Cloud Computing: Models, Applications, Advantages and Disadvantages
Info: 11920 words (48 pages) Dissertation
Published: 30th Nov 2021
Abstract
Cloud computing is the upcoming future of technology as it leverages round-the-globe processing, storage and subsequent retrieval of data.
It takes the power of computing away from the client and hence enables easy access on thin clients (mobiles, PDAs, tablets). Also, it offers services to end users as well as environment to developers to customise applications and deliver solutions. Cloud gives freedom to users to access their data from anywhere in world and also facilitates exchange of data between networks through Inter-cloud. In the advent of smartphones and technology driven devices, cloud computing also plays a pivotal role in the IoT (Internet of Things). IT industry has realised the cost effectiveness and scalability aspect of cloud and have appointed various cloud service providers to be the custodians of their data.
Table of Contents
Introduction
History of Cloud Computing
Virtualisation
Cloud Management
Cloud Architecture
Cloud Servers Models (IAAS, PAAS, SAAS)
IAAS (Infrastructure as a Service)
PAAS (Platform as a Service)
SAAS (Software as a Service)
Types of Cloud Deployment Models
Private Cloud
Public Cloud
Hybrid Cloud
Community Cloud
Reason for Cloud usage
Applications of Cloud Computing
Impact of Cloud Computing
Security in Cloud Computing
Latest Development/Trend in Cloud Computing
Advantages and Disadvantages of Cloud Computing
Discussed Papers
Paper 1: Mobile Cloud: Advantage, Disadvantage and Open Challenge [20]
Paper 2: Cloud Computing Applications for Smart Grid: A Survey [21]
Paper 3: DDoS attacks in cloud computing: Issues, taxonomy, and future directions [22]
Paper 4: Cloud Computing Research and Development Trend [24]
Conclusions
References
Introduction
Cloud computing is an evolving technology for the future with rising demands on providing the data centres to the organisations. Cloud computing connects computers through internet and sharing the computer resources provided by the cloud providers. The cloud itself defines that data is saved somewhere where we can access it using a computer device and internet together rather than stored on some desktop or flash drive. Cloud computing is a rising technology for the trend and also a solution to many organisations irrespective of the fact that it’s a startup company or big IT firm. IT industry is expanding and migrating their data on Cloud with the implementation of Cloud computing with the facility of pay as you use that means users are required to pay for the resources on the basis of usage.
Cloud is a blessing for small organisation to deal with administration of large data with less cost,but it also has certain disadvantages such as security and privacy.
Similar to electricity, cloud computing allows organisations to devour resources. Cloud computing provides a platform to access of applications through internet rather than on a physical computer or server in the same building. It is rising in popularity with good cost efficiency ,elasticity, throughput ,scalability and delivers online business.
With all the ease, reduced hardware and maintenance cost, convenience around the world, flexibility and automated process where the clients need not be concerned about the software updates. It is being used by large industries like Google, IBM, Microsoft , and Amazon.
History of Cloud Computing
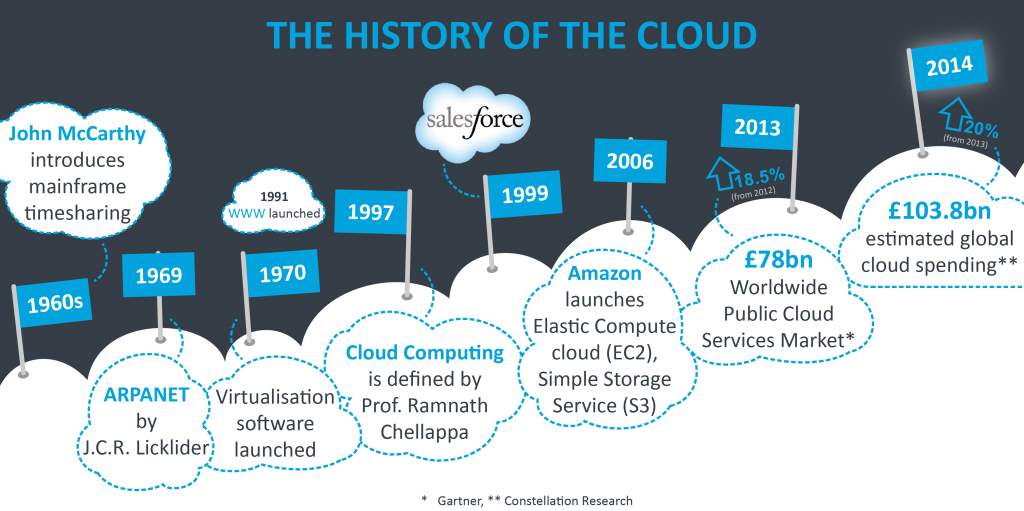
Figure3: History of Cloud Computing [1]
Cloud came into existence in 60s, so it is not a new technology. Grid Computing, Software as a Service, Application Service Provision and Utility computing are the evolvement stages of the cloud. Business technology can be revamped with the help of internet and cloud computing.
Early 60s: John McCarthy brought expensive mainframes for organisations to use.
In 1969 - 1970: developed ARPANET to connect the world and provide access to data from anywhere anytime. Virtualisation evolved which used VM software and enabled different computers to run on one Operating system.
In 1997: Term cloud computing was used.
In 1999: Plain websites started the concept of Salesforce.
In 2003: Hypervisor became the next generation.
In 2006: Pay as you go and EC2 Elastic Compute Cloud and Amazon S3 became the practice.
In 2008, 2009: Microsoft Azure and App Google Engines.
In 2013: IAAS- Market service grew faster with it.
In early 60s and 70s, supercomputers including all the software, printers, storage devices were usually used by the people that were really expensive.
Furthermore, in the beginning of 80s, mainframe computers were rising in demand for personal use, came into picture paving the way for low costs. Virtualisation in mainframe computing is highly utilised. Several users share the whole system with each physical server hosting the several other virtual machines VMs, each VM running OS consisting of its own storage space, CPU utilisation and network.
In the late 80’s and into the year 2000, the trade started a massive swing to distributed computing with small servers (compute devices). Each server comprises of more memory, CPU, and storage than mainframe. After 20 years of installing innumerable smaller servers across millions of data centers, computer resources and management in the organizations to cloud providers. The cost of maintaining the system is really high according to the performance of cloud. With the leap of development in technology, the industry is undergoing over-distribution of computer resources where large network servers have more throughput than required with lots of idle time.
With the consolidation of the computing, we can amalgamate the data centers , server at one place on cloud and provide access to the organisations and save cost to improve IT industry. The consolidation of server farms and data centers is in full swing both as a cost savings measure but also to better focus an organization’s IT staff. Some organizations have come to the understanding that they have enormous IT resources and expenses that could well utilized to emphasis on main customer-oriented facilities moderately than a huge IT department that might be better to outsource. This will ultimately reduce the operational and management costs. Some data centers are now using different sources of energy, unconventional air handling systems and other “green” energy technologies to enhance the normal power system.
Virtualisation
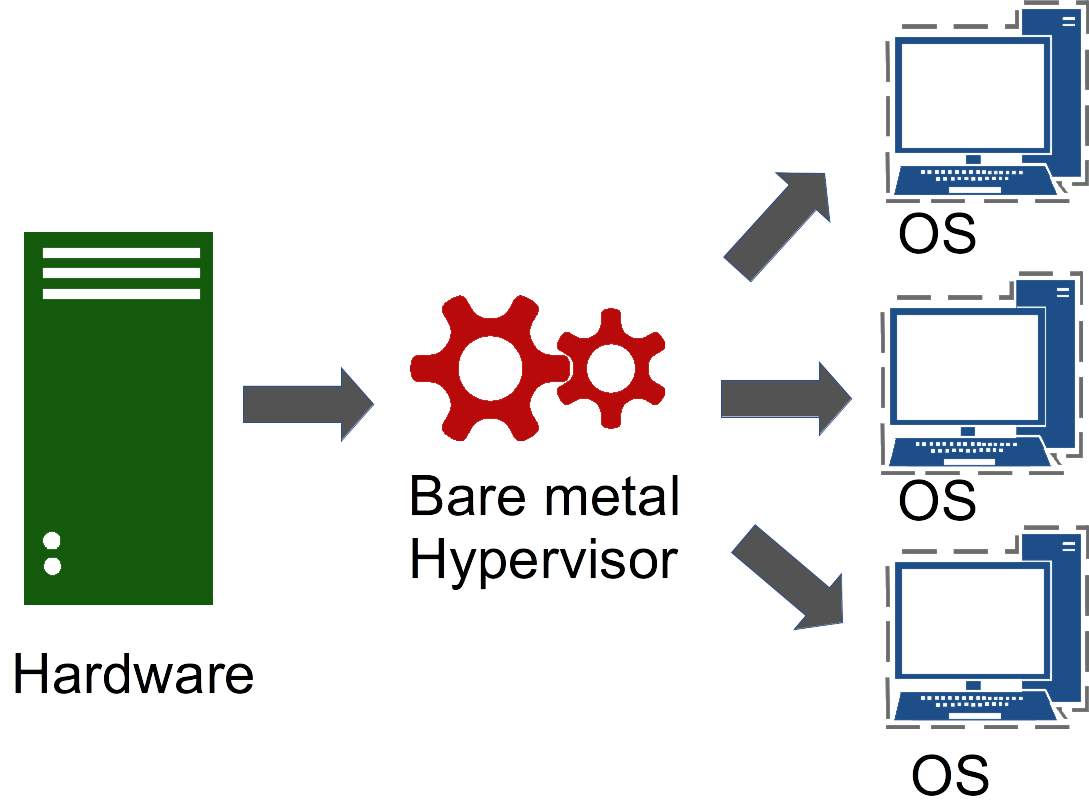
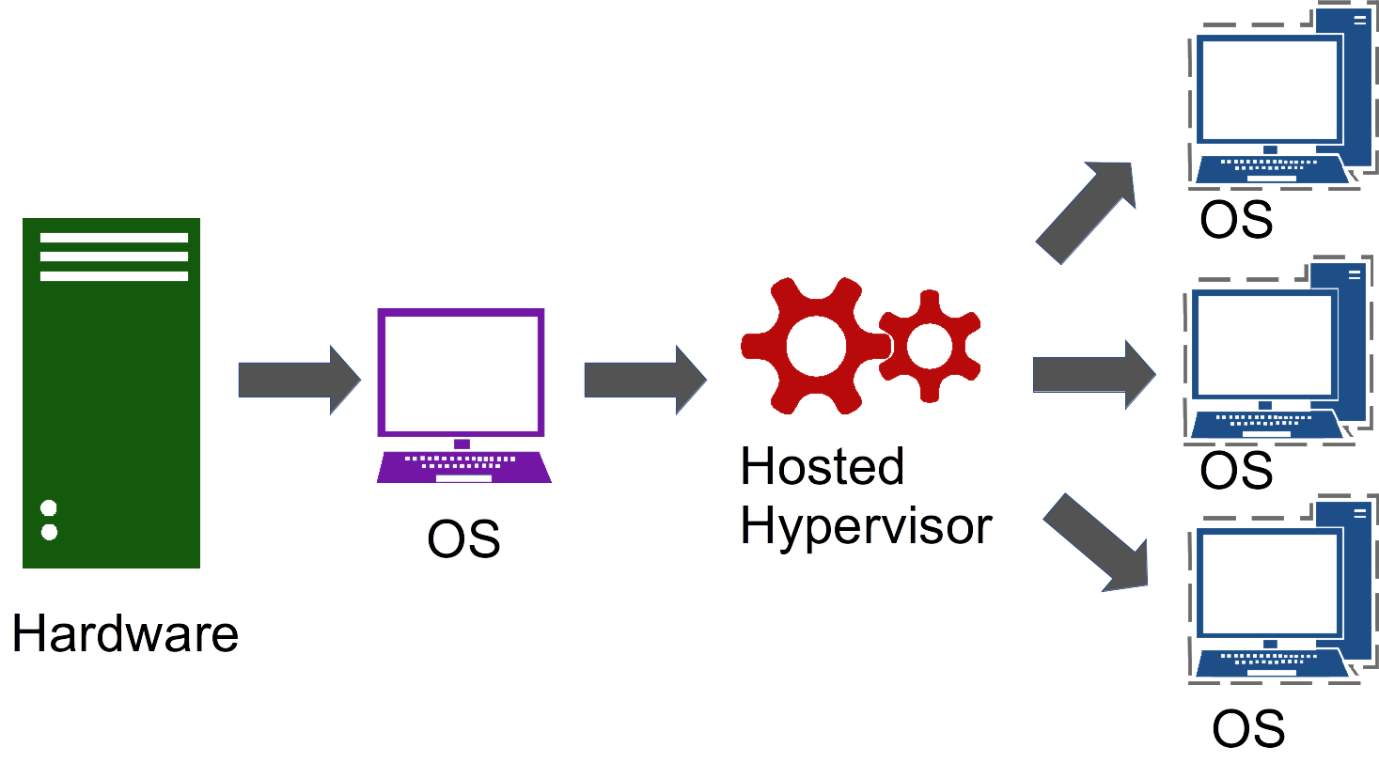
A virtual hardware in combination with virtualization helps in running cloud computing on a actual machine. The entire system will act as a single operating system, thus enabling several computers to work on a large computer.
Virtual machine acta as a software which works exactly like any other physical computer. It can also work on any physical system, with other VM’s working on it at the same time, distributing the workload of VM’s on several different CPU’s and memory.
In this process, all the VM’s act as a duplicate computer having its own software and operating system. One of the example of search a scenario can be 2 VM’s, one with ubuntu and windows will run on physical computer. Each VM will look as its own real computer. There are different forms in which virtualization can be done desktop, storage, server and networks.
http://www.ijcttjournal.org/Volume12/number-4/IJCTT-V12P132.pdf
Virtualization technology is hardware reducing cost saving and energy saving technology that is rapidly transforming the fundamental way of computing [2].
Server virtualization method used by hypervisors avoids some of the physical restrictions that each server can encounter. Virtualization permit software to hoax a physical server into thinking it is multiple server, and consequently capable of illustrating that server don’t execute on complete capacity. Therefore, increasing the number of server would grow the demands of higher traffic and compute loads. More storage space is desired for companies who has higher number of clients due to which they need more storage devices. We cannot overlook the rising demands of storage space. In case of any failure of computer resource, cloud computing systems require double the number of storage devices to preserve all its clients’ information. Cloud system must create a replica of all its clients’ data and store it on other devices. The copies created by this redundancy permits the central server to acquire backup machines to save that data. Hypervisors are of three types:
1. Native hypervisors
It runs on the bare metal server with absence of middleware Operating but solely responsible for the performance and consistency.
http://training.nectar.org.au/package01/sections/virtualization.html
2. Embedded hypervisors
It is integrated into a mainframe on a discrete chip to refine performance of server.
3. Hosted hypervisors
These run as a separate software layer above both the hardware and the OS used for private and public cloud.
Cloud Management
Cloud administration programming can help by dealing with all components of a cloud stage; physical and virtual assets. It enables associations to transform customary equipment into a cloud stage via mechanizing and streamlining the arrangement while overseeing and provisioning those assets fittingly. Thusly, specialist co-ops take full advantage of their speculations and endeavor the development chances of cloud administrations. The advantages are as follows:
- Speedy time to conveyance. Clients require adaptability that can’t be conveyed quickly without arranged, self-benefit provisioning. Today’s existence is that it is snappier and simpler for a client confronting a surge popular for a web application to hand over a Mastercard and change suppliers than to sit tight for their current supplier to increase limit. Cloud administration makes conveyance moment, so your clients aren’t enticed away.
- Adaptability isn’t about on-request provisioning. Be light sufficiently footed to arrangement precisely what the client needs; CPU, memory, circle space or system/design and how the client needs them apportioned. The client can control precisely what they require through self-benefit provisioning and maintain a strategic distance from exorbitant equipment circumstances by paying for what they require, when they require it.
- Expect ROI in days. Utilizing cloud administration programming appropriately, offering a light-footed arrangement and fast reaction that arrangements the cloud stage will spare cash while presenting new income streams.
- Cloud administration gives granular perceivability and control over which assets clients can really utilize. By utilizing metering, you can check how data transmission, systems and circle I/O, for instance, are being utilized. Before cloud administration, there was no chance to get of knowing how expenses were mounting. Presently you can charge clients for what they are utilizing.
- Upper hand through provisioning control. While not each specialist co-op will need to offer self-benefit provisioning, the usefulness is as yet essential and can’t be offered without cloud administration. A few organizations will need to uphold ‘designation control’ where a few people can arrangement servers on-request, while despite everything others have to demand it. This is an upper hand.
By using cloud administration, you will have the capacity to keep pace with the mechanical scene as they offer market separation and also guaranteeing income and new income streams through consultancy and new business benefit models.
Cloud Architecture
The most trending technology in the world is Cloud Computing nowadays. Many IT firms are using cloud to improve their client relationship. All the large and small companies are widely using cloud. Internet is the network medium which provides cloud service.
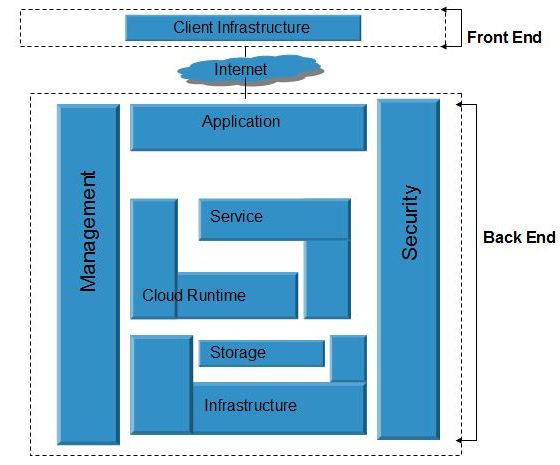
Figure : Architecture of Cloud computing in Graphical view [3]
Cloud Architecture is divided into two sections:
- Front End
- Back End
Front End
The front end is seen or accessible by the user of the computer. Computer network is required to access the system of cloud which is a part of front end. Cloud computing systems doesn’t have the similar user interface. Facilities provided by Web-based e-mail programs control existing Web browsers such as Internet Explorer or Firefox. Other systems have exceptional applications that offer network access to consumers.
Back End
The back end is the “cloud” unit of the system encompassing various resources like computers, servers, virtual machines and data storage systems to distribute cloud computing services. It includes any program like to process the data to video games. Generally, one dedicated server is assigned for an application who manages the system, monitors traffic and client demands to guarantee everything runs effortlessly. There are certain protocols and hypervisor ,a firmware which acts as virtual machine monitor which permits instance of cloud resource network to connect with each other.
Cloud Servers Models (IAAS, PAAS, SAAS)
Cloud is built on datacenters, integrated with different network. Cloud is a layered structure with three types of cloud service delivery models. Figure below all the layers of Cloud as a service. Virtualized physical resources, virtualized infrastructure, with virtualized middleware platforms and business applications are provided and used as services in the Cloud [26]. Security must be maintained for the Cloud clients and providers.
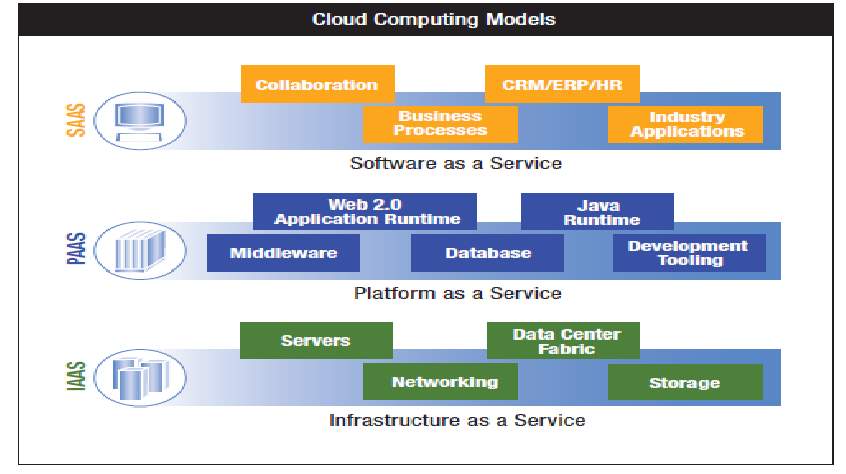
Figure: Layered Model of Cloud based services [4].
IAAS (Infrastructure as a Service)
Infrastructure as a service (IaaS) can be defined as the process of sharing the hardware resources for the execution of services using virtualization technology. AWS is one of the IaaS provider which helps in supporting virtual server instance and storage, along with API’s which allow users/customers to shift workload to a virtual machine. Users have the permissions to start/stop the access, install/uninstall the space as per their requirement. Based on users need, cloud providers offer different sizes of compute optimized instance for various type of workload requirement.
Since this service is called as the Infra structure layer it is also called as the Virutalization layer. In this layer it creates the pool of virtual machines which can used to store and access the software.These virtual machines are used to create and destroyed according to the user’s requirement. This service allows users to access the servers and storage infrastructure in a centralized service [4] [5] [6]
Various components of infrastructure such as storage, virtualization, networking etc can be outsourced with the help of IaaS models to any cloud provider.
With the help of OS images and application software installation we can deploy our applications on cloud. Installation of application software and OS maintenance, upgradation and patching is done by user. The cost of resource will be generated by the provider of cloud on the basis of consumption and usage.
For an instance, virtual machine can be created on Azure Microsoft Windows , can be utilized according to the requirements with facility to pay as you use.
Below figure shows the creation of VM for hosting WCF. [5]
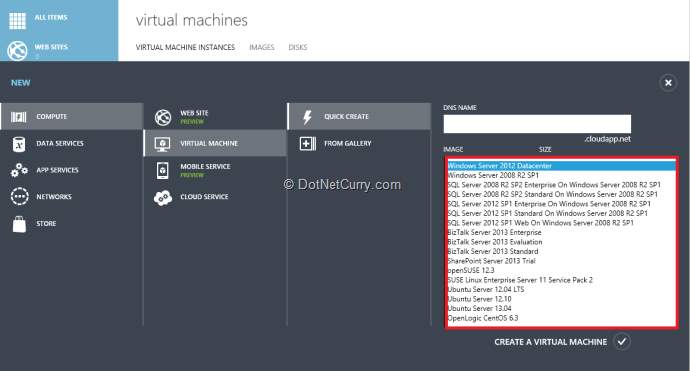
For example, using Microsoft Windows Azure, you can set up new Windows Server and Linux virtual machines and adjust your usage as your requirements change. You only have to pay for the service that you use. Below is a snapshot of Windows Azure services from windowsazure.com.
PAAS (Platform as a Service)
It provides the server or database platform for the user to run and execute the application using programming languages maintained by the providers on cloud infrastructure. Users can do the changes by the tool provided by the providers using Internet. PAAS provides OS Platform with certain tools for configuring the application to increase the demand. It automatically upgrades the hardware and software and releases the user from installing it.
In brief, it provides the hardware and software platform where the user can directly jump in and start the work . However, for deploying the tool ,one requires lot of hardware like database, web servers, to be installed on the machine for the setup of the application.
It also offers team to collaborate on work. PAAS merchants such as Salesforce.com gives CRM (Customer Relationship Management) platform for development and management.
The main drawback of PAAS is user is dependent on the platform and infrastructure of the provider. User need to change the programming language if it’s not supported by the provider.
Most importantly the server uptime and price has the key role.
SAAS (Software as a Service)
SAAS is packaged software with need of maintaining the software and managing the hardware ,it is just using the hosted software on the Internet. For example , bank who is giving us reliable service where the information of customers are kept secured, nobody can access their details without the permission. It lessens the effort of the clients to install the software, set it up and maintain their updates. SAAS is suitable for Customer Relationship Management, banking, healthcare. SAAS Providers accomplishes access to the application with security and performance.
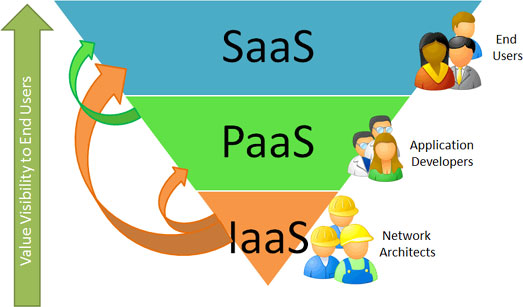
Below Figure1 [5] represents the hierarchal structure of the Cloud where Apps are part of SAAS, OS for PAAS and hardware in IAAS. IAAS is the bottom layer with PAAS as the middle layer and SAAS with the topmost with all the running applications.
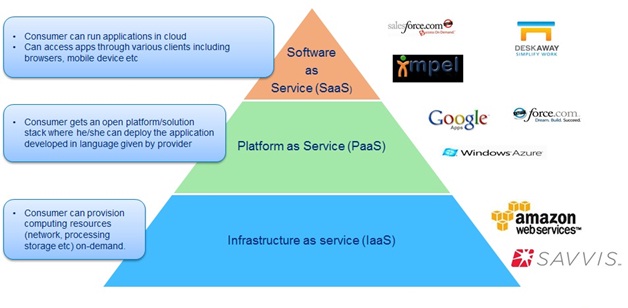
However, Figure2 [2] represents the role of companies in cloud, very less people were required for the hardware at IAAS level, few more companies than above created application on OS in PAAS level and last but not the least SAAS has the most developers and companies associated to create numerous applications.
Types of Cloud Deployment Models
Private Cloud
Most of the Organisations privately uses the given data center infrastructure consisting of hardware and software which is referred to as Private Cloud. Those data center are not shared with other organisations and called as on-premises or off-premises. Virtual Private Cloud is known as shared datacenter. Private cloud is quite expensive as it is single company owned data center so it is used by large companies. It is more secured and assets are kept within the firewalls with an advantage to companies to have full control of their data. It also has a drawback that it needs on premises software on the location of the company rather than the cloud over the internet. One of the best examples of a private cloud is Eucalyptus Systems [6].
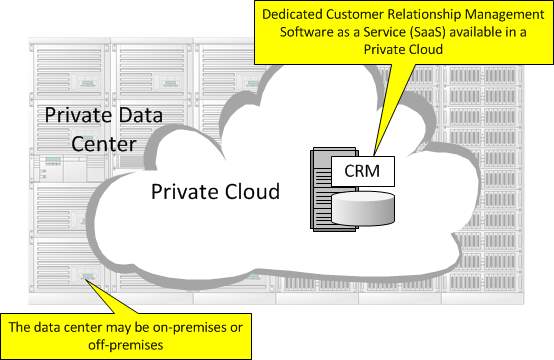
Figure: SAAS, Customer Relationship Management to demonstrate a Private Cloud
http://www.service-architecture.com/articles/cloud-computing/private_cloud.html
Public Cloud
Internet itself is defined as Public cloud. Cloud Service providers access internet to build applications and storage on Public Cloud. Public Cloud is really cheap as all the expenses of hardware, application is shielded by provider. Its uses model of pay as per use, so its charged as per the usage of the user. It is generally not suitable for the all the organisations due to security as they can store their sensitive data on it. It could be termed as storage as a service. Examples of a public cloud include Microsoft Azure,Google App Engine.
Its about sharing the data center among multiple organisations as the data center is off premises.
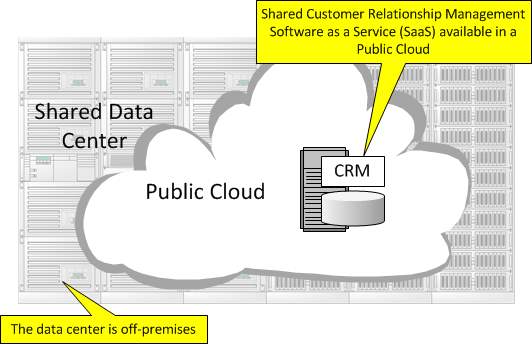
Figure: CRM, SAAS to illustrate a Public Cloud
http://www.service-architecture.com/articles/cloud-computing/private_cloud.html
Hybrid Cloud
Amalgamation of private cloud and public cloud. It is combination of multiple clouds where they are carrying out different functions within the same firm. This let the organizations to accumulate protected or fortunate data on a private cloud, while absorbent the facility to control resources from the public cloud to run applications that depend on this data. Thus, an organisation can increase their productivities by using public cloud services for all non-sensitive processes, trusting on a private cloud when they need it and confirming that all of their stages are impeccably integrated. This preserves data exposure to a bare minimum since they’re not stowing sensitive data for long-term on the public cloud. Example of Hybrid Cloud is Cloud Bursting.
The strong advantage of a hybrid cloud model is taking on-premises, private infrastructure which is accessible immediately than public cloud services. Furthermore, it reduces access time and latency. Hybrid clouds offers the benefits of scalability, reliability, security, cost efficiency, rapid deployment and potential personal savings of public clouds with all the security and increased control and management of private clouds. An example of a Hybrid Cloud includes Amazon Web Accommodations (AWS) [7] [8].
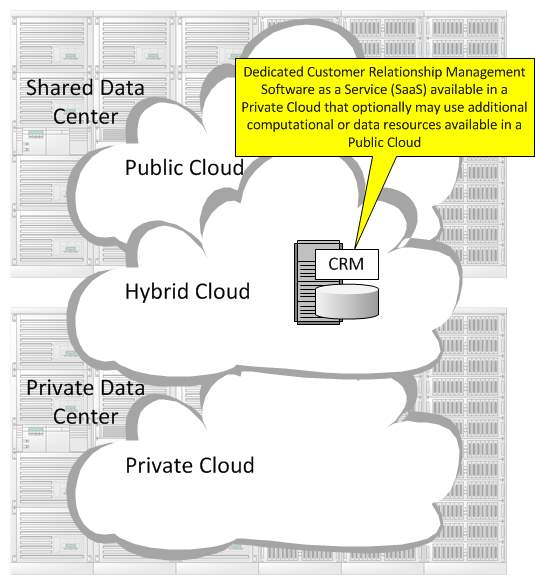
Figure: Customer Relationship Management (CRM) Software as a Service (SaaS) to illustrate a Hybrid Cloud.
http://www.service-architecture.com/articles/cloud-computing/private_cloud.html
Community Cloud
The organisation with same business requirements uses private community cloud of diverse government works within a definite sector. They endeavor to accomplish a comparable level of security control and oversight as those given by private mists while attempting to offer a portion of the cost efficiencies offered by open mists.
Reason for Cloud usage
Even though, there are many reasons for the rise of Cloud Technology in the IT industry, the major reasons for cloud emergence are listed below [9].
- Rapid evolution of computer and communication technologies: Industrial growth in computing and computing devices, and in the data communication pave the way to the incredible growth of cloud technology since the delivery of the work is slow, unavailability of people, high capital expenditure is becoming the burden for the organisations. Cloud helped removing these obstacles by introducing the datacentre for the business to adapt the technology with less spending. Cloud services benefit to sustain resourceful staff so as to makes intellect for your business.
- Maintaining Business and capital: Capital can be protected as keeping investment and costs to a minimum can be very significant to small and medium businesses identically. Earlier, most of the organizations used to save their data manually or stored their data in on premise structure. But to meet the global capability, most of the organizations want to exploit their time to advance the business, and prepared to outsource their IT prerequisite. Purchasing cloud services, also in a single application form like Salesforce.com or their complete datacenter is more cost effective, more consistent and allow them to move their limited resources in order to mount their business.
- Scale up business and access from anywhere: Industries that have top seasons or different seasonal employment demands can profit from cloud services by allowing them provisionally more volume for the regular business high time, without acquiring the hardware or software that would then go vacant during the slower times of the year. Users can access applications and data anytime and anywhere with the help of internet.
Applications of Cloud Computing
Cloud Computing is one of the foremost field of computing resources online since distribution and managing of resources in cloud is easy. Such features have made it an advantageous in the following fields: –
- E-Learning is a latest mania in the arena of education that offers an appealing environment for students, faculty members, and scholars. All of them could join to the cloud network of their organization and acquire data or information from there.
- Enterprise resource planning (ERP) usage in cloud came into existence when there is high development in the business. Service providers install the ERP in the cloud by their own rather than spending money in management of applications, human resources, payroll etc .
- E-Governance in Cloud computing can progress the operational of a government by refining the way it delivers the facilities to its citizens, institutions and cooperation with other governments. We can modify the environment and make it more scalable. It also removes the burden of managing, installing and upgrading applications.
Impact of Cloud Computing
Cloud computing will be very beneficial for the business and people individually.
- Gaming and Application world: Education can be provided to people by means of cloud computing via applications. All the required information would be available at our ease. Gamers can enjoy undisrupted experience with the 3D games available on mobile device with cloud.
- Things can be fixed easily before their failure: With the help of cloud , one can detect the failure of the household stuff by using cloud based applications. Like in healthcare industry, medical equipment’s have been made which works as per the information stored in it to give accurate details. Doctors can access the patient details through mobile phones.
- Use of Computers will diminish: Soon our usage on computers will be hands free , only changes detected by 3D camera and gestures and infrared detection method will be in existence. Users can use tablets and Mobile phones for any kind of sharing than access computers.
- Shopping would be easier: Rather than going to stores for shopping, one can shop sitting at home. If certain products are not available in the store online, cloud based application will automatically send the notification to the store warehouse about its unavailability.
- Small business leverage cloud: Due to limitations of budget, small business will grow worldwide with reduce overhead cost. We need not build new data centers for different small organisations, companies can use infrastructure as a service for keeping the same pace as their large companies’ competitors.
- Travelling will be smooth: Some of the students created a cloud computing mobile application which track bunch of vehicles travelling together. The application gives explorers a chance to view vehicle telemetry about their speed and fuel use; send cautions about stops en route; advise kindred caravaners by messaging street condition and risks; and select the best course. The blend of area following, online networking and cloud-based investigation could enhance a wide range of transportation situations.
- Laptops/ computer data breach: No longer the data is stored on a physical device, so it is just a means to access our data. Data is encrypted to protect it on internet, one can carry laptop with all the important information on it.
- Public/ Private Cloud for Home purpose: For monitoring the health of the patient, with cloud one can utilizes an infrared camera mounted over the restroom mirror to take a day by day photograph of a man’s face. After some time, the pictures can be put away and dissected for changes, alarming specialists of pre-destructive skin cells so treatment can start prior.
- Each one will be rise up in business field: One can identify the user need according to the usage and predict the requirements and activities. Analysing the behaviour of the customers will change the innovation and accelerate in entrepreneurship.
- Lessen language barrier: Nowadays, iphone has developed an application for converting the voicemail messages to text messages. Recognition of Speed accuracy provision is also provided for mobile users.
Security in Cloud Computing
Handling security in the cloud is about acclimatizing to an agile world where development is quick and resources are adjustable. However, old security techniques and suitable perimeter protection are not enough, extra tools and assessment practices should be taken into consideration to offset risks for quick development and multi-tenant service provider settings to guard delicate data. We should train the users on how to protect their system by training them with new automation tools, encryption, conduct security tests to adapt in an agile cloud world. Training and awareness of the staff is important. Developers of Cloud must be trained as the whole organization should be skilled at recognizing social engineering occurrences of imitating the websites to steal credentials and install malware on your systems. Security always starts with people.
When familiarizing security to the cloud model and taking over these best practices we would be certain of a cloud application to be more secure, than an application deployed in a non-cloud environment. Based on the development of cloud technologies and the upgrading of the toolsets that functioning teams, developers and security engineers influence, we expect that with time security on public cloud services will lessen. Security will still be a vital topic, but not because of intrinsic restrictions or security breaches in the technology happening on the cloud.
Latest Development/Trend in Cloud Computing
Mobile Cloud Computing
In the era of cloud computing, people regularly use mobile devices. The mobile devices like smartphones, tablets, iPhones are associated to the cloud over internet. We have created a platform of “Bring your own device” BYOD to store or manipulate their data on cloud for streaming, storage and syncing. IT departments must find the method to consolidate personal cloud services for their workers in a BYOD background with tools such as Mobile Device Management. MCC is in its beginning stage and it experience many problems in combining mobile and cloud computing technologies. Although the mobile technologies are progressing in a faster speed, the essential characteristics of mobile devices concerning about their storage capacities, processing speed, screen size, battery life etc. own a significant issue towards execution of MCC [10]. The wireless interconnection in mobile devices is also a major issue because of data rates and signal strength fluctuating based on network. Thus MCC technologies should concentrate on resolving issues of reliability, latency and throughput [11]. [Significantly, MCC is a growing technology to look forward as both mobile and cloud technologies
New Cloud Services
By constantly mounting developments in the field of cloud computing, the services offered are achieving modern heights. New services include following:
MaaS, C-MaaS, CaaS, DaaS and XaaS.
Monitoring-as-a-Service: MaaS is a service rent out to enterprises to supervise their applications distributed in the cloud. MaaS focus on the several security characteristics like integrity, privacy of their applications and track the cloud environment, dedicated servers or cloud infrastructure [12]. It enables customers to observe from one center regardless of the location of their applications. NewRelic, AppDynamics, Coradiant are some of the merchants who propose MaaS [13].
Cloud Migration as a Service (C-MaaS): It handles with relocating of in house servers to cloud setup. It enables the customers to change their physical and virtual servers into any cloud computing stage. One such example is Rivermeadow enCloud that allows customers to relocate to cloud in a cost-effective way. It comprises of four steps in migrating namely Collects, Converts, Deploys and Synchronize [13]. Communication as a Service delivers IP communication technologies like VoIP, PBX and VPN as a service over cloud [14]. This eradicates the need to be contingent on other providers or services to start communication. The communication can take various forms like e-mails, chats, voice and video calls etc [15].
XaaS or ‘anything as a service’ points to granting any feature to users through cloud than in house systems. A few XaaS services include Storage as a Service, Unified Communications as a Service (UCaaS), Network as a Service (NaaS), Desktop as a Service (DaaS) etc [16].
Soon, solutions to protection and management of identity is going to take a troll in the Industry for improving the security issues in the cloud systems.
Development of cloud based applications consistent with multiple platforms to scale up the efficiency and scalability of the cloud computing.
Hybrid Clouds which is an amalgamation of private and public cloud. Several companies are expected to implement cloud deployment model and discard the old process of cloud which include a wiser swing from labour-intensive to operative cost models with lesser total cost, compact complexity and better dexterity. This will be a high value addition for businesses and activities which provisions business innovation with possibly lesser hazards.
Advantages and Disadvantages of Cloud Computing
Advantages of Cloud Computing
Key to Storage
Elasticity on the storage of cloud according to the demand of the client when they require more it will be given inevitably or will be decreased if not needed.
Cloud offers best storage systems like Google Drive, Dropbox for storing the files than earlier means of backup options like CD’s, hard drives. Backup can be done anytime and anywhere with the access of internet with our own comfort. With Cloud, users are offered free storage up till some size for storing small files and clients can upgrade the space to save large files such as videos, images. Pupil need not spend money on buying hardware and upgrading their computers for storing files.
Save Money
The companies pay, as much as they use [17].Money is saved on the purchase of computers and upgrading them on regular basis according to the user need , Internet serves the purpose to upload the files on Cloud and the avail the best services like free storage and call facilities free of charge.
Ease of access
With the use of Internet and Cloud services, one can easily access their documents from anywhere even if you don’t carry your laptop or pen drive. With the cloud, the “Bring your own device” (BYOD) policy can be easily adopted, permitting employees to bring personally owned mobile devices to their workplace.
Backup and Recovery
In case of any disaster, company has a backup for the data. Backing up and restoring the data in cloud is comparatively easy than on computers. Moreover, retrieval of data is handled by the providers of cloud. Henceforth, old systems of storing the data is surpassed by the backup and retrieval services provided by cloud providers.
Quick Deployment and ease of integration
Lastly and most importantly, Cloud computing gives the advantage of quick deployment. Once opting for this method of functioning, the entire system can be fully functional in a matter of a few minutes. Of course, the amount of time taken here will depend on the exact kind of technology that is needed for the business. Furthermore, software integration occurs automatically and organically in cloud installations. A business is allowed to choose the services and applications that best suit their preferences, while there is minimum effort in customizing and integrating those applications
Disadvantages of Cloud Computing
Limitation on Bandwidth
“Bandwidth is a measure of how much data can be moved from one spot to another in a given amount of time” [18]. If bandwidth is not as quick as the customer want, the result would be not apt.
Security
Possible risk of the data been misused by an unauthorised person. There is a bigger risk on the data being hooked, if the client has no full control. After the client makes sure that a vendor takes security measures, they are to consider the data transfer by using encryption technologies [19].
Technical Issues
Though it is true that information and data on the Cloud can be accessed any time and from anywhere, there are moments when the system can have some serious malfunction. Businesses should be aware of the fact that this technology is always prone to outages and other technical issues. Even the best Cloud service providers run into this kind of trouble, in spite of keeping up high standards of maintenance
Prone to attack
Storing information in the cloud could make the companies vulnerable to external hack attacks and threats, therefore there is always the lurking possibility of stealth of sensitive data. Related to the security and privacy mentioned before, note that cloud based solutions are exposed on the public internet and are thus a more vulnerable target for malicious users and hackers. Nothing on the Internet is completely secure and even the biggest players suffer from serious attacks and security breaches. Due to the interdependency of the system, If there is a compromise on one of the machines that data is stored, there might be a leakage of personal information to the world.
Possible downtime
Cloud computing makes the small business dependent on the reliability of their Internet connection. Additionally, you should remember that the whole setup is dependent on internet access, thus any network or connectivity problems will render the setup useless. As a minor detail, also keep in mind that it might take several minutes for the cloud to detect a server fault and launch a new instance from an image snapshot.
Inflexibility
Choosing a Cloud computing vendor frequently means locking the business into using their proprietary applications or formats. For instance, it is not possible to insert a document created in another application into a Google Docs spreadsheet. Furthermore, a company needs to be able to add and/or subtract Cloud computing users as necessary as its business grows or contracts.
Lack of Support
“Customer service for Web apps leaves a lot to be desired – all too many cloud-based applications make it difficult to get customer service promptly – or at all. Sending an email and hoping for a response within 48 hours is not an acceptable way for most of us to run a business”
Discussed Papers
Paper 1: Mobile Cloud: Advantage, Disadvantage and Open Challenge [20]
In this paper, author has focused on the overview, importance of mobile cloud computing, the challenges in mobile cloud computing and pros and cons of mobile application a most of the applications on mobile phones are compatible with cloud. With internet and mobiles, applications for smart phones, tablets and laptops are taking troll in the IT industry for the next generation. Only demerit of smart phone is the storage capacity which is very limited, cloud has overcome that by providing storage on cloud over internet. Applications in such devices grants access to mails, search engines, games and music .
Author has also briefly discussed about the basic concept of cloud, deployment models, architecture and service models.
Areas where applications of Mobile Cloud Computing are advantageous:
- Healthcare: Services such as on demand are offered to the hospitals on the cloud in spite of individual applications. Health related mobile applications is really useful in maintaining the records, reduce medical error, security and privacy to the patients records.
- Gaming: Only the screen is the main interface for the gamers , in cloud ,rendering of graphics to server states that multimedia code must save battery and increase playing time.
- Government: To make services of government accessible anywhere anytime, mobile devices are being used by people to use govt applications.
- Banking: Applications are used to check the banking details and transactions via sms on mobiles.
- Learning on Mobile: It is combination of e-learning and cloud on mobile device. Anybody can access or learn any new thing via Mobile learning applications.
Most biggest challenge according to author in this paper is low bandwidth, Quality of service, cost and interoperability.The following are the merits and demerits of Mobile Cloud Computing:
Merits:
- Good storage.
- Scalability
- Cost efficient
- Access anywhere and anytime.
- Reliable backup and recovery solutions
- Redundancy and backup recovery services.
- Performance and Scalability.
- Easy Integration and deployment is quick.
- Environmentally friendly.
Demerits:
- Compliance
- Security
- Privacy
- Control of Information flow
- Compatibility
- Cost is unpredicted
- Provider dependency
- Control is limited on remote
Paper 2: Cloud Computing Applications for Smart Grid: A Survey [21]
This article describes the future of the smart grids. Smart grids smoothens the electricity flow in the distributed architecture where management of power needs to be secured, reliable, cost effective and efficient. By using cloud applications, difficulties of conventional smart grid to cloud smart grid can be overcome. Smart Grid is two way communication between consumers and utilities ,manage and control the usage of power to the software systems at both consumer and producer end. Utilities should expand the communication network management system so that they can achieve appropriate data center with the help of which they can administer lots of smart meters into certain dependable established ways. Smart Grids with infrastructure of Cloud, applications can be accessed anywhere and anytime by the customers.
Author has explained cloud computing definition, the types of cloud services and deployment models. The authors discuss when we implement cloud for smart grid energy management the existing building blocks such as demand response without cloud are diminishing.
Figure1: below represents view of both the conventional smart grid without Cloud and smart grid with Cloud.

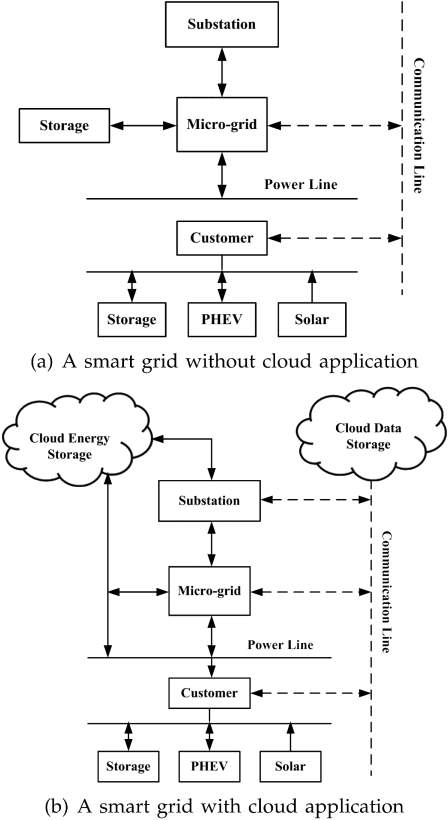
Figure1: Smart grid with and without cloud
These are the below issues without cloud smart grid architecture:
- Server capacity is limited.
- Master Slave architecture is dependent on two way communication. Any failure of one end can lead to failure of entire system.
- Cyber attacks
- Limited storage and memory in energy management i.e. Demand response when the customers are more.
- Limited bandwidth and energy resources.
- Management of Micro Grid.
In the end author has focussed on the solution of the problems in smart grid without cloud by introducing the two types of Cloud-Based Demand Response:
- Communication in Data centric manner.
- Group Communication in Topic based manner.
Smart Grid Information Management using cloud is also described to enhance the delay in the communication. Figure2 depicts that the warehouse is the cloud data storage for smart meters, utility provider, substation and micro grid.
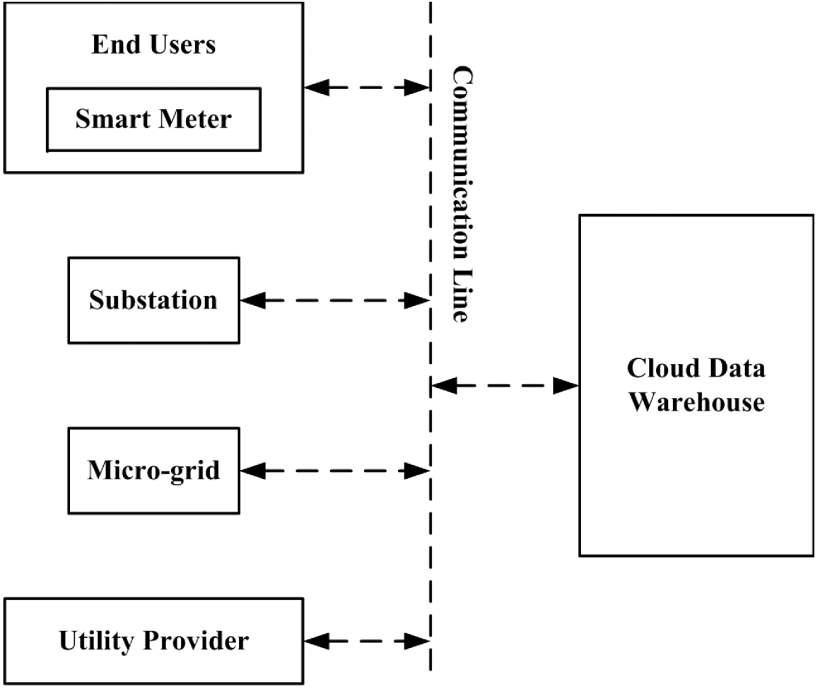
Figure2: Cloud Data Warehouse communication with smart grid.
Smart Grid with cloud computing security.Figure3 shows the cloud computing and smart grid components interaction. To grant security to clients, only approved components of smart grid can use different cloud services.
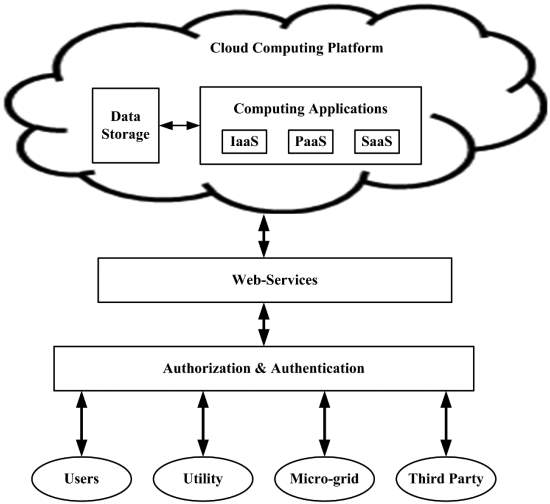
Figure3: Cloud and smart grid components interaction
Smart grid design will leverage cloud computing to optimize security, cost of monitoring, power and data management.
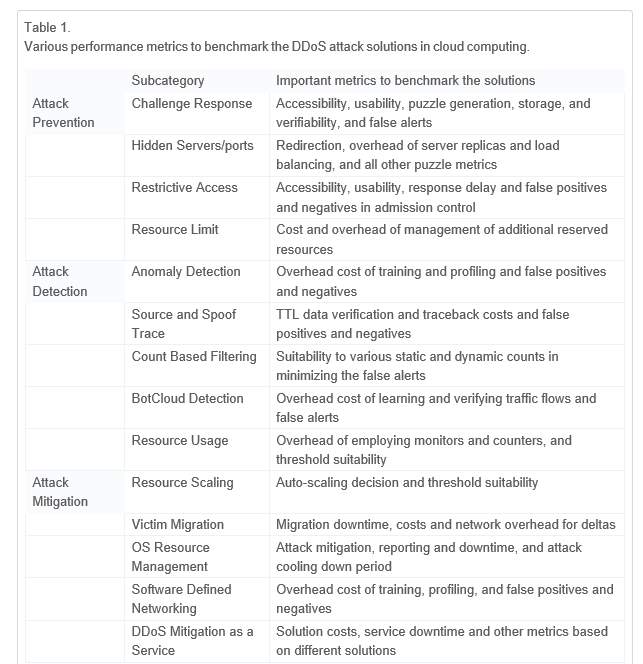
Paper 3: DDoS attacks in cloud computing: Issues, taxonomy, and future directions [22]
As the cloud computing is in the boom in addition to different technologies, being the data and confidential information stored onto the cloud, security becomes the major reason to worry about, being attacked on cloud effects that disbalance the operations and working and flow of other departments.
One major issue is DDOS (Distributed Denial of Service ) attack exist in the cloud computing, highly required solution for these types of attacks, few solutions like auto scaling solutions, mitigation security for resources available. Services like cloud computing being so famous due to its “pay as you go” services, comparatively like in house systems there are ample number of cons with maintenance, hardware cost etc, but as everything comes with pro’s and con’s, all the cons can be overhead by taking preventing measures like users which are suspected are being filtered out or dropped before it could affect the sever, prevention does not have any kind of state which it could be figured whether it’s open or attacker or not.
Same time if prevention could not work but do always work on the detection of the attacker where signs are present on to the server and the could easily monitored using performance analysis, few categories we could help in attacker detection are as follow like usage of the resources, automation detection using some bot, filtering in the numbers or detection of the anomaly etc.even though being affected by by attacker, mitigation process will help the user to recover for the same,it can be achieved using different sub categories like scaling the resource.
According to the author mention being the cloud the primary source of the data, n number of work and attacks has been referred before coming on the conclusion and future discussions has been referred.
Few aspect that do matters are as follows:
- Features and the impacts
- Can be prevented using test
- Setting the proper number and filtering on the patterns
- Scaling of the resources used in the application
As the management of resources in operating system and inbuilt service like DMass as a service. The three-primary solution can be used to achieve solution or prevention from being attacked by the attacker prevention, mitigation and detection and these solution have proved and tested with their effectiveness evaluation in cloud computing.
Paper 4: Cloud Computing Research and Development Trend [24]
Internet has been developing very quickly in recent 10 years, the cost of maintaining the storage,hardware and power consumption is increasing day by day. To resolve this problem we have a new kind of model which is Cloud Computing. Cloud computing serves the purpose of users by providing hardware, software and services in a secured, quick and convenient way which is centered by internet. It utilize the vacant resources of computer and also increases the performance of network.
The main characteristics of cloud computing is in Virtualization, distribution and data transportation.
In virtualization we have nothing to do with physical hardware, many factors such as IT source,software, hardware, operating system and net storage can be easily virtualize.
E.g.:- suppose we have to increase our storage capacity of server, in this case we don’t need to purchase the server physically we just need to add virtual machine on the running server, in this way we can save large amount of money. We have various types of styles in cloud computing like:
- SAAS (software as a service) it integrates all the companies that provide similar services on internet by sharing their resources through browser. Salesforce is the main company that provide this service
- Utility computing in this recently Amazon, Sun, IBM companies are appearing which provides storage and virtual services to users through collecting memory and equipment’s.
- Network service in this the service providers instead of providing single machine procedure through API, they help programmers to create internet bases applications.
- PAAS(platform as a service) :- it provides development environment as a service to users.
- MSP (management service provider):- this mostly serves the IT industry instead of users.
- Commercial service platform its mix of saas and msp it basically provides platform for interaction between users and service providers.
Cloud computing characteristics: –
Ultra large scale it enlarges the users computing powers as scale of servers is large
Virtualization: – cloud is completely virtualize by this we can get any service any time on Mobile and PC.
Cloud computing is highly reliable than local computer by using multiple transcript fault tolerant, the computation node isomorphism exchangeable.
Cloud computing is Versatile as it doesn’t aim at special application, various applications are supported by cloud and each cloud further support different applications running at same time.
It is highly extendable to meet the increase in requirements demand and we can buy anything according to our need like water electricity.
It’s also very inexpensive
If we use cloud computing without any thoughts then it’s very dangerous as sometimes on small changes management cost will increase sharply so we have to think on our requirements before using cloud computing. There are many more players in the on-demand market that many reports acknowledge. These range from basic infrastructure offerings (IaaS), through platform support (PaaS) to full applications (SaaS) The long term cost of ownership may at first not seem to add up, but take into consideration other factors such as reduced risk and added value and for many organisations on-demand services make a lot of sense. Cloud computing is changing the way IT departments buy IT. Businesses have a range of paths to the cloud, including infrastructure, platforms and applications that are available from cloud providers as online services. Many people may be confused by the range of offerings and the terminology used to describe them and will be unsure of the risk and benefits.
Paper 5: Research on Service-Oriented Cloud Computing Information Security Mechanism
The utilization of cloud computing has made a revolution in the world. The thesis describes the references model, architecture of cloud, cloud security content matrix etc.
Firstly, cloud computing system companies uphold the responsibility of administering and preservation of data centre and make assurance that well developed computing power and gigantic space for the users.
Cloud computing system comprise of three classes which are defined as
PLATFORM AS A SERVICE
INFRASTRUCTURE AS A SERVICE
Software as service
SAAS – Provides all kind of services to users and manufactures through yielding all sorts of assistance in internet software eg Google apps and Microsoft online office software.
PAAS – Provides all kind of services to software developers and yield services like billing, introspection, subscription example salesforce.
IAAS – especially provides all services to developers and yield detailed infrastructure such computation, storage and bandwidth example amazon’s ec2/s3.
Reference model of cloud computing system
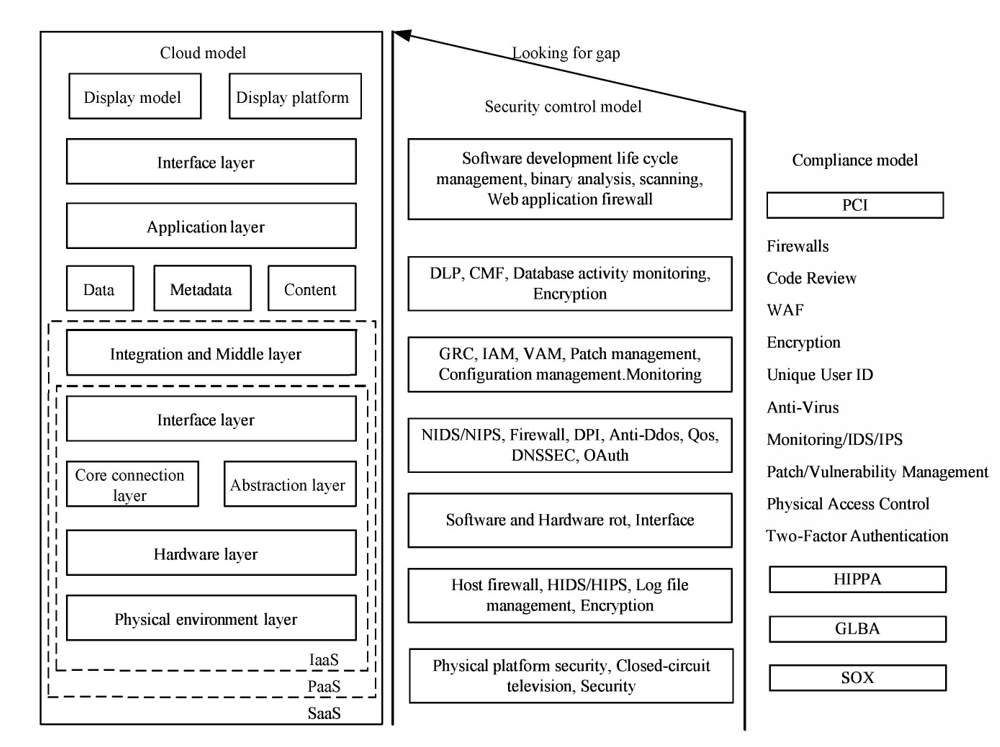
Figure: Security Reference Model for Cloud Computing
Furthermore, to have a good knowledge of cloud computing system it is necessary to understand relationship between cloud computing model and dependencies. All cloud computing services are linked to each other. IAAS is located at hardware platform on which PAAS is place which upgrades the application development and middleware. However, SAAS is located at the bottom of the IAAS and PAAS.
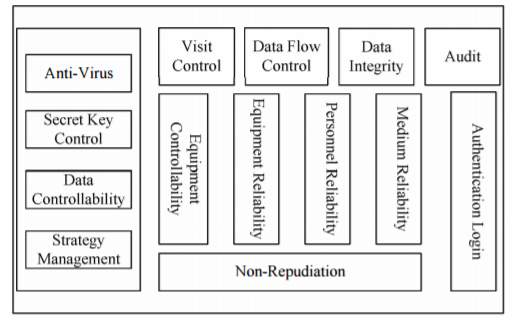
The paramount feature of cloud computing system is lower level. They all are highly encrypted and have three segments such as data security, application security and virtual security.
Data security- there is a need of data vanquishing and theft it doesn’t matter what kind of data is used data security is more important and is protected by data transmission security, data isolation and data residual.
Application security- due to change in data accessibility there is a threat to all kind of application and is fortified by the end user security, SAAS application security and PAAS application security.
Virtual security- to make the operation stable, safety measures must be taken virtualisation technology. Security of virtualisation includes isolation of virtual machine, virtual firewall, safety management of virtual machine, virtual machine monitor and vulnerability management.
In the other part, author describes the security framework of cloud computing. Figure.
Security framework of cloud computing
The author has also put forward the below strategy to secure the cloud computing security service:
- Risk assessment analysis to start public and private cloud.
- Enterprise trusted cloud.
- Encrypt data
- Authentication
- Data transmission security
- Selecting service provider according to requirement.
In the end author states that the Internet of things must be the next footstep to encourage cloud computing security services.
Paper 6: Security Issues In Service Model Of Cloud Computing Environment [26]
Cloud computing service is the emerging era of Information Technology. In the era of rapidly evolving technology and its high-paced advancement, It brings certain advantages to the table such as reducing operational costs and high availability to end users. It has stretched its arms across all sizes of enterprises vis-a-vis large, medium and small.
There are various IT giants that roll out the cloud services like Google, Microsoft Azure and Amazon.
Data centers function as the backbone of computing which is termed as IaaS(Infrastructure as a Service ) and includes storage, servers, routers, hubs and the application service for end user is termed as SaaS (Software as a Service).
Platform as a Service(PaaS) exposes various APIs for developer to deploy and test their services on different environment and programming languages.
Among various threats to Cloud Services, some major threats are listed below:
- Data losses
- loopholes in risk security measures
- Weak inter-platform security
- Prone to cyber-Attacks
- Issues in Accessibility and Dependability
- Piracy of Account
- Legal issues
- Danger in sharing the same technology
While adopting Cloud systems, providers should follow some of the following guidelines:
- Analysis of end to end data transmission and encryption techniques.
- Regular security audits should be carried out internally as well as by external agencies.
- Security systems should be kept abreast with changing technologies in cloud.
- Data of the client to be accessible to only privileged users.
Cloud providers to ensure that they deploy only limited professionals to access the data with required approvals.
5. Data should be encrypted using robust techniques.
6. Contingency plan in case of disasters and how data would be recovered in wors case scenario.
7. Cloud service providers should ensure that their hardware must be fully secure and not prone to malicious attacks.
8. Legal procedures in case of contract breach should be clearly stated and if provider fails to conform with contract,it is liable for penalty.
To achieve security in the cloud computing, author has given the resolution :
- Finding right cloud provider.
- Transparent contract with cloud vendor.
- Good recovery facilities.
- Infrastructure which avert cyber-attacks.
- Using Encrypted data.
- Proper study of data.
Security issues, resolutions, threats are explored so far in this research. Soon Cloud would deliver a secure environment for IT industry. In future work, we will incorporate the diverse cryptographic-calculations by tackling the security in distributed computing.
Paper 7: Cloud Computing and Inter-Clouds – Types, Topologies and Research Issues [27]
Cloud computing is the emerging technology that has invaded every dimension of the software world right from storage of data to development platform to the service offered to end-user.
Key Characteristics:
- On-demand self-service-Users are provided with storage and computing capabilities based on their requirements.
- Resource sharing-Computing resources are shared among customers globally.
- Network access-Customers can access the services over thin clients like laptops, tablets, computers and cellphones.
- Resource optimization-Based on metering calculations, resources are optimized based on services offered to user by the cloud service provider.
Cloud Architecture:
- Front end– Cloud clients like the apps running on mobile, web and thin clients.
- Back-end–
- Infrastructure as a Service(IaaS) – Storages, network switches and hardware components.
- Platform as a Service(PaaS) – Runtime environment, DB server and dev tools.
- Software as a Service(SaaS) – End user service like Email, CRM, Games etc.
Cloud Deployment Models:
- Public Cloud – Small industries can leverage the cloud services on a pay on-demand basis and resources are allocated dynamically as per respective ask. General public can also access same. Infrastructure is maintained at the cloud service provider.
Merits include-reduced cost, global access, flexibility. Demerits are Less secure and customisability.
- Private Cloud – Caters solely to an organizational need and infrasturcture can exist on premises or off-premises.
Merits-High security, privacy and increased control. Demerits-inflexible cost and limited area.
- Hybrid cloud – Cloud infrastructure is a collection of both private and public cloud with a standardized technology for exchange thus enabling portability.
Merits-Scalability, cost efficiency, flexibility.Demerits- Networking issues and security compliances.
- Inter-Clouds – It refers to interconnection of public clouds of different cloud infrastructure providers to ensure portability and interoperability.
Need for inter-cloud arises when the storage has exhausted and to ensure continuity of expanding demands of user. It helps in utilising the resources of other clouds available.
Types of Inter-Clouds
1. Federation – Cloud providers in same organization or federation voluntarily agree to allow inter-connectivity of resources and infrastructure.
2. Multi cloud – There is no voluntary service offered by service provider however client has to utilise shared resources of multiple independent clouds.
Topologies:
Federation:-
- Peer-to-peer Inter-cloud federation – Clouds collectively interact with each other without any mediator. May use distributed entities for directories. eg. Open Cirrus, Reservoir, Arjuna Agility
- Centralized inter-cloud-Clouds use a central entity as a storehouse which registers the various clouds and then resource sharing is carried out. e.g inter-cloud, DCC, Contrail.
Multi-cloud:-
- Multi-cloud service – Clients access various clouds through service hosted on client or on externally.
e.g STRATOS, OPTIMIS, mOSAIC, Contrail.
- Multi-cloud libraries – Clients develop their own library as API which inter-clouds can use collectively e.g. Jcloud, Apache Nuvem, Apache Libcloud.
Inter-Cloud Research Issues:
- Application Service Behaviour Prediction– There is a need for building models to learn, predict and forecast the service behaviour and the challenge is when these services behaviour changes hence affecting the demands.
- Optimal mapping of server to resources-Significant operating costs warrants maximising efficiency through optimal mapping between services and resources. Quality of Service(QoS) is not compromised in optimizing resource utilisation.
- Optimization models-Optimization strategic models should be developed that determine best deployment plan and service to achieve both user-centric and resource-centric QoS targets.
- Asset-Cloud service integration-Clients have business applications and data that must not be migrated to cloud for privacy reasons and this warrant need of integration and interoperability to address issues like data management and identity management.
- Decentralized system monitoring-Federation share resources in a distributed manner however the system optimization and monitoring is centralized. Due to scalability and performance concerns, indexing models and service monitoring that are decentralized are necessary.
Author has discussed various inter-cloud architecture and the need for it along with examples. The various topologies in Inter-cloud and research challenges for it which must be addressed to implement Inter-cloud.
References
[1] “history-and-vision-of-cloud-computing,” timesofcloud, [Online]. Available: http://timesofcloud.com/cloud-tutorial/history-and-vision-of-cloud-computing/.
[2] K. K, P. E, N. SS and C. JN, “Virtualization Technology in Cloud Computing Environment,” IJETAE 3, 2013.
[3] Cloud-Computing-Architecture-Diagram.jpg, “http://cloudcomputingnet.com,” 2015. [Online]. Available: http://cloudcomputingnet.com/wp-content/uploads/2015/05/Cloud-Computing-Architecture-Diagram.jpg.
[4] A. L. J. N. T. S. a. S. T. M. Klems, “What’s Inside the Cloud? An Architectural Map of the Cloud Landscape,” IEEEXplore, pp. 23-31, Jun 2009.
[5] “iaas-pass-saas-the-cloud-101,” 07 09 2014. [Online]. Available: https://www.linkedin.com/pulse/20140907071547-305726885-iaas-pass-saas-the-cloud-101.
[6] K. B. R., P. R. and R. A., “Cloud Security Issues,” In Proceedings of IEEE International Conference on Services Computing, pp. 517-520, 2009.
[7] “Global Netoptex Incorporated. Demystifying the cloud. Important opportunities, crucial choices,” no. Global Netoptex Incorporated. Demystifying the cloud. Important opportunities, crucial choices.‖ pp. Available: http://www.gni.com [Dec. 13, 2009]., pp. 4-14, 2009.
[8] “Hybrid Cloud by Webopedia,” [Online]. Available: http://www.webopedia.com/TERM/H/hybrid_cloud.html.
[9] V. Rajaraman, “Cloud Computing,” in RESONANCE, RESONANCE, 2014, pp. 242-258.
[10] H. Q. Abdullah Gani, “Research on Mobile Cloud Computing: Review, Trend and Perspectives,” in IEEE, 2009.
[11] Vidhya.V, “International Journal of Advances in Computer Science and Technology,,” IJACST All Rights Reserved networks, pp. 65 – 69 68, May 2013.
[12] h.-i.-m.-a.-a.-s.-m. aas.
[13] “http://www.toolsjournal.com/cloud-articles/item/1146-riv ermeadow-cloud-transition-saas-to-reach-masses-with-vmw are-link-up”.
[14] [Online]. Available: http://www.logitel.gr/solution/server-based-cloud-compu ting/communications-as-a-service-caas. .
[15] P. S. a. S. V. Dipal Vashi, “Communication as a service based Cloud Computing,” International Conference on Emerging Technology Trends, pp. 15-17, 2011.
[16] [Online]. Available: http://clean-clouds.com/2011/12/10/xaas-anything-as-a-service..
[17] J. B. R. &. K. M. Hurwitz, Cloud Computing For Dummies, New Jersey, NJ: Wiley: Retrieved from ProQuest ebrary database, 2009.
[18] E. &. L. B. Marks, Cloud Computing, New Jersey, NJ: Wiley, 2010.
[19] J. M. Galloway, A cloud architecture for reducing costs in local parallel and distributed virtualized cloud environments, ProQuest Dissertations & Theses Global., 2013.
[20] A. Alzahrani, N. Alawan and M. Sarrab, “Mobile cloud computing: advantage, disadvantage and open challenge,” Proceedings of the 7th Euro American Conference on Telematics and Information Systems, p. 21, 2014.
[21] S. a. M. S. a. R. J. J. Bera, “Cloud computing applications for smart grid: A survey,” IEEE Transactions on Parallel and Distributed Systems, vol. 26, pp. 1477-1494, 2015.
[22] G. a. G. M. S. a. S. D. a. C. M. a. B. R. Somani, “DDoS attacks in cloud computing: issues, taxonomy, and future directions,” Computer Communications, no. Elsevier, 2017.
[23] A. Popescu, “Definition of Cloud Computing.,” 15 October 2009. [Online]. Available: http://jots.mypopescu.com/post/213246006/cloud-computing-definition.
[24] G. Joshi, E. Soljanin and G. Wornell, “Efficient Redundancy Techniques for Latency Reduction,” 2015.
Cite This Work
To export a reference to this article please select a referencing stye below:
Related Services
View allRelated Content
All TagsContent relating to: "Computing"
Computing is a term that describes the use of computers to process information. Key aspects of Computing are hardware, software, and processing through algorithms.
Related Articles
DMCA / Removal Request
If you are the original writer of this dissertation and no longer wish to have your work published on the UKDiss.com website then please:




