2016, para. 2). The valuable return – that is, the data obtained in the cyberattacks – can be sold in the underground markets on the Dark Web. Symantec & HIMSS Media (2016) estimated that while social security and credit card numbers sold for $1 on the black market, EHRs sold for $50 or more per chart (p. 1). Theft of valuable data, such as PII, can also be utilized to conduct additional targeted attacks on the business entity, on their network, on individuals, or on medical equipment and devices. Even the cyber-terrorist group, “Deep Panda, has a five-year strategic attack plan focused on healthcare targets” (Gomez & Konschak, 2015, p. 5). In an interview with Rachel Polansky for NBC2, Mike Smith, Director of IT at Lee Health, the largest healthcare provider in Lee County, FL, stated, “Less than 10% of the email traffic coming into Lee Health is legitimate, and that is what most companies around the country are dealing with right now” (Polansky, 2017, para. 19).
The growing reports of HPH sector intrusions and intrusion attempts display a change in motivational efforts, where attackers have shifted from targeting financial information only to targeting EHRs. EHRs include PII, personal health information, and financial information. EHRs allow providers quick transmission of and access to patient records. Gomez and Konschak (2015) claimed, SMB non-acute care providers, such as physician offices, are one of the biggest threats to large acute care providers, because the SMB providers “typically have relatively unsophisticated systems with minimal security,” which connect and transmit data to larger HPH providers (p. 5). Attackers target the HPH sector as an industry with valuable information but one not prepared to defend itself against such attacks, no matter the size or type of entity.
Tools
The 2016 HIMSS Cybersecurity Survey evaluated cybersecurity challenges regarding threats faced and tools utilized by acute and non-acute care providers. Acute care providers included healthcare systems and hospitals, while non-acute care providers included ambulatory and outpatient services, physician offices, mental and behavioral health facilities, and other healthcare facilities, such as home health agencies. Of the 150 respondents, 80% experienced a recent “significant security incident” (HIMSS, 2016, p. 5). The study showed acute care providers had a “greater array of security technologies in their portfolio than non-acute care providers”; this was attributed to the larger acute care providers “potentially having relatively more financial resources to invest in such technologies” than the SMB non-acute care providers (HIMSS, 2016, p. 2). The tools surveyed included antivirus/malware, firewalls, data encryption during transit, data encryption at rest, audit logs, patch and vulnerability management, intrusion detection systems, intrusion prevention systems, network monitoring tools, mobile device management, user access controls, access control lists, single sign-on, web security gateway, messaging security gateway, and multi-factor authentication.
Of those tools, antivirus/malware and firewalls, encryption in transit and at rest, and patch and vulnerability management were three of the top-utilized tools. The study found that only 84.9% of acute care providers and 90.3% of non-acute care providers utilized antivirus/malware and firewalls (HIMSS, 2016, p. 3). “Without the use of a firewall, providers lack the ability to prevent or mitigate viruses, malware, and other forms of malicious software” (HIMSS, 2016, p. 3). With the increase in ransomware variants, this lack of basic defenses leaves HPH provider systems and data vulnerable.
Encryption in transit and at rest is an extra layer of protection even if the system is compromised because attackers would need to crack the encryption to read the data. Only 68.1% of acute care providers and 48.4% of non-acute care providers utilized encryption in transit; similarly, only 61.3% of acute care providers and 48.4% of non-acute care providers utilized encryption at rest (HIMSS, 2016, p. 3). When providers lack encryption in transit, they are sending data “in the clear” – meaning, the data is vulnerable to eavesdropping and packet sniffing, and therefore, vulnerable to compromise (HIMSS, 2016, p. 3). Encryption is like a vaccine in the medical field, and it is a plan of contingency in cybersecurity. If a virus enters a person’s body, the infection can potentially be prevented with the proper vaccine. Similarly, if an attacker gains access to a system, encryption could potentially stop the attacker from compromising the integrity of the data.
Patch updates manage and close detected vulnerabilities. Only 61.3% of acute care providers claim to regularly maintain patch and vulnerability management, while even less non-acute care providers, only 41.9%, maintain patch and vulnerability management (HIMSS, 2016, p. 3). HIMSS (2016) found many to struggle with this because it requires continuous maintenance (p. 3). However, unpatched and vulnerable systems provide attackers with access. “Just as our roads and bridges need regular repair and upkeep, so do the technical linkages that allow the information superhighway to flow” (Cybersecurity National Action Plan Factsheet, 2016, para. 39).
Even though antivirus/malware and firewalls, encryption at rest and in transit, and patch and vulnerability management were three of the highest-utilized tools, their survey numbers scored relatively low. In addition, the provider-utilization percentages for the remaining surveyed tools continued to decline. The implementation of these minimum defenses is not enough. “Today, attackers could infiltrate the EHR and delete important patient data, such as information about a penicillin allergy or diabetes” (Gomez & Konschak, 2015, p. 4). In this case, unauthorized access of EHRs resulting in data manipulation becomes just as dangerous as data theft. Additionally, ransomware can deny them all access to this important patient data when it is needed the most. Furthermore, medical devices are also vulnerable to these attacks.
Medical devices
Ransomware causes disruptions in medical networks, access to medical records, and invasion of privacy. In addition, ransomware could pose a potential risk to medical devices thereby threatening patient safety. The multitude of devices connected to the Internet makes up the IoT, which provides “increased access to diagnostic testing, comprehensive treatment, and preventative care” (ICIT, 2016, p. 45). “We are experiencing a revolution in which all objects in our daily lives are converging on similar computing and communication capabilities, and therefore also on similar susceptibility to cyber threats” (CENC, 2016, p. 23).
HPH providers utilize a variety of both legacy and newly developed machines and devices all run by computer chips. “Anything with a computer chip offers attackers an entry point – even if the device is not connected to the Internet” (Gomez & Konschak, 2015, p. 3). The ICIT (2016) likens a network’s cybersecurity to a castle, where any unsecured devices connected to the network are like the secret passages that must be guarded to keep intruders from gaining access inside the castle (p. 47). Unfortunately, there is much disagreement regarding who is responsible for device security: the provider utilizing the device or the manufacturer developing the device. The reality is that both are responsible for device security.
Medical device security starts at the manufacturer and developer level and continues to the provider level. According to Symantec and HIMSS (2016), “medical device manufacturers are not mandated to incorporate cybersecurity features in their design and development” (p. 1). Because of this, the complex network of connected medical devices becomes a new target for attackers. The CENC (2016) found that manufacturers race their products through development to be the “first to market,” which too often compromises quality testing and the necessity to be “secure to market” (p. 26). ICIT (2016) agrees, advising that “developers should produce code with a security-by-design structure instead of implementing security as an afterthought” (p. 48).
At DefCon 2011, researcher Jay Radcliffe, also a diabetic, discovered how to hack his insulin pump and cause it to dispense the incorrect amount of insulin, which could be fatal. Furthermore, “during his tenure as Vice President, it was discovered that Al Qaeda operatives were attempting to compromise Dick Cheney’s pacemaker by exploiting an unsecured Bluetooth connection” (ICIT, 2016, p. 10). If these devices are not secured, the threat of ransomware could stop them from working. Furthermore, if the data in an automated surgical tool is manipulated, it could result in a larger incision than it was originally programmed to make. To ensure better medical device postures and avoid a medical device Stuxnet situation, “empirical evidence of aggressive penetration testing before and after a medical device is released to the public must be a manufacturer requirement” (ICIT, 2016, p. 83).
Finances
Poor cyber postures are even more prevalent among HPH SMB providers due to their lack of finances and expertise. “For some SMBs, the security of their information, systems, and networks either is not their highest priority or is something they do not have the resources to address” (CENC, 2016, p. 21). CGI Group, Inc. (2015) attributes this lack of defenses to a “lack of capacity or financial means to effectively address these growing challenges” (p. 1). In addition, the HIMSS survey (2016) showed high agreement among surveyed providers, that a lack of appropriate cybersecurity personnel and a lack of financial resources were the biggest barriers to mitigating cybersecurity risks (p. 10).
Furthermore, in personal communications with HPH providers, some SMB providers would rather risk compromise of their patient data and pay the monetary non-compliance penalty, because it is more affordable than implementing and maintaining quality postures and complying with mandates. “One could argue that HPH providers, whose mission is to help patients according to the Hippocratic Oath, have a responsibility to protect patient and employee data” (ICIT, 2016, p.6). According to ICIT (2016), by ignoring or skirting this responsibility, the provider, instead, is placing its patients in direct harm (p. 6). If attackers recognize these patterns, in addition to the previously discussed Trend Micro claim, then as major medical providers and manufacturers harden their systems, attacks will “trickle down” to target the SMB providers and manufacturers – those less likely to have hardened defense systems implemented.
No matter the size of the HPH provider, none are immune to the growing cyber threats, especially the SMB providers, who are the current “low-hanging fruit.” The CENC (2016) estimated that “the cost to attack a system is only a fraction of the cost to defend it” (p. 7). Time and easily accessible tools give attackers the advantage because a “security team has to protect thousands of devices while a malicious actor needs to gain access to only one” (CENC, 2016, p. 7). For the HPH sector, “the economic impact of cyberattacks is tremendous; the Ponemon Institute estimates they cost a healthcare system $5.6 billion a year to respond to the breach, provide defense, pay damages, and defend claims” (Gomez & Konschak, 2015, p. 3). Cybersecurity is not a “one-and-done task” for any sized entity. It must continue to evolve with the evolving threat landscape and so must cybersecurity postures.
Postures
The solution to these challenges begins with the provider’s postures. Postures are the policies, standards, guidelines, best practices, frameworks, and risk management programs put in place to secure networks and increase awareness. However, the CENC (2016) found that “many organizations, if not most, rely on policies, frameworks, and standards that have not been updated to take technological innovations into account” (p. 8). In the HPH sector specifically, Symantec and HIMSS Analytics (2016) found that “EHRs and digital clinical systems have been deployed without strategic data and IT infrastructure security planning” (p. 1). In addition, Symantec and HIMSS Analytics (2016) estimated that many HPH providers allocate less than 6% of their IT budget to cybersecurity (p. 2). Furthermore, Symantec and HIMSS Media (2016) found that “only 23% of surveyed HPH organizations have an ongoing, consistent risk management program” (p. 1). These postures are ineffective without full provider participation, especially if providers are not continuously updating their postures to match the continuously-changing threat landscape.
Through the examination of the evolutionary history of ransomware, providers gained an understanding of how quickly these threats can change. Gomez and Konchak (2015) warn providers that “no HPH organization, no matter how small, is immune to cyber threats” (p. 2). Each new variant of ransomware increases the magnitude of detrimental effects on providers, especially when they lack a continuous security and risk management lifecycle. The example also demonstrated the challenges providers, especially SMB providers, face in securing complex networks made up of a variety of devices, both old and new. David Finn of Symantec reported that “over one-third of organizations are still only complying with key mandates or only implementing basic security controls” (Finn & Chaput, 2017, 43:44). Those SMB providers who do not implement quality cybersecurity postures endanger their patients and become a threat to larger entities with whom they transmit data. “A failure anywhere in this complex environment can have immediate cascading consequences across the sector” (DHS, 2016, p. 33). These SMB providers, who make up a large amount of the HPH sector, therefore, endanger the entire HPH sector.
Each provider must comply with postures set forth from their respective “umbrella” agencies in the defense against cyberthreats. However, “the HPH threat environment is a dynamically changing cyber landscape, while legislation, on the other hand, is stagnant” (ICIT, 2016, p. 68). For example, Medicaid providers in Louisiana must comply with standards and regulations set forth by the Louisiana Department of Health (LDH), formerly the Department of Health and Hospitals (DHH). However, in their updated provider manual, there is no section regarding the requirements for cybersecurity specifically. Furthermore, in personal communications with LA Medicaid SMB providers, some claimed they are unaware of any mandates regarding cybersecurity.
The updated provider manual simply refers providers to HIPAA. “HIPAA requires providers to provide safeguards to prevent unauthorized access to protected health care information” (DHH, 2016, Provider Requirements section 1.1, p. 3). In addition, under the manual’s Electronic Health Records section, “providers that maintain electronic records must develop and implement a policy to comply with applicable state and federal laws and rules and regulations to ensure each record is valid and secure” (DHH, 2016, Provider Requirements section 1.1, p.4). Furthermore, LDH/DHH makes no specification of those laws, rules, and regulations, other than HIPAA.
Health Insurance Portability and Accountability Act
The Health Insurance Portability and Accountability Act (HIPAA) was enacted in 1996 to protect health insurance coverage and establish national standards for securing healthcare information. The goal of HIPAA was to:
Improve portability and continuity of health insurance coverage in group and individual markets, to combat waste, fraud, and abuse in health insurance and healthcare delivery, to promote the use of medical savings accounts, to improve access to long-term care services and coverage, to simplify the administration of health insurance. (HIPAA, 1996, p.1)
Title II of HIPAA set an important rule, the Security Rule, regarding the protection of healthcare information, or as it is known under HIPAA, electronic protected health information (ePHI).
The Security Rule was issued in 2003. It necessitated that HIPAA-covered entities and business associates “protected against any reasonably anticipated threats, hazards, or disclosures” by ensuring compliance in “the confidentiality, integrity, and availability of all ePHI that the entity created, received, maintained, or transmitted” (HHS-OCR, 2013, p. 63). The Security Rule set a flexible approach of security standards for ePHI. This approach stated that “covered entities and business associates may use any security measures that allowed [them] to reasonably and appropriately implement the standards” based on the “size, complexity, and capabilities of the entity” (HHS-OCR, 2013, p. 63).
The specified implementations were categorized by administrative safeguards, physical safeguards, and technical safeguards. The Security Rule’s administrative safeguards set standards for the implementation of a security management process through risk analysis, risk management, sanction policies, and information system activity reviews; assigned security responsibility; workforce security; information access management; security awareness and training; security incident procedures; contingency plans; and evaluation (HHS-OCR, 2013, p. 64-65). The Security Rule’s physical safeguards necessitated facility access controls; workstation use; workstation security; and device and media controls through means of disposal, media reuse, accountability, and data backup and storage (HHS-OCR, 2013, p. 66). The Security Rule’s technical safeguards put forth standard access controls in the form of unique user identification, emergency access procedures, automatic logoff, and encryption/decryption standards; audit controls; integrity in the form of mechanisms to authenticate ePHI; person or entity authentication; and transmission security in the form of integrity controls and encryption (HHS-OCR, 2013, 66-67).
The Security Rule also specified which safeguards are required for HPH entities to implement and which safeguards are addressable. Addressable safeguards allow entities to evaluate their infrastructure and implement the specifications as they see fit. If the safeguard specification is unnecessary for the entity’s operation, then the entity simply documented their justification for not implementing it. This provided HPH entities with flexibility to customize their cybersecurity implementations. However, this flexibility also puts providers at risk to cyberthreats.
HIPAA also does not specify the levels of security required. For example, in the technical safeguards, only two items – standard access controls and emergency access procedures – are identified as being required; the rest are addressable. Encryption is one of those addressable safeguards. Unfortunately, few providers implement this safeguard. The 2016 HIMSS Survey reported less than half, 48.4%, of non-acute care centers used encryption in transit and at rest (p. 2). Furthermore, there are multiple types of encryption and some are stronger than others. However, a provider could implement the weakest level of encryption and still be compliant. This is termed minimum compliance. According to David Finn, of Symantec, approximately one-third of providers only minimally comply with basic security controls (Finn & Chaput, 2017, 43:44).
Minimum compliance leaves providers open and more vulnerable to threats, and therefore the minimum-security measure becomes worthless. Skilled attackers can crack the minimum levels of encryption thereby giving them access to a multitude of EHRs. However, if the maximum level of encryption, that was available at the time, were mandated and implemented, the provider would be less vulnerable to the threat. In the HPH sector, “many organizations focus on meeting the requirements set by HIPAA and its provisions; however, organizations should consider that often-regulatory requirements are minimum “check box” items rather than comprehensive programs” (ICIT, 2016, pp.23-24).
For these reasons, many industry members consider HIPAA to be outdated, inefficient, and ineffective. For example, industry member, Tim Wafa (2010) argues that HIPAA legislation “has a severe flaw deep within its architecture, one which is severely compromising patient privacy” (p. 531). Wafa argues this is due to its overly flexible and broad standards. However, the drafters of HIPAA “opposed linking their standards to specific technologies” and argued this flexibility was “necessary to ensure covered entities are not overburdened” (Wafa, 2010, pp. 541-542). But, Wafa (2010) maintains that this flexible approach “gives too much latitude to covered entities and therefore fails to provide adequate protection” (p. 532). “Without sufficient granularity, healthcare providers are left to assess solutions independently, too often without adequate resources or the expertise necessary to make an informed decision” (Wafa, 2010, p. 533). Wafa’s argument still holds true today according to David Finn, Health IT Officer for Symantec, who “emphasized that organizations need to stop relying on annual HIPAA compliance risk assessments as measures of data security” (Symantec & HIMSS Analytics, 2016, p. 4). Fortunately, there are other postures that are available to assist SMB providers in the continuity of cybersecurity maintenance and management.
National Health Information Technology Coordinator
On April 27, 2004, President George W. Bush signed Executive Order 13,335, “Incentives for the Use of Health Information Technology and Establishing the Position of the National Health Information Technology Coordinator” (NHITC). The President ordered the establishment of a “nationwide interoperable health information technology infrastructure” (Executive Order No. 13,335, 2004, p. 24,059). The NHITC was responsible for “addressing privacy and security issues related to interoperable health information technology and recommending methods to ensure appropriate authorization, authentication, and encryption of data for transmission over the Internet” (Executive Order No. 13,335, 2004, p. 24,060).
This was the beginning of the HPH reformation and restructure. The goal was to make medical data available immediately, thereby providing better quality healthcare. However, “the reliance on technology expands the potential vulnerabilities and potential risk to critical infrastructure operations” (NIST, 2014, p. 3). Therefore, it was the responsibility of the NHITC and the Health Information Technology (HIT) Policy Committee to address these potential vulnerabilities.
The HIT Policy Committee shall recommend the areas in which standards, implementation specifications, and certification criteria are needed for the electronic exchange and use of health information…and shall recommend an order of priority for the development, harmonization, and recognition of such standards, specifications, and certification criteria among the areas so recommended. Such standards and implementation specifications shall include named standards, architectures, and software schemes for the authentication and security of individually identifiable health information and other information as needed to ensure the reproducible development of common solutions across disparate entities. (American Recovery and Reinvestment Act, 2009, p. 120)
This resulted in the “Guide to Privacy and Security of Electronic Health Information” (2015), which was produced by the Office of the National Coordinator for Health Information Technology (ONC-HIT) and the director of NIST.
The Guide is not considered a requirement or mandate but was developed to assist providers in meeting federal requirements, such as HIPAA. However, ONC-HIT still warns providers that “your practice – not your EHR developer – is responsible for taking the steps needed to protect the confidentiality, integrity, and availability of health information in your EHR” (ONC-HIT, 2015, p. 9). The intent of the Guide is to “help HPH providers better understand how to integrate federal health information privacy and security requirements into their practices” (ONC-HIT, 2015, p. 5). ONC-HIT recommended that providers start with a risk assessment of their organization and the identification of their assets.
ONC-HIT provided a tool to assist in conducting risk assessments. “ONC worked with OCR to create a Security Risk Assessment (SRA) Tool to help guide HPH providers (from small practices) through the risk assessment process” (ONC-HIT, 2015, p. 36). The SRA tool assists providers in setting up and maintaining risk assessments to satisfy the HIPAA standard, but HIPAA does not require providers to utilize this tool. The SRA tool is available for free download on the HealthIT website and includes an instructional video.
The Guide also references the NIST framework. ONC-HIT (2015) recognizes NIST as providing “valuable information to support a strong security program” for the provider (p. 7). The recognition of NIST helps satisfy the NHITC’s requirement to “recognize a program or programs for the voluntary certification of health information technology as being in compliance with applicable certification criteria adopted under this subtitle, including testing of the technology in accordance with the Health Information Technology for Economic and Clinical Health Act” (American Recovery and Reinvestment Act, 2009, p. 118).
Health Information Technology for Economic and Clinical Health Act
The Health Information Technology for Economic and Clinical Health (HITECH) Act was implemented under the American Recovery and Reinvestment Act of 2009. The purpose of the HITECH Act was to “promote the adoption and meaningful use of health information technology” (HHS, 2017, para. 1). Subtitle D of the HITECH Act also introduced breach notification requirements. Under this section, HHS “required covered entities under HIPAA and their business associates to provide notification in the case of breaches of unsecured protected health information” (Breach Notification for Unsecured Protected Health Information Interim Final Rule, 2009, p. 42,740).
However, breaches continue to go unreported. Stu Sjouwerman (2017), from KnowBe4, found data which showed that “more than half of hospitals were hit with ransomware from April 2015 to April 2016, but breach reporting to OCR was practically non-existent” (para. 2). The examination of the evolutionary history of ransomware demonstrated an increase in detected attacks in the HPH sector. An increase in attacks, therefore should cause an increase in breach notifications. However, Sjourwerman (2017) also found that “only nine organizations reported malware or ransomware breaches to HHS-OCR in 2016” (para. 4).
The HITECH Act does not require notification of a breach if the ePHI was encrypted because it considers the data to be secure.
If a covered entity chooses to encrypt ePHI to comply with the Security Rule and discovers a breach of that encrypted information…the covered entity will not be required to provide breach notification because the information is not considered “unsecured protected health information” as it has been rendered unusable, unreadable, or indecipherable to unauthorized individuals. (Breach Notification for Unsecured Protected Health Information Interim Final Rule, 2009, pp. 42,741-42,742)
However, encryption, especially weak encryption, can still be broken. If an attacker cracks the encryption, then the data is no longer secure. Encryption methods can create another obstacle for attackers and potentially prevent them from accessing the data, however, like a flu vaccine, it is not absolute.
The HITECH Act raised much confusion regarding the impacts it had on entities complying with the HIPAA Security Rule. Although it did not “modify a covered entity’s responsibilities with respect to the Security Rule, nor did it impose any new requirements upon covered entities to encrypt all ePHI,” it sought to reinforce the HIPAA Security Rule (Breach Notification for Unsecured Protected Health Information Interim Final Rule, 2009, p. 42,741). Under the HIPAA Security Rule:
A covered entity must consider implementing encryption as a method for safeguarding ePHI; however, because these are addressable implementation specifications, a covered entity may be in compliance with the Security Rule even if it reasonably decides not to encrypt ePHI and instead uses a comparable method to safeguard the information. (Breach Notification for Unsecured Protected Health Information Interim Final Rule, 2009, p. 42,741)
Although government postures and solutions may bring confusion and too much flexibility, they are still necessary to ensure common requirements are met. However, until better postures are mandated, there are other non-government organizations who aid providers struggling to meet these requirements.
For example, NIST created a common framework that any organization in any area of critical infrastructure can utilize and implement. In addition, HITRUST is an organization also developing a common framework, however, their framework is designed specifically for the HPH sector. HITRUST believes a common framework “will result in better health information security sooner than mandates imposed by government “solutions” that will not recognize business and technological realities and cannot adapt quickly enough to changing conditions” (HITRUST, 2017, Policy Advocacy section, para. 3). HITRUST’s framework even incorporates standards set by NIST.
National Institute of Standards and Technology framework
The United States government and “umbrella” agencies recognize the need for cybersecurity postures but are slow to mandate and update any specific requirements. As many as “20% of respondents to a HIMSS Analytic Healthcare IT Security and Risk Management Study comply with key mandates only, such as HIPAA and HITECH, but neither regulation addresses significant changes” (Symantec & HIMSS Media, 2016, p. 1). The 2016 ransomware attacks proved that these broad and flexible, required and addressable implementations are not enough to protect the HPH sector and have not yet brought enough awareness to SMB providers within the sector. “Critical infrastructure owners and operators deserve a clearer guidance and a set of common understandings” (CENC, 2016, p. 13). The NIST framework seeks to provide that clearer guidance in the realm of cybersecurity and risk management.
In response to ongoing cyber threats, President Barack Obama signed Executive Order 13,636, “Improving Critical Infrastructure Cybersecurity,” on February 12, 2013, to strengthen national cybersecurity infrastructure. The order directed NIST to develop a framework to reduce cyber risks and include “a set of standards, methodologies, procedures, and processes that align policy, business, and technological approaches” (Executive Order No. 13,636, 2013, p. 11,741). The order also directs this framework to be “updated as necessary, taking into consideration technological changes, changes in cyber risk, operational feedback, experience from the implementation of a voluntary critical infrastructure cybersecurity program, and other relevant factors” (Executive Order No. 13,636, 2013, p. 11,741).
The NIST framework was designed to be flexible so that it could be implemented by any critical infrastructure sector. Any sized entity, large or small, can utilize the framework, no matter its level of cybersecurity posture maturity. “Each organization’s risk is unique, therefore to manage cybersecurity risks, a clear understanding of the organization’s business drivers and security considerations specific to its use of IT is required” (NIST, 2014, p. 3). Although not industry specific, the NIST framework “complements an entity’s risk management plan” or those without one can “use the framework as a reference to establish one” (NIST, 2014, p. 4). The NIST framework can be utilized in the HPH sector by both large providers and SMB providers.
The core of the NIST framework consists of five industry-standard functions: Identify, Protect, Detect, Respond, and Recover; the second part of the framework consists of Implementation Tiers. The Framework Core is a set of activities and tasks, which assist an entity in identifying assets, protecting assets from vulnerabilities, detecting threats exploiting vulnerabilities, responding to detected attacks, and recovering from attacks to resume normal business operations. It guides the entity through activities and tasks to help it achieve the desired target security environment. The Implementation Tier “provides context on how an organization views cybersecurity risk and the processes in place to manage that risk” ranging from the Partial, Risk-Informed, Repeatable, and Adaptive Levels” (NIST, 2014, p. 9).
Many HPH organizations demonstrate security at Tier 1, or the Partial Level, which is mostly a reactive risk management program. However, the goal of the sector is to strive to meet the requirements of Tier 4, or the Adaptive Level. “Risk management is the ongoing process of identifying, assessing, and responding to risk in helping organizations understand the likelihood that an event will occur and the resulting impact” (NIST, 2014, p. 5). An Adaptive Level is based on predictive indicators, thereby making it an ongoing and proactive risk management program. With the sensitivity of the data transmitted and utilized throughout the sector, reaching an Adaptive Level is necessary for the HPH sector.
The NIST framework provides entities with flexibility but guides them through the implementation of effective cybersecurity postures. Organizations choose to handle risk by “mitigating, transferring, avoiding, or accepting the risk, depending on the potential impact to the delivery of critical services” (NIST, 2014, p. 5). However, accepting risk in the HPH sector is unacceptable due to the sensitivity and high value of the data with which it utilizes. Because the NIST framework provides entities with “flexible baseline standards for addressing cyber risks, rather than a comprehensive list of requirements, entities will need to determine how to implement the standards through concrete internal rules and protocols” (American Hospital Association [AHA], 2013, p. 12).
The HPH sector has yet to adopt a framework. “Of the sixteen critical infrastructure sectors, the HPH sector has not adopted NIST as their framework” (Finn & Chaput, 2017, 32:29). The adoption of NIST is recommended by the CENC, HHS-OCR, and AHA. The CENC (2016) believes its implementation should be better utilized and mandated by the Office of Management and Budget (pp. 19-20). HHS-OCR even drafted a document called “HIPAA Security Rule Crosswalk to NIST Cybersecurity Framework” (2016), which is available on the HHS-OCR website free of charge, to assist providers in applying the NIST framework to their HIPAA Security Rule requirements. Even though the implementation of the framework is voluntary in the HPH sector, the AHA recommends that providers “anticipate that the framework will likely be considered a de facto baseline for general cybersecurity compliance, and significant non-conformity with the framework may increase the likelihood of litigation” (AHA, 2013, p. 4).
Although many providers are still slow to adopt the NIST framework, it is the most commonly utilized framework. Symantec and HIMSS Analytics (2016) reported survey results which “showed it to be the most common methodology used for HIPAA assessments” (p. 3). While the NIST framework is being adopted by some providers, “many smaller businesses are unclear about how to use it” (CENC, 2016, p. 22). However, NIST published “Small Business Information Security: The Fundamentals” (2016) to assist SMBs with the utilization of the framework. This fundamental guide can also be applied to HPH SMB providers.
Health Information Trust Alliance
The Health Information Trust Alliance (HITRUST) was founded in 2007 to bring a common cybersecurity framework to the HPH sector. HITRUST believes a common framework is the “core pillar” to secure EHRs.
HITRUST exists to ensure that information security becomes a core pillar of, rather than an obstacle to, the broad adoption of health information systems and exchanges by addressing specific challenges such as concern over current breaches, numerous and sometimes inconsistent requirements and standards, compliance issues, and the growing risk and liability associated with information security in the healthcare industry. (HITRUST, 2017, p. 3)
The HITRUST framework focuses on both short-term and long-term needs for HPH sector cybersecurity. HITRUST advocates that “the best way to promote confidence in the security of electronic health information is for those who actually use technology to create, access, store and exchange electronic health information to create a common security framework to protect that information” (HITRUST, 2017, Policy Advocacy section, para. 1).
NIST and HITRUST are two critically significant frameworks which mirror each other. Both NIST and HITRUST “use a common language to address cybersecurity risk with cost-effective solutions based on business needs rather than regulations” (ICIT, 2016, p. 69). While NIST is adaptable to any sector of critical infrastructure, HITRUST, which is influenced by NIST, is HPH sector-specific. “HITRUST maintains a widely-adopted cybersecurity and privacy information risk and compliance management framework for the HPH sector that fully incorporates the NIST framework and provides for 135 individual security controls and 14 individual privacy controls” (DHS, 2016, p. 22). HITRUST makes their framework available to providers at no charge while promoting awareness, education, and training to the sector. HITRUST also offers a risk assessment tool like the ONC-HIT SRA tool. The HITRUST risk assessment tool, MyCSF, is available for qualified providers to download free of charge through their website.
Like the NIST framework, the HPH sector has not adopted the HITRUST framework. Unfortunately, HHS does not recognize HITRUST as meeting the requirements of HIPAA compliance. “HHS articulated they do not acknowledge and they do not recognize third-party certifications, such as HITRUST, as a substitute for HIPAA compliance nor as representative or indicative of a good housekeeping stamp-of-approval on the provider’s security program” (Finn & Chaput, 2017, 35:58).
The HIPAA Security Rule and the HITECH Act set broad and flexible legislative measures to protect and secure EHRs after the healthcare reformation. “However, none of the regulations comprehensively address the new environment. For instance, none of the regulations mandate that EHRs be encrypted while at rest or in transit” (ICIT, 2016, p. 42). Broad measures, such as these, attempt to incorporate every possible threat and attack in the past, present, and future without changing, while technology and threats change constantly.
Due to the constant changes, these measures require frequent updates. Without guidance, SMB providers are left confused. This confusion leaves patient privacy open to vulnerabilities. Symantec and HIMSS Analytics (2016) quoted Mac McMillan, Chairman of the HIMSS Privacy and Security Policy Task Force, saying, “you cannot have privacy without good data security” (p. 4). Cybersecurity is not a “one-and-done” task. It must continue to change and be updated due to the continuously-changing threat landscape, as demonstrated through the evolution of ransomware. Otherwise, at some point, the attacker finds a way around the security hurdle.
NIST and HITRUST, on the other hand, guide providers and organizations on the implementation of such measures; while advocating long-term proactive measures, coupled with short-term reactive measure and contingencies. “By developing a sustainable risk management program, organizations shift their security mindset from tactical and reactive to strategic, robust, and long-term” (Symantec, 2016, p. 4). These frameworks, however, are only voluntary. Although other frameworks cannot be used in substitution of HIPAA compliance standards, these voluntary frameworks can be utilized alongside HIPAA. Utilization of these frameworks by SMB providers will help strengthen their HIPAA compliance and create better quality postures. To become more secure, the HPH sector not only requires better quality mandated postures but enforcement of postures. The sector looks to its SSA, HHS, for the establishment of mandated proactive cybersecurity postures.
Enforcement
Cyberattacks are on the rise, especially those which advance future fraud schemes. As the financial sector hardened its systems, criminals moved to the unsecured HPH sector. Instead of only acquiring financial information, cyberattackers could acquire all PII. Stolen PII, such as a pack of just ten Medicare numbers, will sell on the black market for about $4,700 and advance future fraudulent activities (Bisson, 2015, para. 2). As of 2016, fraudulent activities, such as identity theft, were one of the “fastest growing threats in America” (Cybersecurity National Action Plan Factsheet, 2016, para. 3). Many of these nefarious activities are the result of insufficient and ineffective cybersecurity measures. “If fundamental cybersecurity and identity issues are not addressed, America’s reliance on digital infrastructure risks becoming a source of liability” (Cybersecurity National Action Plan Factsheet, 2016, para. 8).
The example of the evolutionary history of ransomware demonstrated how cyberattacks influenced growing threats, such as fraud and identity theft, through targeting EHRs. Those attacks progressively affected a variety of medical devices and record storage devices, thus threatening human lives. Furthermore, it demonstrated that current required postures, such as HIPAA, are inefficient, and “reactive security measures will not be effective in the long run” (Dunbrack & Hanover, 2014, p. 1).
Some providers believe the solution is to continue adding security measures. However, Symantec and HIMSS Analytics (2016) warned providers that “adding more security products and managing data security with after-the-fact tactical responses instead of proactive strategies” is not the solution (para. 4). This may even intensify problems and result in more financial consequences. Likewise, the implementation of more security products is not the solution to unethical providers who ignore postures, such as HITECH. Sjouwerman (2017) quoted ICIT Senior Fellow James Scott who found that “because ransomware is so common, [providers] are not reporting them all” (para. 5). Therefore, a lack of breach reporting can be attributed to a lack of quality postures and a lack of enforcement of those postures.
Awareness of cyberthreats and mandated implementation of quality postures requires proactive enforcement to reduce liability. The White House recognized that “attacking us online is often easier than attacking us in person” (Cybersecurity National Action Plan Factsheet, 2016, para. 3). This idea, coupled with the threat of compromising medical record storage devices and the possibility of compromising medical devices to physically attack a person through cyberspace, is reason enough to propose a restructure. This restructure must establish quality mandated postures and enforce proactive measures within the highly vulnerable and highly targeted HPH sector.
The Department of Health and Human Services
PPD-21 was released on February 12, 2013. It was written to advance the strength and resilience of national critical infrastructure by taking proactive steps to manage risk. As part of the directive, President Obama identified sixteen critical infrastructure sectors and sixteen SSA to oversee the risk management of their respective sector. “Each critical infrastructure sector has unique characteristics, operating models, and risk profiles that benefit from an identified SSA that has institutional knowledge and specialized expertise about the sector” (Obama, 2013, Sector-specific agencies section, para. 1).
PPD-21 identified the Department of Health and Human Services (HHS) as the SSA for the HPH sector. HHS “is responsible for managing and coordinating broad-based sector security and resilience activities” (DHS, 2016, p. 14). Specifically, HHS is tasked to “take proactive steps to manage risk and strengthen the security and resilience” of the HPH sector (Obama, 2013, Policy section, para. 1). By “considering all hazards that could have a debilitating impact on national security, economic stability, public health and safety, or any combination thereof,” HHS can “reduce vulnerabilities, minimize consequences, identify and disrupt threats, and hasten response and recovery efforts” in the HPH sector (Obama, 2013, Policy section, para. 1). As the SSA, HHS also has the authority to enforce HIPAA through the HIPAA Enforcement Rule.
HIPAA enforcement
The HIPAA Enforcement Rule was issued on February 16, 2006. “The HIPAA Enforcement Rule contains provisions relating to compliance and investigations, the imposition of civil money penalties for violations of the HIPAA Administrative Simplification Rules, and procedures for hearings” (HHS, 2017b, para. 1). HHS-OCR is tasked to handle the enforcement process. HHS-OCR “administers and enforces the HIPAA Privacy, Security, and Breach Notification Rules and conducts HIPAA complaint investigations, compliance reviews, and audits” (ONC-HIT, 2015, p. 7). HHS-OCR also retains the authority to impose civil penalties for non-compliance (ONC-HIT, 2015, p. 56).
HHS-OCR works closely with other agencies to assist in HIPAA enforcement. HHS-OCR “also works in conjunction with the DOJ to refer possible criminal violations of HIPAA” (HHS, 2017a, para, 2). When the DOJ receives referrals, the agency may investigate and prosecute criminal violations of HIPAA. State Attorneys General (SAG) may also “bring civil actions and obtain damages on behalf of state residents for violations of the HIPAA Rules” (ONC-HIT, 2015, p. 56). When a breach notification is required, HHS-OCR posts a list of the breached providers and the details of the incident on the website’s breach portal. After completion of the investigation and evaluation, HHS-OCR discloses what corrective actions were taken.
Although HHS-OCR takes part in compliance reviews and audits, these enforcement measures are mainly reactive measures because they are mostly conducted when a complaint is received or when a breach requires notification. David Holtzman, attorney and former senior advisor to HHS-OCR, stated:
The common denominator for many of the enforcement actions in OCR cases came about when investigations into the root cause of the breach affecting more than 500 individuals found systemic, often profound, failures of organizational programs to safeguard protected health information. And most often cited was a failure to perform an information security risk assessment or to have a risk management plan to address gaps in the safeguards for information systems, both required actions under the HIPAA Security Rule. (Holtzman, 2017, para. 9)
This further enforces the fact that many providers are not in compliance with HIPAA or are only in minimum compliance. It also demonstrates a lack of enforced oversight measures, thereby making HIPAA ineffective.
HHS-OCR has implemented a HIPAA Privacy, Security, and Breach Notification Audit Program, which is primarily a compliance improvement program. However, because the HPH sector does not mandate cybersecurity frameworks, such as NIST or HITRUST, HHS-OCR can only audit providers under HIPAA mandates and ensure the minimum HIPAA requirements. Essentially, because the requirements of HIPAA have proved to provide insufficient protections from cyberthreats, such as ransomware, HIPAA enforcement can never truly be sufficient.
Proactive enforcement proposal
To become effective and sufficient, HIPAA requires the assistance of provider awareness, quality mandated postures and frameworks, and stronger proactive enforcement. While many industry members recommend the creation of a single proactive cybersecurity oversight agency within the HPH sector, this option is costly to put into action. For example, the creation of DHS, the most recent and “the largest government reorganization undertaken since 1947,” cost $36.2 billion (DHS, 2004, p. 1). In addition, DHS requested an annual budget of $41.2 billion to operate in the 2016 fiscal year (DHS, 2016, p. 3). To fund the creation and operation of a new agency for proactive cybersecurity oversight, the HPH sector would be looking at similar costs. However, in their report “Enhancing National Cybersecurity Infrastructure” (2016), the CENC warns that “an increase in spending does not necessarily result in an increase in security” (p. 9).
Fortunately, agencies with the authority to conduct proactive oversight measures are already established in the HPH sector.The expansion of these agencies to incorporate proactive cybersecurity oversight divisions, will save the HPH sector in unnecessary costs. It will also create the necessary effective redundancy to ensure quality cybersecurity postures throughout the HPH sector.
Various oversight and investigating agencies exist within the HPH sector. These include, but are not limited to, the DOJ, HHS, HHS-Office of Inspector General (OIG), HHS-OCR, SAG, and state departments of health. These agencies work in some capacity to fight fraud and abuse in the HPH sector’s health programs, such as the Medicare and Medicaid programs. Furthermore, these agencies already have close working relationships with each other in conducting joint investigations. SAG, for example, retain authority to conduct proactive oversights and manage civil violations and criminal prosecutions. Therefore, expanding them with cybersecurity oversight divisions will assist in hardening the HPH sector’s security and resilience.
The HITECH Act gave SAG the authority to enforce HIPAA. Section 13410(e) of the HITECH Act provides SAG the authority “to bring civil actions and obtain damages or enjoin further violations of the HIPAA Privacy and Security Rules on behalf of state residents” (HHS, 2017d, para. 1). HHS-OCR and SAG already coordinate and collaborate with each other on these types of cases. HHS-OCR “welcomes collaboration with SAG seeking to bring civil actions to enforce the HIPAA Privacy and Security Rules, and OCR will assist in the exercise of this new enforcement authority” (HHS, 2017d, para. 3).
SAG coordinate with HHS and other federal agencies in Medicare cases, and they handle and collaborate with state agencies in Medicaid cases. While the HPH sector’s Medicare program is federally funded, the Medicaid program is state funded. By allowing the states to take over proactive cybersecurity oversight measures in the Medicaid program, HHS can focus its proactive cybersecurity oversight resources on the Medicare program. This leaves other state oversight agencies responsible for any other programs and provider types.
By doing this, the Federal government, state governments, and the HPH sector can establish better cybersecurity postures in their various healthcare programs. By expanding upon these preexisting oversight agencies, the HPH sector can conduct proactive cybersecurity evaluations at lower costs. The implementation of this proposal will result in a decline of attempted cyberattacks, and the HPH sector will no longer be one of the most vulnerable sectors of critical infrastructure.
For example, most SAG incorporate a Medicaid Fraud Control Unit (MFCU). These oversight units collectively recovered $1.8 billion in 2016 (Beaton, 2017, para. 2). MFCUs fight fraud and abuse within the HPH sector’s Medicaid program. MFCUs exist in the District of Columbia and every state except North Dakota. MFCUs have the authority to conduct reactive and proactive activities in the fight against fraud and abuse. Title 42 U.S.C. § 1007 (1999), Public Health; State Medicaid Fraud Control Units, “authorizes the Secretary to pay a State ninety percent of the costs of establishing and operating a State Medicaid fraud control unit for the purpose of eliminating fraud in the State Medicaid program” (p. 1,028). These units have been highly successful in combatting fraud reactively and would provide the sector with a starting point for initiating proactive cybersecurity oversight measures. Taking advantage of the expansion of these preexisting agencies would save the HPH sector in unnecessary costs.
The Louisiana MFCU, for example, has been the most consistently high performing unit in the nation. On August 15, 2013, Wendel and Lyons for USA Today reported that LA led the nation in recovered fraudulent Medicaid payments during the previous fiscal year (p. 4A). “The federal CMS reported that the LA recovery rate of nearly 2% of all Medicaid dollars spent was the highest of any state” (Wendel & Lyons, 2013, p. 4A). Furthermore, in a letter from Richard Stern of the Office of Evaluation and Inspections, to Fred Duhy, the former director of the LA MFCU, the Unit was nominated for the Inspector General’s Award for Excellence in Fighting Fraud, Waste, and Abuse for 2016 (Stern, 2016, para. 1). The LA MFCU recovered nearly $640 million between the 2010 fiscal year and the 2014 fiscal year, and the LA MFCU’s recoveries totaled $17,905,243 during the 2015 fiscal year (Stern, 2016, para. 2). The LA MFCU conducts reactive investigations and participates in proactive activities by providing fraud and abuse risk management training to LA Medicaid providers.
Each Medicaid provider is required to sign a provider agreement contract to provide Medicaid services. In the contract, Medicaid providers agree to provide enforcement and oversight agencies, such as MFCUs, with requested documentation for investigation and evaluation purposes. MFCUs find their authority in the Federal regulations governing the Medicaid Program (42 CFR 431.107) and in state regulations, such as the LA Medical Assistance Program:
These regulations require that all providers of service make available to the State and Federal Government, as well as State MFCUs, all records necessary to disclose the extent of services the provider furnished the patient.
Furthermore, since the MFCU conducts both law enforcement and health oversight functions and disclosure is mandated by law, there exists an exception to privacy requirements of HIPAA. See 45 C.F.R. 164.512 and 45 C.F.R. 164.501. (LA MFCU, 2017, para. 2-3)
Conducting proactive cybersecurity evaluations as a health oversight agency would assist in preventing fraudulent activity, and therefore would still be within the MFCUs jurisdiction.
In addition to providing requested documentation, the provider agreement contract would also require HHS to establish random penetration testing and risk management audits on providers. These audits would be conducted by enforcement and oversight agencies in the evaluation of cybersecurity postures implemented by providers or their third-party associates. By conducting proactive penetration testing and risk management audits on providers, HHS via MFCUs can ensure better cybersecurity postures throughout these HPH sector programs.
Some HPH sector providers may provide both Medicare and Medicaid services and therefore be evaluated by both HHS and MFCUs. Providers should treat the penetration testing audit as an attack. There will be a time when a provider is defending against multiple attackers. Providers with quality cybersecurity postures should be able to defend against multiple attacks. In this case of redundancy, one enforcement oversight agency may find a vulnerability that another agency did not. Therefore, redundancy in penetration testing audits ensures better quality postures. At the conclusion of the testing period, enforcement agencies would provide their analysis reports with the results and recommendations for improvement to the provider. These improvements may include an update to the best quality tools and processes available at the time of the evaluation to match changes in the threat landscape.
Providers with insufficient postures or discovered vulnerabilities would be allowed a predetermined period of time after the evaluation to address cybersecurity issues. After that predetermined period, the provider may be reevaluated to ensure compliance. If the provider does not address the cited issues within the predetermined period, enforcement oversight agencies may issue fines. Dunbrack and Hanover (2014) argue, though, that “providers think it is cheaper to pay the fines and other associated costs than it is to invest in a comprehensive security strategy” (p. 1). In this case, HHS would need to offer incentives to providers for complying with these new measures or risk steeper fines. “Incentives should always be preferred over regulation, which should be considered only when the risks to public safety and security are material and the market cannot adequately mitigate these risks” (CENC, 2016, p. 5).
Currently, HHS has not implemented any such proposed mandates. The SSA is currently conducting research on cybersecurity within other sectors. The hope is that other sector implementations may be applied to the protection of the HPH sector. HHS ordered the Health Care Industry Cybersecurity Task Force to conduct this research for the HPH sector.
Health Care Industry Cybersecurity Task Force
The Cybersecurity Information Sharing Act of 2015 ordered HHS, in coordination with DHS and NIST, to compile a team to analyze cybersecurity within the HPH sector and other industries. In response, HHS created the Health Care Industry Cybersecurity Task Force made up of experts in both government and private sector capacities (Public Health Emergency, 2016, para. 6). The goal of the Task Force is to “collectively look across industries and sectors to find the best ways organizations of all types are keeping data and connected medical devices safe and secure” (Wakefield, 2016, para. 7). According to Task Force member, Fred Trotter:
We are to investigate: What can the healthcare industry learn from other industries about cybersecurity? What are the special challenges that we face with cybersecurity in healthcare? What are the difficulties protecting EHR systems and networked electronic medical devices? What cybersecurity study materials should the healthcare industry be exposed to? How should an organization designed to coordinate the sharing of cybersecurity threats between healthcare industry players and the US Federal Government operate? Finally, we were asked to give Congress a written report summarizing all of the above. (Trotter, 2016, para. 2)
The Task Force’s report is expected sometime this year, as their term expired in March 2017, however it was not available at the time of this writing. The Task Force has actively sought public opinions from industry employees in assisting them on their mission. Another group they may seek guidance from is the Commission for Enhancing National Cybersecurity.
Commission on Enhancing National Cybersecurity
The Commission on Enhancing National Cybersecurity (CENC) conducted a similar analysis, which is not HPH sector-specific; but it addressed issues, particularly on restructuring, which may be applied to the HPH sector. “To the maximum extent possible, the burden of cybersecurity must be ultimately moved away from the end-user – consumers, businesses, critical infrastructure, and others – to higher-level solutions that include greater threat deterrence, more secure products and protocols, and a safer Internet ecosystem” (CENC, 2016, p. 5). The proposed implementation of proactive enforcement seeks to start this process. The responsibility of cybersecurity for the end-user SMB provider thus far has resulted in an unclear, confusing, “every man for himself” scenario. SMB providers are inexperienced or financially incapable of handling such a responsibility, and they require further guidance and assistance in these implementations.
The HPH sector sets broad, flexible, unclear, and confusing postures. The HPH sector’s “umbrella” agencies simply expect those providers, who have no knowledge or expertise in cybersecurity, to implement and “voluntarily comply” with these postures. “When it comes to cybersecurity, organizations cannot operate in isolation” (CENC, 2016, p. 2). And, the mandated postures provided continue to go unchanged to match the continuously-changing threat landscape. The HPH sector cannot enforce what is not mandated. Without the HPH sector coming together to implement better postures and some form of proactive enforcement of those postures, the HPH sector will be left in a reactive state and continue to remain vulnerable.
With HHS distributing cybersecurity enforcement to assisting oversight agencies, more assistance can be provided to HPH SMB providers on the implementation of better quality postures. This will bring the sector’s defenses together and create a more secure and resilient HPH sector. The CENC claims “the government is – and should remain – the only organization with the responsibility and, in most cases, the capacity to effectively respond to large-scale malicious or harmful activity in cyberspace” (CENC, 2016, p. 13). The proposed implementation of proactive enforcement seeks to move some of the responsibility from the end-user provider to entities that are more experienced and financially able to oversee and update security and resilience of the sector. This also allows HPH providers to revert their focus back to their main responsibility of providing quality healthcare.
The HPH sector must implement better proactive measures while continuing to maintain their reactive measures. “For now, technological advancement continues to outpace security and will continue to do so unless shifts in our cybersecurity strategies and how well we implement those strategies are made” (CENC, 2016, p. 3). The HPH sector “will be unable to shift the advantage in cyberspace away from attackers until we collectively recognize that continued dependence on reactive cybersecurity makes it easier for attackers to find compromised systems” (CENC, 2016, p. 26). The implementation of the proposed proactive enforcement of better quality postures will help move the HPH sector away from a reactive state and into a proactive state.
Discussion of the Findings
The purpose of this research was to examine the cybersecurity threats and postures of the HPH sector to bring awareness to SMB providers, and to propose to the HPH sector a restructure to ensure proactive cybersecurity standards. This research will answer the questions: What threats and challenges do SMB providers face? What low-cost/no-cost postures are available to defend against these threats? How should the sector restructure to handle these threats?
The government and the HPH sector, long ago, recognized the need for cybersecurity. However, valuable patient data remains vulnerable to cyberthreats. In addition, the government and HPH sector have failed to establish quality mandated postures, and proactive enforcement is nearly nonexistent. These implementations are required to secure vulnerable patient data and defend against current cyberthreats.
The example deep-dive examination into the evolutionary history of ransomware established the level of sophistication achieved by cyberthreats. Ransomware was identified as the greatest challenge the HPH sector faced in 2016, and providers must be prepared to defend against such sophisticated attacks in the future (Sjouwerman, 2017, para. 1). However, according to Finn’s statistics – that “over one-third of organizations are still only complying with key mandates or only implementing basic security controls” – the HPH sector, in its current state, is not prepared to defend against such sophisticated attacks (Finn & Chaput, 2017, 43:44).
The expectation of the growth in cyberattacks in the HPH sector existed since 2014 (SecureWorks Counter Threat Unit, 2014, para. 1). CGI (2015, p. 1) and Gomez and Konschak (2015, p. 2) reported multiple warnings from the FBI advising HPH providers to expect targeted cyberattacks – and ransomware threats specifically – to grow. Even with the provided warnings and industry statistics, the HPH sector still fell victim to these cyberattacks. ProofPoint, Inc. (2016, p. 9) provided analysis showing the growth of ransomware in 2016 (Figure 1); and FireEye produced analysis reported by Chong (2016, para. 9), which displayed the HPH sector as the top-affected industry of the Locky ransomware campaign (see Appendix A).
The 2016 ransomware attacks on large acute care centers were a wake-up call to the HPH sector causing these facilities to recognize the need for stronger cybersecurity postures. This research examined the challenges SMB providers face in implementing quality cybersecurity postures. The challenges they face include the change in attacker motives; the lack of implemented cybersecurity tools; the wide array of devices to protect, including medical devices; the lack of finances and expertise; and most importantly, the lack of quality mandated postures and proactive enforcement.
The analysis reported by Pajares and Oliver (2015, para. 1) for Trend Micro showed a “trickle-down effect,” where cyberattackers shifted targets in other industries. Attackers first targeted larger entities. Then, as the larger entities hardened their defenses, the attackers targeted SMB and those with little to no defenses. In the HPH sector, cyberattackers targeted the large acute care centers in 2016. Therefore, as those large acute centers harden their networks and systems, it is likely that cyberattacks will “trickle down” to the SMB providers.
The 2016 HIMSS Cybersecurity Survey provided further clarification regarding these challenges. The HIMSS survey analysis (2016, p. 2) demonstrated non-acute care providers (SMB providers) utilized a smaller array of security technologies than the larger acute care providers. HIMSS (2016, p. 2) attributed these results to the SMB providers potentially having relatively less financial resources than larger providers. Fewer financials also lead to fewer opportunities in employing cybersecurity experts to implement, manage, and maintain quality tools and architectures.
Medical devices are also identified as a “low-hanging fruit” of the HPH sector. This research identified instances of attackers targeting medical devices, such as pacemakers, and researchers manipulating medical devices, such as insulin pumps (ICIT, 2016, p. 10). This is evidentiary of medical devices possibly becoming one of the future targets of cyberattacks. The examination of ransomware demonstrated the malware’s ability to affect a multitude of storage devices, from Windows to Apple and from desktop to mobile. In addition, ransomware that is not operating-system-specific allows for even more attack opportunities through unsecured medical devices. The risk to medical devices is further increased by the lack of security postures mandated and the disagreement about implementation responsibilities between manufacturers and providers. Cybersecurity is a continuous process and, therefore, is the responsibility of both the manufacturer and the provider. These are significant vulnerabilities that must be addressed due to the critical risk to patient safety and human lives.
All these challenges arise from the lack of quality mandated postures and enforcement that provide opportunities for attackers to take advantage. Although mandated security requirements, such as HIPAA and HITECH exist, they remain unchanged and, therefore, outdated to effectively and sufficiently defend against these threats. Industry experts from Wafa (2010) to Finn (2016) have argued the inefficiency of HIPAA due to its “checkbox” requirements that are overly broad and flexibility, which cause more confusion than clarity.
For example, these mandated postures identify possible compliance without implementation of addressable standards. Because encryption is an addressable standard of HIPAA, it is not required. Furthermore, HIPAA’s level of encryption is flexible, making the minimum level of encryption sufficient for compliance. However, when skilled attackers can crack weak encryptions, the strongest levels of encryption available must be utilized and mandated.
The example of encryption, as the vaccine of the cybersecurity industry, can help prevent the compromise of data integrity even if intruders gain access to a system, but only when the strongest levels of encryption are implemented. Although, it is not absolute, encryption is an addressable standard which must become a required mandate as contingency if an intrusion occurs. In addition, because weak encryptions can be cracked, files must be considered insecure upon breach whether encrypted or unencrypted. If these mandates must stay broad and flexible, they must continuously stay up to date. For example, mandates must dictate to providers the implementation of the best encryption process available at the time. They must also mandate updates to these measures as better quality processes are developed to keep up with the continuously-changing threat landscape.
SMB providers who are compliant to the minimal mandated cybersecurity measures leave themselves vulnerable and more likely to be a target of cyberattacks. This claim is further supported by analysis conducted by Gomez and Konschak (2015, para. 5), which showed that unsecure SMB providers who transmit data to and from larger providing entities become a threat to those larger entities and the rest of the HPH sector. This is like someone with the flu going out into public potentially infecting others with which they come into contact. Minimum compliance also leaves SMB providers open to increased legal and financial consequences. Therefore, SMB providers must also continuously update their cybersecurity postures with the best available measures.
Because of the continuously-changing threat landscape, cybersecurity postures are not a “one-and-done” operation. The CENC (2016, p.8) and Symantec (2016, para. 1) recognized the reliance of outdated policies and standards, where data security and IT infrastructure is critical, by organizations, such as LDH/DHH and, in effect, SMB providers. Cybersecurity postures must continually mature and progress along with the evolving threats. HIMSS (2016, p. 1) found that only 23% of surveyed providers implemented an ongoing risk management program. The implementation of ongoing risk management programs will assist the HPH sector in making the shift from its current reactive state into a long-term proactive state.
However, HHS, as the HPH sector’s SSA, is slow in taking the necessary proactive steps directed by PPD-21. HHS only enforces minimum compliance of outdated HIPAA mandates, while the utilization of other quality frameworks, such as NIST and HITRUST, exist. Even though industry experts and the CENC (2016, pp. 19-20) recommend NIST or official adoption of a cybersecurity framework, the HPH sector is the only sector of critical infrastructure that has not adopted NIST (Finn & Chaput, 2017, 32:29). Furthermore, HHS does not accept implementation of the HITRUST framework as satisfying compliance with HIPAA (Finn & Chaput, 2017, 35:58).
The threats faced by SMB providers in the HPH sector is attributed to the lack of quality mandated postures, which also affects the lack of enforcement of those postures. The HPH sector cannot enforce what is not mandated. Because HIPAA is categorized by industry experts as being insufficient, the enforcement of these postures is also insufficient. This research, therefore, proposed a restructure to the HPH sector to take proactive steps, as directed in PPD-21, in the creation of better quality mandated postures to include the adoption of a cybersecurity framework and the implementation of proactive enforcement measures to ensure the protection of EHRs and PII.
The CENC (2016, p. 13) recommended that the government be responsible for handling cybersecurity incidents and oversight due to their size and resources instead of end-users, such as SMB providers. But, while some may call for the creation of a new agency to handle cybersecurity risk management incidents and oversight, research of DHS showed this option to be costly to the HPH sector. However, this research identified government agencies, which already exist, that have the authority to take on proactive enforcement measures of oversight. Therefore, instead of creating a whole new agency, this research proposed a restructure through the expansion of preexisting agencies with the capacity to enforce cybersecurity measures.
This research used the Medicaid program as its example. This research also identified a high-performing oversight unit, the LA MFCU, to assist in the implementation of this proposal. The LA MFCU is housed under the LA SAG, who already holds authority in conducting proactive enforcement activities. Not only does the LA MFCU hold enforcement authority, but they also hold oversight authority (LA MFCU, 2017, para. 2-3). The purpose of the LA MFCU is to fight fraud and abuse in the Medicaid program. Therefore, expansion into cybersecurity oversight in the fight against fraud and abuse is not outside of the Unit’s jurisdiction.
However, within the LA Medicaid program, providers are required to sign a provider agreement contract. In this contract, they agree to provide HIPAA-exempted government enforcement and oversight agencies with HIPAA-protected documentation that assists in agency investigations. This proposal would require the LA MFCU to coordinate with LDH/DHH and HHS in revision of the provider agreement contract. By signing the revised contract, providers would consent to proactive oversight measures and enforcement, which may include penetration testing of their systems. In return, the LA MFCU, in coordination with HHS and LDH/DHH, would agree to submit analysis reports to the provider at the end of the testing period. By signing the revised contact, the provider would also agree to pay any fines issued at the discretion of the SAG. In addition, the provider would also agree to implement any recommended updates based on the analysis report.
With the expansion of this high-performing unit, and in coordination with HHS, HHS-OIG, HHS-OCR, and LDH/DHH, the LA MFCU can implement proactive cybersecurity enforcement and oversight activities to assist the HPH sector in the fight against fraud and abuse. In coordination with HHS-OCR and the SAG, the LA MFCU can also issue civil violations and conduct criminal prosecutions, if necessary. By expanding the LA MFCU with a cybersecurity oversight division, they can assist HHS in constructing quality cybersecurity structure throughout the state.
MFCUs exist in the District of Columbia and every state except North Dakota. Therefore, if successful, the National Association of Medicaid Fraud Control Units (NAMFCU), in coordination with HHS, can expand this proposal to other states in need of better quality enforcement. The expansion of these divisions into every state MFCU provides HHS with a more cost-efficient solution to strengthening cybersecurity infrastructure around the country and throughout the HPH sector. Through these proactive enforcement measures, HHS, as the SSA, takes a giant leap forward in the fulfillment of PPD-21. In effect, this expansion also assists America’s goal in strengthening national cybersecurity resilience.
The change for quality mandated postures and enforcement of those postures have been recognized by many industry experts. However, lawmakers and HPH sector government agencies are negligent to the necessity of this change. Every entity partially becomes an IT company while utilizing cyberspace and connecting to the rest of the world. The HPH sector is potentially facing cyberthreats that could also affect human lives. Therefore, the HPH sector will not be able to afford the life and death risks associated with minimum “checkbox” cybersecurity standards while patient lives become threatened through cyberspace. Without mandated comprehensive long-term risk management programs, lawmakers and HHS create the “perfect storm” for HPH providers by allowing an environment that puts the data of nearly every individual at risk for attackers to take advantage. The HPH sector is one of those industries where the stakes are higher because of the effects these threats could have on people’s lives. In other industries, money can be returned, but in the HPH sector, lives cannot be replaced.
The HPH sector will never be secure without full provider participation, and participation requires mandates and enforcement of mandates. As the goals of providing better quality healthcare to Americans change, so too must the sector’s cybersecurity measures to protect those goals. That is, as data analytics become less retrospective and more predictive and prescriptive, so too must the cybersecurity to protect that data (CGI Group, Inc., 2015, para. 1). The HPH sector must take its own advice in this regard. This research demonstrated the necessity for the HPH sector to focus its security resources on better quality mandated postures and proactive enforcement to meet those predictive and prescriptive needs.
Future Research and Recommendations
This research showed the sophistication of the current threat landscape by looking at the greatest threat and challenge to the HPH sector. The example of ransomware and its effects on the HPH sector demonstrated the weak state of the sector. Its weak state can be attributed to a lack of quality mandated postures and therefore a lack of enforcement of those postures. Therefore, it is recommended that the HPH sector coordinate with lawmakers to create better quality mandated postures for the sector and create enforcement of those postures to ensure uniformity throughout the sector.
HHS must work with lawmakers to update and create better quality mandates that strengthen the sector’s cybersecurity and resilience. Because the threat landscape is continuously changing, lawmakers must also factor in the time necessary to regularly evaluate the mandates to ensure they continue to match the threat landscape. It is imperative that HHS and lawmakers also consider creating proactive solutions to the HPH sector’s cybersecurity challenges.
The adoption of a cybersecurity framework, or the development of a customized framework, for the HPH sector will help providers meet the revised quality compliance mandates of proactive solutions. HHS and lawmakers must come together to address the HPH sector’s current weak state and determine a target state to reach. Borrowing from the NIST framework, the HPH sector must strive to reach the Adaptive Level of cybersecurity and risk management. HHS, as the SSA, must start with the adoption of a framework and assist providers in its implementation, while also employing enforcement of these standards.
This research demonstrated the absence of law enforcement during cybersecurity incidents. Because law enforcement does not have the ability to intervene until after the incident has occurred, they must become more proactive to eliminate the possibility of a future attack. Therefore, it is recommended for HHS and lawmakers to employ mandates for proactive cybersecurity implementation by law enforcement and oversight agencies.
The CENC recommends that cybersecurity should be managed by the government, and industry members call for the creation of an entity whose sole purpose is cybersecurity oversight. However, by examining the creation of DHS, this research demonstrated the costliness of this option. Nevertheless, there already exist enforcement and oversight agencies with the ability to implement these proactive standards. Expansion of these agencies would save the HPH sector in unnecessary creation and operation costs of a new entity.
This research identified a successful and consistently performing agency with the authority to implement these proactive operations. It is recommended that the LA MFCU test this proposal by expanding their computer forensics section to include a cybersecurity compliance section. This proposal also recommends the LA MFCU to work with LDH/DHH and HHS on revisions to the Medicaid provider agreement contract to include consent to proactive quality assurance testing of revised cybersecurity mandates. If successful, it is recommended that Barbara Zellner of NAMFCU work with HSS to implement these expansions across all MFCUs nationwide. Implementations of better quality mandates, the adoption of a cybersecurity framework, and proactive enforcement of these postures will bring the HPH sector closer to reaching an Adaptive Level of cybersecurity. This proposed implementation will also assist the HPH sector in becoming more secure and resilient, thereby making national infrastructure more secure and resilient and meeting the directive of PPD-21.
Due to the limitations of this paper, future research would need to be conducted on the risks of vulnerable medical devices in the HPH sector. “In October 2015, Senator Bill Cassidy (R-LA) and Senator Sheldon Whitehouse (D-RI) proposed the Transparent Ratings on Usability and Security to Transform Information Technology (TRUST IT) Act of 2015. TRUST IT requires the ONC to institute a system to rate product security, usability, and interoperability” (ICIT, 2016, p. 69). The TRUST IT Act requires products to be rated and posted on the ONC website. In addition, this research asks Sen. Cassidy and Sen. Whitehouse to consider the implementation of a HPH provider rating system. Similar, to the Health Department’s rating system of restaurants, providers can be annually rated based on their cybersecurity and risk management infrastructure. This rating system would ensure confidence in patient privacy and information security.
Conclusion
The healthcare industry and the cybersecurity industry are two similar fields. The healthcare industry diagnoses, manages, and maintains the health of human bodies. Similarly, the cybersecurity industry analyzes, maintains, and secures the health of a network, or a body of technologies. These networks, made up of various devices, store and secure sensitive patient information and assist doctors in providing quality care to patients. These two industries must evolve in parallel.
The previous presidential administrations sought to change the healthcare industry. “Over the next 20 years, data analytics will play a powerful role; its greatest impact will be less retrospective (what happened), and more predictive (what might happen) and prescriptive (what could happen)” (CGI Group, Inc., 2015, para. 1). This research examined the threats and challenges, postures, and enforcement of cybersecurity in the HPH sector and proposed a restructure for a more secure and resilient HPH sector. This research demonstrated that as the healthcare industry becomes less retrospective and more predictive and prescriptive, the cybersecurity industry and methods to protect data analytics must follow. Therefore, cybersecurity in the HPH sector must become less retrospective and more predictive and prescriptive.
References
American Hospital Association. (2013). Cybersecurity and hospitals. Retrieved from http://www.aha.org/content/13/ahaprimer-cyberandhosp.pdf
American Recovery and Reinvestment Act of 2009, Pub. L. No. 111-5, § 3,002, 123 Stat. 115 (2009). Retrieved from https://www.gpo.gov/fdsys/pkg/PLAW-111publ5/pdf/PLAW-111publ5.pdf
Beaton, T. (2017, Mar. 8). Medicaid fraud control units recovered $1.8 billion in 2016. Retrieved from https://healthpayerintelligence.com/news/medicaid-fraud-control-units-recovered-1.8-billion-in-2016
Bisson, D. (2015, Sept. 24). Healthcare industry is four times more likely to be impacted by advanced malware than other industries. Retrieved from https://www.tripwire.com/state-of-security/latest-security-news/healthcare-industry-is-four-times-more-likely-to-be-impacted-by-advanced-malware-than-other-industries/
Breach Notification for Unsecured Protected Health Information Interim Final Rule, 45 C.F.R. § 160 and 164 (2009, Aug. 24). Retrieved from: https://www.gpo.gov/fdsys/pkg/FR-2009-08-24/pdf/E9-20169.pdf
Brenner, S. (2010). Cybercrime: Criminal threats from cyberspace. Santa Barbara, CA: Praeger.
CGI Group, Inc. (2015). Cyberprivacy and cybersecurity for health data: Building confidence in health systems. Retrieved from https://www.cgi.com/sites/default/files/white-papers/cgi-cybersecurity-for-health-data-white-paper.pdf
Chong, R. (2016, Aug. 17). Locky Ransomware Distributed Via DOCM Attachments in Latest Email Campaigns [Web log post]. Retrieved from: https://www.fireeye.com/blog/threat-research/2016/08/locky_ransomwaredis.html
Commission on Enhancing National Cybersecurity. (2016, Dec. 1). Report on securing and growing the digital economy. Retrieved from https://www.nist.gov/sites/default/files/documents/2016/12/02/cybersecurity-commission-report-final-post.pdf
Cybersecurity National Action Plan Factsheet. (2016, Feb. 9). Retrieved from https://obamawhitehouse.archives.gov/the-press-office/2016/02/09/fact-sheet-cybersecurity-national-action-plan
Department of Health and Hospitals. (2016, Apr. 22). Provider requirements [Special section]. General information and administration provider manual: Chapter one of the Medicaid services manual, 1.1. Retrieved from http://www.lamedicaid.com/provweb1/Providermanuals/manuals/GIA/GIA.pdf
Department of Health and Hospitals. (2017a). Enforcement Process. Retrieved from https://www.hhs.gov/hipaa/for-professionals/compliance-enforcement/enforcement-process/index.html
Department of Health and Human Services. (2017b). The HIPAA enforcement rule. Retrieved from: https://www.hhs.gov/hipaa/for-professionals/special-topics/enforcement-rule/index.html
Department of Health and Human Services. (2017c). HITECH Act Enforcement Interim Final Rule. Retrieved from https://www.hhs.gov/hipaa/for-professionals/special-topics/HITECH-act-enforcement-interim-final-rule/index.html?language=es
Department of Health and Human Services. (2017d). State Attorneys General. Retrieved from https://www.hhs.gov/hipaa/for-professionals/compliance-enforcement/state-attorneys-general/index.html
Department of Health and Human Services Office for Civil Rights. (2013). HIPAA administrative simplification regulation text. Retrieved from https://www.hhs.gov/sites/default/files/hipaa-simplification-201303.pdf
Department of Homeland Security. (2004). Fiscal year 2004 budget in brief. Retrieved from https://www.dhs.gov/sites/default/files/publications/FY_2004_BUDGET_IN_BRIEF.pdf
Department of Homeland Security. (2016). Fiscal year 2016 budget in brief. Retrieved from https://www.dhs.gov/sites/default/files/publications/FY_2016_DHS_Budget_in_Brief.pdf
Department of Homeland Security. (2016, May). Healthcare and public health sector-specific plan. Retrieved from https://www.dhs.gov/sites/default/files/publications/nipp-ssp-healthcare-public-health-2015-508.pdf
Ducklin, P. (2016, Oct. 18). Data-stealing CryPy ransomware raises the spectre of variable pricing for files. Retrieved from https://nakedsecurity.sophos.com/2016/10/18/data-stealing-crpy-ransomware/
Dunbrack, L. & Hanover, J. (2014, Nov.) Cybersecurity in healthcare. Retrieved from https://www.symantec.com/content/en/us/enterprise/white_papers/b-cybersecurity-in-healthcare-wp.pdf
Emergency Preparedness Requirements for Medicare and Medicaid Participating Providers and Suppliers Final Rule, 42 C.F.R. § 403, 416, 418, et al. (2016).
Exec. Order No. 13,335, 3 C.F.R. 24,059-24,061 (2004), Retrieved from https://www.gpo.gov/fdsys/pkg/FR-2004-04-30/pdf/04-10024.pdf
Exec. Order No. 13,636, 3 C.F.R. 11,736-11,744 (2013), Retrieved from https://www.gpo.gov/fdsys/pkg/FR-2013-02-19/pdf/2013-03915.pdf
Federal Bureau of Investigations Internet Computer Complaint Center. (2012, Aug. 9). Citadel malware continues to deliver Reveton ransomware in attempts to extort money. Retrieved from https://www.ic3.gov/media/2012/120809.aspx
Finn, D. & Chaput, B. (2017, Mar. 14). Operationalizing cybersecurity in healthcare: 2017 IT security and risk management [Video file]. Retrieved from https://www.symantec.com/about/webcasts?commid=236825&utm_campaign=communication_reminder_24hr_registrants&utm_medium=email&utm_source=brighttalk-transact&utm_content=title
Gallagher, S. (2016, March 29). Two More Healthcare Networks Caught up in Outbreak of Hospital Ransomware. Retrieved from http://arstechnica.com/security/2016/03/two-more-healthcare-networks-caught-up-in-outbreak-of-hospital-ransomware/
Giri, B. N. & Jyoti, N. (2006). The emergency of ransomware. Retrieved from http://citeseerx.ist.psu.edu/viewdoc/download?doi=10.1.1.169.5881&rep=rep1&type=pdf
Gomez, J. & Konschak, C. (2015). Cyber-security in healthcare: Understanding the new world threats. Retrieved from http://divurgent.com/wp-content/uploads/2015/03/Cyber-Security-Healthcarepdf.pdf
Hayashi, K. (2007, Feb. 13). Trojan.Archiveus: Technical Details. Symantec. Retrieved from https://www.symantec.com/security_response/writeup.jsp?docid=2006-050601-0940-99&tabid=2
Health Information Trust Alliance. (2017). About Us. Retrieved from https://hitrustalliance.net/about-us/
Health Information Trust Alliance. (2017, Feb.). Introduction to the HITRUST CSF. Retrieved from https://hitrustalliance.net/documents/csf_rmf_related/v8/CSFv8_1Introduction.pdf
Health Information Trust Alliance. (2017). Policy Advocacy. Retrieved from https://hitrustalliance.net/about-us/policy-advocacy/
Health Insurance Portability and Accountability Act of 1996. H.R. 104-736 (Conference report). 104th Cong. (1996). Retrieved from https://www.gpo.gov/fdsys/pkg/CRPT-104hrpt736/pdf/CRPT-104hrpt736.pdf
Healthcare Information and Management Systems Society. (2016). 2016 HIMSS cybersecurity survey. Retrieved from http://www.himss.org/sites/himssorg/files/2016-cybersecurity-report.pdf
Holtzman, D. (2017, Jan. 3). A 2017 Forecast for HIPAA Enforcement [Web log post]. Retrieved from http://www.databreachtoday.asia/blogs/2017-forecast-for-hipaa-enforcement-p-2349
Independence Hall Association. (1995). The story of Charley Ross. Retrieved from http://www.ushistory.org/germantown/upper/charley.htm
Institute for Critical Infrastructure Technology. (2016, Jan.). Hacking healthcare IT in 2016. Retrieved from http://icitech.org/wp-content/uploads/2016/01/ICIT-Brief-Hacking-Healthcare-IT-in-2016.pdf
Kleoppel, D. & Durdin, K. (2017, Feb. 9). Demystifying the NIST cybersecurity framework for healthcare [Video file]. Retrieved from https://www.symantec.com/about/webcasts?commid=236821&utm_campaign=communication_reminder_24hr_registrants&utm_medium=email&utm_source=brighttalk-transact&utm_content=title
KnowBe4. (2016). A short history and evolution of ransomware. Retrieved from https://www.knowbe4.com/ransomware
Leetaru, K. (2016, Mar. 29). Hacking hospitals and holding hostages: Cybersecurity in 2016. Forbes. Retrieved from http://www.forbes.com/sites/kalevleetaru/2016/03/29/hacking-hospitals-and-holding-hostages-cybersecurity-in-2016/#2b39136b3e2e
Levene, B., Yates, M, & Downs, R. (2016, Feb. 16). Locky: New ransomware mimics Dridex-style distribution [Web log post]. Retrieved from http://researchcenter.paloaltonetworks.com/2016/02/locky-new-ransomware-mimics-dridex-style-distribution/
Leyden, J. (2010, Sept. 1). Russian cops cuff 10 ransomware trojan suspects: Cybercrime gang allegedly raked in $16M. Retrieved from: http://www.theregister.co.uk/2010/09/01/ransomware_trojan_suspects_cuffed/
Louisiana Medicaid Fraud Control Unit. (2017). Medicaid provider records request letter. [Letter to providers]. Copy in possession of the Louisiana Medicaid Fraud Control Unit.
Namestnikov, Y. (2015). Kaspersky security bulletin 2015: Evolution of cyber threats in the corporate sector. Retrieved from https://securelist.com/files/2015/12/KSB_2015_business_threats.pdf
National Institute of Standards and Technology. (2014, Feb. 12). Framework for improving critical infrastructure cybersecurity. Retrieved from https://www.nist.gov/sites/default/files/documents/cyberframework/cybersecurity-framework-021214.pdf
Obama, B. (2013, Feb. 12). Presidential policy directive 21: Critical infrastructure security and resilience. Retrieved from https://obamawhitehouse.archives.gov/the-press-office/2013/02/12/presidential-policy-directive-critical-infrastructure-security-and-resil
Office of the National Coordinator for Health Information Technology. (2015, Apr.). Guide to privacy and security of electronic health information. Retrieved from https://www.healthit.gov/sites/default/files/pdf/privacy/privacy-and-security-guide.pdf
Pajares, P. & Oliver, J. (2015, Sept. 22). Business held for ransom: TorrentLocker and CryptoWall change tactics [Web log post]. Retrieved from http://blog.trendmicro.com/trendlabs-security-intelligence/businesses-held-for-ransom-torrentlocker-and-cryptowall-change-tactics/
Pena, A. (2016, April 6). How to deal with ransomware [Web log post]. Retrieved from https://blogs.technet.microsoft.com/office365security/how-to-deal-with-ransomware/
Phillips, C. (2016, March 29). Healthcare Industry Sees Increase in Malware Attacks. The National Law Review. Retrieved from http://www.natlawreview.com/article/healthcare-industry-sees-increase-malware-attacks
Polansky, R. (2017, Feb. 3). NBC2 Investigation: Medical records sold on the Dark Web. NBC2. Retrieved from http://www.nbc-2.com/story/34422480/nbc2-investigation-medical-records-sold-on-the-dark-web
ProofPoint, Inc. (2016). The ransomware survival guide: What every organization needs to know before, during, after an attack. Retrieved from https://www.proofpoint.com/sites/default/files/ransomware-survival-guide-cm.pdf
Public Health Emergency. (2016, Dec. 9). Health care industry task force. Retrieved from: http://www.phe.gov/preparedness/planning/CyberTF/Pages/default.aspx
Public Health; State Medicaid Fraud Control Units, 42 U.S.C. 1007 (1999). Retrieved from https://www.gpo.gov/fdsys/pkg/CFR-1999-title42-vol3/pdf/CFR-1999-title42-vol3-part1007.pdf
Robb, D. (2016). Your money or your life/files. Retrieved from http://cdn2.hubspot.net/hubfs/241394/Knowbe4-May2015-PDF/WhitePaper_Ransomware_KnowBe4.pdf?hsCtaTracking=8ed3768d-3e53-4a15-882e-94b0fd6bc071%7C19a59b96-460a-4ded-81d4-84a22020f345&__hstc=19315687.7490e7924ff984d0794d4120b68cd57f.1486317016396.1486471128186.1486480207631.3&__hssc=19315687.2.1486480207631&__hsfp=2169180631
Roberts, P. (2015, Oct. 22). FBI’s advice on ransomware? Just pay the ransom. Retrieved from https://securityledger.com/2015/10/fbis-advice-on-cryptolocker-just-pay-the-ransom/
SecureWorks Counter Threat Unit. (2014, Aug. 27). CryptoWall ransomware threat analysis. Retrieved from https://www.secureworks.com/research/cryptowall-ransomware
SecurityScorecard. (2016, Oct.). 2016 Annual healthcare industry cybersecurity report. Retrieved from https://cdn2.hubspot.net/hubfs/533449/SecurityScorecard_2016_Healthcare_Report_Final.pdf
Sjouwerman, S. (2015, May 26). Is your network infected with sleeper ransomware? [Web log post]. Retrieved from https://blog.knowbe4.com/is-your-network-infected-with-sleeper-ransomware
Sjouwerman, S. (2017, Mar. 25). Ransomware is skyrocketing, but where are all the breach reports? [Web log post]. Retrieved from https://blog.knowbe4.com/ransomware-skyrocketing-but-where-are-all-the-breach-reports
Stern, R. (2016, May 10). Nomination for the Inspector General’s Award for Excellence in Fight Fraud, Waste, and Abuse; 2016 Honor Awards. [Letter to Fred Duhy]. Copy in possession of the Louisiana Medicaid Fraud Control Unit.
Symantec. (2014, Aug.) Symantec intelligence report: August 2014. Retrieved from http://www.symantec.com/content/en/us/enterprise/other_resources/b-intelligence_report_08-2014.en-us.pdf
Symantec & Healthcare Information and Management Systems Society Analytics. (2016). Addressing healthcare cybersecurity strategically. Retrieved from https://img03.en25.com/Web/Symantec/%7B7ed5a2f6-12fa-4e09-a318-3772a3578197%7D_Addressing_Cybersecurity_Strategically_whitepaper.pdf?aid=elq_10752&om_sem_kw=elq_16884759&om_ext_cid=biz_email_elq_
Symantec & Healthcare Information and Management Systems Society Media. (2016). Cybersecurity in healthcare: Why it’s not enough, why it can’t wait. Retrieved from https://www.symantec.com/content/dam/symantec/docs/infographics/symantec-healthcare-it-security-risk-management-study-en.pdf
Trotter, F. (2016, Sept. 13). Cybersecurity Check In [Web log post]. Retrieved from http://thehealthcareblog.com/blog/2016/09/13/cybersecurity-check-in/
Wakefield, M. (2016, Mar. 16). The health care industry cybersecurity task force [Web log post]. Retrieved from https://wayback.archive-it.org/8315/20170119032808/https://www.hhs.gov/blog/2016/03/16/healthcare-industry-cybersecurity-task-force.html
Wafa, T. (2010, Feb. 3). How the lack of prescriptive technical granularity in HIPAA has compromised patient privacy. North Illinois University Law Review, 30(3), 531-551. Retrieved from https://ssrn.com/abstract=1547425
Wendel, T. & Lyons, D. (2013, Aug. 15). State-by-state. USA Today, p. 4A.
Winton, R. (2016, Feb. 18). Hollywood hospital pays $17,000 in bitcoin to hackers; FBI investigating. LA Times. Retrieved from http://www.latimes.com/business/technology/la-me-ln-hollywood-hospital-bitcoin-20160217-story.html
Appendix A – Locky Ransomware Top Affected Industries
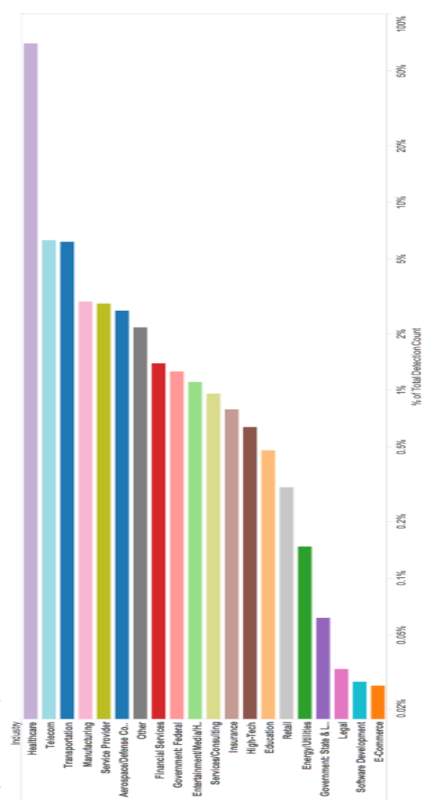
Figure 2. Locky ransomware top affected industries (Chong, 2016, para. 1).
Cite This Work
To export a reference to this article please select a referencing stye below:
Related Services
View allRelated Content
All TagsContent relating to: "Healthcare"
Healthcare is defined as providing medical services in order to maintain or improve health through preventing, diagnosing, or treating diseases, illnesses or injuries.
Related Articles
DMCA / Removal Request
If you are the original writer of this dissertation and no longer wish to have your work published on the UKDiss.com website then please:




