Remote Cross Platform Task Manager Development
Info: 12717 words (51 pages) Dissertation
Published: 15th Jun 2021
Chapter-1 Introduction
1.1 General Introduction
Task Manager is basically used for managing task, system monitoring and start up manager included with systems. It provides limited information about computer performance and running applications, processes and CPU usage, memory information, network activity and statistics, logged-in users and system services. The Task Manager can also be used to set process priorities, processor affinity, forcibly terminate processes, shut down, restart, hibernate, or log off from system.
Each operating system has its own task manager which control its task, monitor them and organised them in optimal way by using appropriate system calls, but in our project we are developing an advance application which can monitor task of other system along with its own, by using our application user can control task of other operating system along with its own. Such as, a user can manage Ubuntu task by using Android or Android task by using Ubuntu. User has to ask for permission to another system if he or she want to connect with that system. If permission has granted then the user can monitor the task of another system by using his/her own device. We have provided password protected connectivity, task monitoring of another system, multiple platform connectivity from single device, connection of different system using sockets.
User can kill process or task of his or her own system or process of another device, monitor CPU usage of different system, check graph of CPU usage, check memory utilization of system, create or start new process of his or her own system along with other system irrespective of operating system that system have and user can also change the priority of task of his or her own system along with another system. Our task manager user system calls and sockets of different operating system to provide all the functionality that we have mentioned. We have used different technology and tools to achieve our goal. Till now we have developed remote task manager for Android and Ubuntu and windows. A user can also monitor the task of distant device by using google firebase. Security is the main concern here because accessing any device remotely may leads to the security threats, so till now we have protected our application with password and some other security measure. We can even use statically approach by using R-language to extend the functionality of our application in future.
1.2 Problem Statement
Today, each operating system has its own task manager which monitors their tasks, CPU usage, produce statistics accordingly. But what about distributed system, in distributed system several computer are connected to each other through LAN wire or other physical medium and we don’t have any proper task manager to monitor the task of other system. We require a task manager through which administrator can monitor the other system irrespective of operating system. A user can also monitor other system by using Google firebase, this require a decent internet connection.
We are developing a remote cross platform task manager through which can monitor or perform everything that present task managers are doing. We want to connect different operating system with sockets or monitor different operating system from a single source. The main objective of this project is to view all the running tasks, resources occupied by the respective tasks, kill a task of another or same system and to control the tasks of a remote system. It also represents the CPU usage in a graphical representation. Our objective is to develop a cross platform task manager to control tasks of Android, Windows and Linux system from any device and this device may have any operating system. Second important problem is to reduce delay which we are going to have while sending the task information through sockets between different operating system. Thirdly task may have different permission problem in different operating system, so we also have to keep that in mind while developing our application.
1.3 Details of Empirical Study
1. Android : Android is a mobile operating system developed by Google, based on the Linux kernel and designed primarily for touch screen mobile devices such as smart phones and tablets. Android’s user interface is mainly based on direct manipulation, using touch gestures that loosely correspond to real-world actions, such as swiping, tapping and pinching, to manipulate on-screen objects, along with a virtual keyboard for text input. In addition to touch screen devices, Google has further developed Android TV for televisions, Android Auto for cars, and Android Wear for wrist watches, each with a specialized user interface. Variants of Android are also used on notebooks, game consoles, digital cameras, and other electronics[14].
Android has the largest installed base of all operating systems of any kind. Android has been the best selling OS on tablets since 2013, and on smart phones it is dominant by any metric.
Initially developed by Android Inc which Google bought in 2005, Android was unveiled in 2007 along with the founding of the Open Handset Alliance , a consortium of hardware, software, and telecommunication companies devoted to advancing open standards for mobile devices. As of July 2013, the Google Play store has had over one million Android applications published including many business class apps that rival competing mobile platformsand over 50 billion applications downloaded. An April May 2013 survey of mobile application developers found that 71% of developers create applications for Android, and a 2015 survey found that 40% of full-time professional developers see Android as their priority target platform, which is comparable to Apple’s iOS on 37% with both platforms far above others. In September 2015, Android had 1.4 billion monthly active devices[14].
Android’s source code is released by Google under open source licenses, although most Android devices ultimately ship with a combination of open source and proprietary software, including proprietary software required for accessing Google services. Android is popular with technology companies that require a ready-made, low-cost and customizable operating system for high tech devices. Its open nature has encouraged a large community of developers and enthusiasts to use the open-source code as a foundation for community driven projects, which deliver updates to older devices, add new features for advanced users or bring[14].
2. Python2 : Python is a widely used high-level, general-purpose, interpreted, dynamic programming language. Its design philosophy emphasizes code readability, and its syntax allows programmers to express concepts in fewer lines of code than possible in languages such as C++ or Java. The language provides constructs intended to enable writing clear programs on both a small and large scale[15].
Python supports multiple programming paradigms including object-oriented, imperative and functional programming or procedural styles. It features a dynamic type system and automatic memory management and has a large and comprehensive standard library[15].
Python interpreters are available for many operating systems, allowing Python code to run on a wide variety of systems. CPython, the reference implementation of Python, is open source software and has a community-based development model, as do nearly all of its variant implementations. CPython is managed by the non-profit Python Software Foundation[15].
3. Java : Java is a programming language and computing platform first released by Sun Microsystems in 1995. There are lots of applications and websites that will not work unless you have Java installed, and more are created every day. Java is fast, secure, and reliable. From laptops to data centers, game consoles to scientific supercomputers, cell phones to the Internet, Java is everywhere[16].
Java used for application programming, system programming, system programming as well as distributed app development. Java has its own run time environment as software development kit. It is platform independent. It is secure because it does not need operating system support to run its program and it does not have explicit pointer[16].
4. Glade : Glade is a RAD tool to enable quick & easy development of user interfaces for the GTK+ toolkit and the GNOME desktop environment. The user interfaces designed in Glade are saved as XML, and by using the Gtk Builder GTK+ object these can be loaded by applications dynamically as needed. By using Gtk Builder, Glade XML files can be used in numerous programming languages including C, C++, C#, Java, Perl and Python[17].
5. Quickly :Quickly is a framework for creating software programs for a Linux distribution using Python, PyGTK, Glade Interface Designer and Desktop Couch. It then allows for easy publishing using bzr and Launch pad.
Quickly is designed to speed up the start of new projects with the use of templates, not only for programs but for any type of project. These templates are used to automate project configuration and maintenance. Delegating into templates and not into a specific library allows projects created using Quickly not to require dependencies on any particular library or runtime of Quickly itself.
6. Google Firebase :Firebase is a mobile and web application platform with tools and infrastructure designed to help developers build high-quality apps. Firebase is made up of complementary features that developers can mix-and-match to fit their needs. The team is based in San Francisco and Mountain View, California. The company was founded in 2011 by Andrew Lee and James Tamplin. Firebase’s initial product was a realtime database, which provides an API that allows developers to store and sync data across multiple clients. Over time, it has expanded its product line to become a full suite for app development. The company was acquired by Google in October 2014 and a significant number of new features were featured in May 2016 at Google I/O[18].
7. QtCreator : This is a cross platform integrated development environment for C++, JavaScript and QML. This user C++ compiler and GNU compiler collection. Qt Creator includes a code editor and integrates Qt Designer for designing and building graphical user interfaces (GUIs) from Qt widgets[19].
1.4 Approach to problem in terms of technology /platform to be used
In the field of Computer Science, there is always scope of development and improvement of solutions to existing one or new problems. Delay is associated with present task manager that we already have. When these task manager used in real time then there might be some possibility of some missing packets or data because task manager user system calls to interact with operating system kernal, so when data is sent by kernal it might get lost due to overheads or bus overload which slow processing of the information. So system goes through some recovery option to recover the lost data which cause delay in displaying the output of task manager. On distributed system, some time we want to access the task remotely of another system but we don’t have any proper task manager for this scenario.
1.5 Support for Novelty/ significance of problem
When we transfer task information across the systems then there will be some problem of overhead. Here we are proposing algorithm to take care of the overheads by using proper data structure such as balanced binary tree to store the information because it has height of log(n).We are also providing parental control so that unauthorised user would not be able to access the system remotely. So user has to provide password before accessing the system. Remote task manager would face some problem when server restart itself so in that case server notify client all by itself and application establish the connection again without disturbing the user. In operating system, we also have to take care of operating system’s consistency because there are some task by killing which user will crash the system so entire system will start again and this leads to loss of data and present user work. So we are also hiding those system calls which handle the running of operating system so that it will not stop working.
1.6 Tabular comparison of other existing approaches
| Features | iOS | Android | Windows | Ubuntu |
| Company | Apple Inc | Open Handset Allowance | Microsoft | Canonical Inc. and Ubuntu Community Contributor |
| Current Version | 10.2 | 7.0 | 10.0.14393.448 | 15.04 |
| OS Family | Darwin | Linux | Windows | Linux |
| CPU Architecture | ARM,ARM64 | ARM, x86,
MIPS |
ARM, x86 | ARM, x86, x86-64 |
| Programmed In | C, C++, Objective C, Swift | C, C++, Java | C, C++, .Net, C# | C, C++, QML |
| Shared File Access | Yes | Yes | No | Yes |
| SDK | Mac OS X using iOS SDK | Linux, Mac OS X and Windows | Windows | Ubuntu SDk |
| Parental control | Yes | Yes | Yes | No |
| Non english support | Yes | Yes | Yes | Yes |
Table 1: Comparison between OS
Chapter-2 Literature Survey
2.1 Summary of Additional Relevant Paper
2.1.1 Research paper 1
Title of the paper :Optimized Chat Server Protocol for Server Side Scripting Languages.
Authors :A. P. D. Krishnajith, R. D. I. P. Devinda and R. G. Ragel
Year of publication :2010
Publishing details : 2010 5th International Conference on Industrial and Information Systems, ICIIS 2010, Jul 29 – Aug 01, 2010, India
Summary :
As we will progress with our project, we intend to deliver web services to users which will help them benefit without having the actual app. This research paper helped us to know various techniques we can use while delivering the web app version of our application. This paper broadly discusses two methodologies to efficiently use and implement the connection between server side and client, server being real time web service that will temporarily store our data, like Google’s Firebase, and client being the system which will remotely monitor our host. It discusses the pros and cons of both protocol services and we intend to design a hybrid model using client side scripting. To optimize the total result, the paper proposes to burden the server less so that it can entertain more clients and distribute the load on clients. Also, the server needs to hold a last alive time of hosts in order to efficiently maintain connections and remove any dead link[1].
Web link :http://ieeexplore.ieee.org/document/5578709/
2.1.2 Research paper 2
Title of the paper :A Study of High-Performance Communication Mechanism
for Multicomputer Systems
Authors :Hideki Murayama, Satoshi Yoshizawa, Takeshi Aimoto, HidenoriInouchi, ShooichiMurase, Takehisa Hayashi, Hiroshi Iwamoto
Year of publication :1996
Publishing details :1996 IEEE Proceedings of IPPS ’96
Summary :
The main idea of the research paper under study is to implement various methods to reduce communication software overhead in order to achieve most throughputs in a multicomputer system, i.e., a network full of different computers/work stations. One of the methods to reduce the overhead is by skipping the checksum calculation and it can be implemented for practical use. But the largest contribution to overhead is made by data copying, if we can reduce that, we can efficiently devise a working technique to drastically improve throughput. But data copying cannot always be skipped. The sender side system needs to be synchronous to implement the copy-less mechanism while the receiver side system needs a feature that makes the pre-assigned receive area reside in main memory. To accomplish the above said method, the paper describes a hardware mechanism named DLA. We cannot physically implement DLA, even though it reduces CPU usage by a great deal and increases throughput, but we did learn about trying different implementations of TCP and UDP to reduce a lot of overhead during communication[2].
Web link :http://ieeexplore.ieee.org/document/508042/
2.1.3 Research paper 3
Title of the paper: Predictability of Process Resource Usage: A Measurement- Based Study on UNIX
Authors :Murthy V. Devarakonda and Ravishankar K. Iyer
Year of publication :1989
Publishing details :IEEE Transactions On Software Engineering, Vol. 15, No. 12, December 1989
Summary :
This paper develops a statistical approach for predicting the CPU time, the file IIO, and the memory requirements of a program at the beginning of its life, given the identity of the program. Resource parameters for analyzing program resource requirement are CPU time, local I/O file, memory requirement and starting and ending of program execution. Initially, statistical clustering is used to identify high-density regions of process resource usage for the measured system. The identified regions are used as the states to build state-transition models to characterize the resource usage of each program in its past executions. The prediction scheme uses the knowledge of a program’s resource usage in its last execution and its state-transition model to estimate the resource requirements for the next execution. There are two factors that effect the prediction:
1. Program execution frequency.
2. Maximum and minimum knowledge of the program.
Experimental data show a very small deviation between actual result and calculated result[3].
Web link : http://ieeexplore.ieee.org/document/58769/
2.1.4 Research paper 4
Title of the paper :Research and Design of a Real-time Interactive Application Development Model Based on the Android Platform
Authors :Zhilong Yang, Yong Wang, Yongquan Yang, Zhiqiang Wei
Year of publication :2013
Publishing details :2013 Sixth International Symposium on Computational Intelligence and Design
Summary :
The main observation from this paper is regarding the real-time interactive application development model on the Android platform. The information of server can be displayed in real time to the android device, and user can operate according to the real-time situation. Corresponding operation message is sent back to the server and then the server takes the next action according to the message from client. Android client and server use the persistent socket mechanism to establish connection channel to connect to each other, so that server can push messages to Android client and Android client can send messages to server in real time and the messages are transmitted more rapidly[4].
Architecture of the model that we proposed in this research paper is divided into three function layers, namely the application layer, the data management layer and the basic service layer. The application Layer is built on the other two layers. Users obtain messages from through it and take different actions. The Data Management Layer is responsible for the operation of SQLite database. The Basic Service Layer is responsible for the connection, security, and communication of the entire model[4].
In order to maintain a smooth connection between the client and the server and for maintaining persistent socket connection, 2 techniques are mentioned in the paper. Polling and Push. Polling is the technique in which the HTTP requests are sent to the server at a regular time interval; and every time that the server receives a request, it responds back to the client. However, this technique faces intense communication with the server which causes significant network overhead and high power consumption of Android client. In Push technique, the client creates and maintains a persistent socket connection to server so that the server sends data to the client in real time when the server gets data. The client just sends keep alive package to server at regular time to maintain the smooth connection[4].
Web link :http://ieeexplore.ieee.org/document/6804804/
2.1.5 Research paper 5
Title of the paper :A Memory Management Scheme for Enhancing Performance of Applications on Android
Authors :Kumar Vimal and AdityaTrivedi
Summary :
Though there is a plethora of good applications in the market today, some applications face memory management issue. Memory leaks in the applications can easily affect the overall performance of the application leading to an application crash. Memory is the most important thing that has to be taken care of while working specifically with android it sets a paucity for memory in handset devices. Activity Manager Service(AMS) is required for executing a framework on Android. AMS also helps to receive and respond to user requests. AMS is the first service that boots up during the launch of an application. On Android when an application running on the screen is left then Android does not stop allocating memory to it. This technique helps the application to start at a faster rate hence saving a lot of RAM. Before a ‘low memory killer’ activates itself, the AMS kills the application before it. Furthermore, there are some different algorithms mentioned in the paper to minimize the usage of RAM[5].
Web link :http://ieeexplore.ieee.org/document/7488407/
2.1.6 Research paper 6
Title of the paper :A Software Component for Network Based Data Acquisition and Control Applications
Authors :Guchuan Zhu
Year of publication :2006
Publishing details :The International Workshop on Computer Architecture for Machine Perception and Sensing
Summary :
This paper presented a software component for networked applications, such as data acquisition and control. Being an object-oriented design, this component can easily cope with
different communication protocols. The programming interface is simple and easy to use, and the the communication mechanics is completely transparent to the user. This allows the application code to be reusable and portable to different platforms. Applications, such as simulation of network based[6].
Being built on the basis of object-oriented design, this component can cope with different communication protocols and be easily to extended to multi-platform environment. An implementation of communication through TCP/UDP socket connection is illustrated. Applications of this software component to networked control system simulation on Matlab platform, real-time system control using PC Target, and monitoring wireless sensor networks are demonstrated. it is shown that this software component provides a convenient way for the development of networked based applications[6].
Web link :http://ieeexplore.ieee.org/document/4350346/
2.1.7 Research paper 7
Title of Paper : Design and Implementation of Remote Control System between Android Platform
Authors : Kui-sheng WANG, Yan HOU and Ying-zhuo XU
Year of Publication : 2016
Publishing details : IEEE TransactionOn Information Systems. 24-26 June 2016
Summary :
This paper introduces a remote control system between Android platforms, the system is considerate remote control application for the Android mobile phone users. Structure model was built to analyse the function of the lasers in more detail. In this world of rapid development it is difficult for user to go to a technical advisor for just a small flaw in this device. Hence, it is necessary to design and implement remote control software for the mobile terminals Users can remote control of two phones in any network. The system can ask for help and as well as help others to solve the problem remotely. Firstly, the study begins with learning the architecture if the android platform. Architecture is made up of applications, framework of application, libraries and a kernel. Android application mainly consists of User Interface. It is written in Java program and contains a variety of resource files. It generates an APK package after compilation. Some important frameworks such as RFB protocol was also to keep record of graphical users remotely. RFB is a thin client protocol and reduces the hardware requirements. Transmission Control Protocol (TCP) is used to transmit images between platforms. TCP works on transport layer. As iIPv6 is not universal, every mobile phone has to send its IP individually. This step cannot be completed without a server. Android phone acts as a client during the conversation. In this paper, SQL Lite Database is being used to create record of user logins. Once the client sends request to Graffiti server, it has to be accepted by the server. Communication can be initiated at this stage[7].
Weblink : http://ieeexplore.ieee.org/document/7816692/
2.1.8 Research paper 8
Title of Paper : Design and Implementation of an Application with android with remote management of a smartphone.
Authors : Tito Torres, Darwin Alulema, Carlos Romero
Year of Publication : 2015
Publishing details : IEEE Communications and Computing, 2015
Summary :
Research paper provides us knowledge on a Google provided API i.e. Firebase. It is used for maintain a central database. Firebase is not just a Real-time Database, but it has some more unique features such as Authentication, hosting, notification etc[8].
The basic idea behind creating database is to store data systematically and fetch data when required. Firebase allows us to create database with only a few lines of code. Data is stored as JSON and key-value pair. Adding Firebase to an android application requires following steps.
- Analysis of data and the active users of the database. Firebase provides you with Summarised data.
- For the application to be used by Authorised users only, Firebase provides an “AUTH” feature. User can login with Gmail, Facebook and twitter and can set his own authorization rules as well.
- Database in Firebase is a cloud-based database and SQL queries are not required. Firebase can store all type of data such as videos, raw data, videos etc.
- Firebase also supports Crash reporting of software and hosting of websites.
First step for using Firebase is to create an account on its console by entering name, E-mail and location. Secondly, a JSON file has to be downloaded and pasted in project folder. Moreover, rules can be modified to maintain security. To add data to firebase database, few funtions such as setValue(), push(), runTransaction() etc. have to be used.The data is fetched via Event listener from the database. There are specific things that can be done by using the source code that Google has provided on the firebase website. Firebase stands above all other databases as there are specific rules and regulation to implement it. The probability of mismanagement of data is reduced by a large percentage[8].
Weblink : http://ieeexplore.ieee.org/document/7152090/
Consolidated Summary of Literature Study:
Chapter-3 Analysis, Design and Modeling
3.1 Description of Project
A well written description of any project makes it possible for the indented audience (e.g. the sponsor, the executive) to understand the concept and context of the proposed project and to realize whether to approve and finance the project or not.
3.1.1 Introduction
Task Manager is basically used for managing task, system monitoring and start up manager included with systems. It provides limited information about computer performance and running applications, processes and CPU usage, memory information, network activity and statistics, logged-in users and system services. The Task Manager can also be used to set process priorities, processor affinity, forcibly terminate processes, and shut down, restart, hibernate, or log off from system.
Each operating system has its own task manager which control its task, monitor them and organised them in optimal way by using appropriate system calls but in our project we are developing an advance application which can monitor task of other system along with its own, by using our application user can control task of other operating system along with its own. Such as a user can manage Ubuntu task by using Android or android task by using Ubuntu. User has to ask for permission to another system if he or she want to connect with that system. If permission has granted then user can monitor the task of another system by using his/her own device. We have provided password protected connectivity, task monitoring of another system, multiple platform connectivity from single device, connection of different system using sockets.
User can kill process or task of his or her own system or process of another device, monitor CPU usage of different system, check graph of CPU usage, check memory utilization of system, create or start new process of his or her own system along with other system irrespective of operating system that system have and user can also change the priority of task of his or her own system along with another system. Our task manager user system calls and sockets of different operating system to provide all the functionality that we have mentioned. We have used different technology and tools to achieve our goal. Till now we have developed remote task manager for Android and Ubuntu and we will extend our project with functionality of other operating systems also such as IOS and windows in coming future. We can even use statically approach by using R-language to extend the functionality of our application in future
3.1.2 Scope
We provided the delay management by using proper data structure to store the information of task in optimised way. We will extend our application for windows as well as iOS systems. Enable user to provide priority to task according to their need. We will manager memory usage by managing the background task. If there is some task which is not used in long time we will kill that process automatically. This will make our application fast and memory management easier. We will classify application by using advance neural network and machine learning. We will predict the approximate memory usage, CPU utilisation and burst time for any application before it even start. We will extend the connection on internet along on the LAN to provide greater connectivity and functionality. We will auto detect the available device in our surrounding and able to provide a stable connection with them. We also used the firebase to provide connectivity over internet, which will enable user to access the remotely from any corner of the world.
3.1.3 Overview
Nowadays, we don’t have any appropriate cross platform remote task manager, which is able to connect different devices with different operating system, we don’t have any task manager which can be operated remotely with internet so that an user could be able to monitor the task of the other devices. But now we are developing a true cross platform remote task manager system with help of which a user will be able to monitor the task of the other devices it means he or she will be able to monitor, kill, create, run and operate task of other devices remotely.
To achieve our goal, we are developing stand alone application for windows and ubuntu, mobile application for android and also provide connectivity through google firebase so that user will be able to monitor task through internet. Since privacy and security are major factor in developing any application, therefore we have provided password protected connectivity. In password protected connectivity, user have to provide the right password in order to access a device remotely, so data will remain secure and it will prevent unauthorized person to access the application. We also provided the CPU and memory usage in order to monitor the use of different task. This will be beneficial in optimal use of battery as well as memory. we have also provided the graphical representation of CPU and memory usage so that user will be able to understand it more clearly.
3.1.4 Overall Description
The requirement analysis and specification phase starts once the feasibility study phase is completed and the project is found to be financially sound and technically feasible. The goal of the requirement analysis and specification phase is to clearly understand the customer requirement and to systematically organize these requirements in a specification document called Software Requirement Specification (SRS).
3.1.4.1 Software Requirements
- Android Studio
- Virtual Box with Ubuntu 14.04
- Python 2.7
- Glade
- JAVA 1.8
- Gedit
- Brackets
- Photoshop
- Firebase console
- Web Browser
3.1.4.2 Hardware Requirements
- 4 GB RAM
- 40 GB hard disk
- 1280 * 800 minimum screen resolution
- Android phone
- Internet supported system(for web application)
3.1.4.3 Functional and Non Functional requirements
A functional requirement describes what a software system should do, while non- functional requirements place constraints on how the system will do so. The functional requirements are describing the behaviour of the system as it relates to the system’s functionality. The non-functionality requirement elaborates a performance characteristic of the system.
3.1.4.3.1 Functional Requirements
- Interaction with different operating system.
- Data transfer between multiple devices having different operating system.
- Kill, modify, update and provide priority to the task of same or another system.
- Display current status of tasks, their CPU usage and other properties.
- Access must be password protected.
- Displaying graphs and resource usage.
- Real time processing of data.
- Implementing proper management of data by using appropriate data structure.
- Remote access with help of google firebase.
3.1.4.3.2 Non-Functional Requirements
- Data related to task must be processed in optimised way.
- Socket must be implemented for transferring the data across the systems.
- Information must be reliable.
- Security must be considered while developing the application.
- User access control must be considered decently.
- Maintenance and portability are the important factor for this application.
3.1.4.4 Product Perspective
This subsection of the SRS should put the product into perspective with other related products. If the product is independent and totally self-contained, it should be so stated here. If the SRS defines a product that is a component of a larger system, as frequently occurs, then this subsection should relate the requirements of that larger system to functionality of the software and should identify interfaces between that system and the software.
A block diagram showing the major components of the larger system, interconnections, and external interface scan is helpful.
- Activity Lifecycle in Android
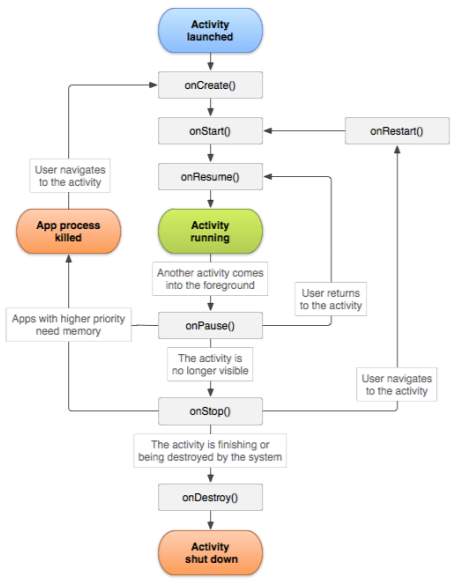
Fig 1 : Android life cycle
- Flow of execution for android
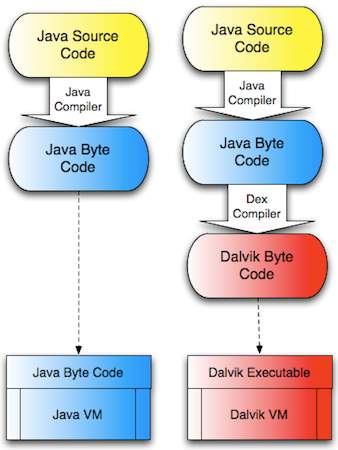
Fig 2 : Flow of execution for android
- Real time data transfer
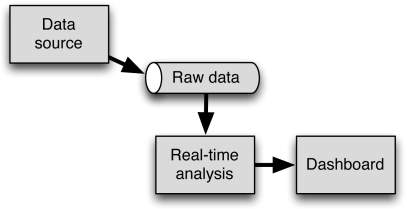
Fig 3: Real time data transfer
- Client and server connection through TCP
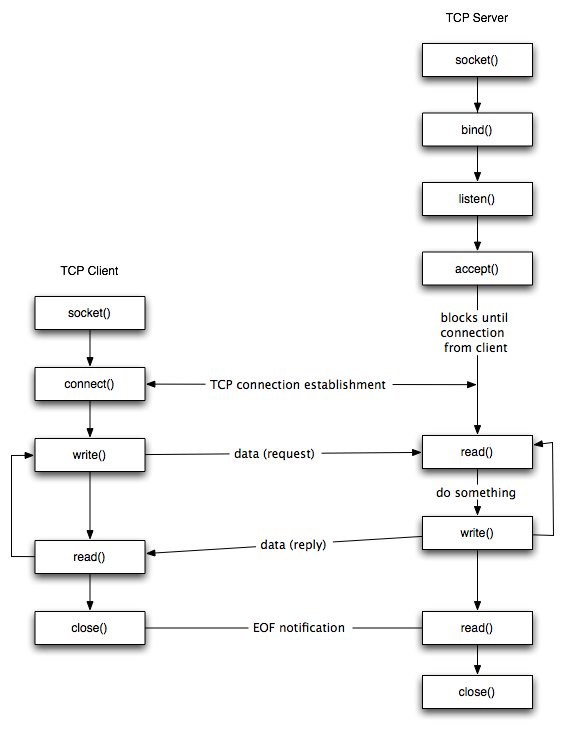
Fig4:TCPconnection
3.2 Modified Design
This section presents the design and overlook of the actual application and its various phases. Fig 5 represents the starting page of the application, by clicking the start button user will see further operation of the application. In Fig 6 user will enter the ip of other device to establish the connection. In fig 7 show the online version of the application where user sign in abd by doing will be able to access the application through firebase. Fig 8 show the graphical representation of the CPU usage and memory usage of the respective device. Fig 9 show the main page of the application where task are shown. User can kill and monitor task using this user interface. Fig 10 show the ubuntu functionality, where user set up the connection using ip. Fig 11 show the task of other devices by using sockets. Fig 12 show the task CPU and memory usage graph on ubuntu system.
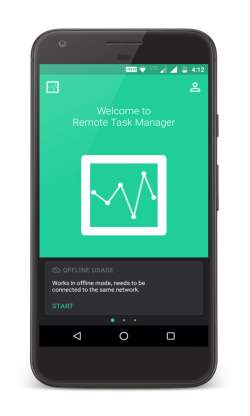
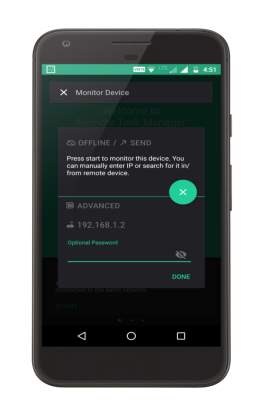
Fig 5: Offline Starting Page Fig 6: IP Configuration Page


Fig 7: Google Login Fig 8: Graphical Representation

Fig 9: Task Representation
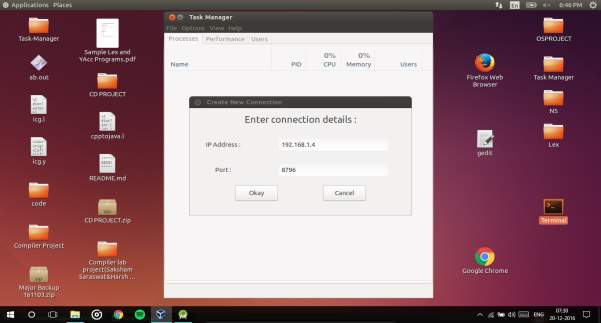
Fig 10: Establishing connection in ubuntu
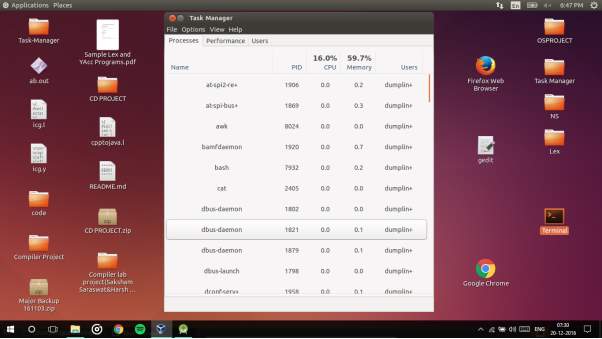 Fig 11: Getting data from other devices
Fig 11: Getting data from other devices
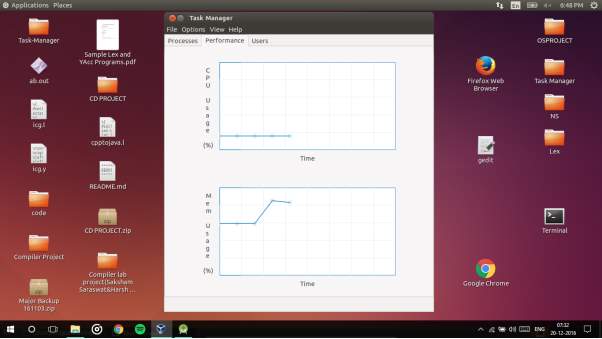
Fig 12: Graph for CPU and memory usage.
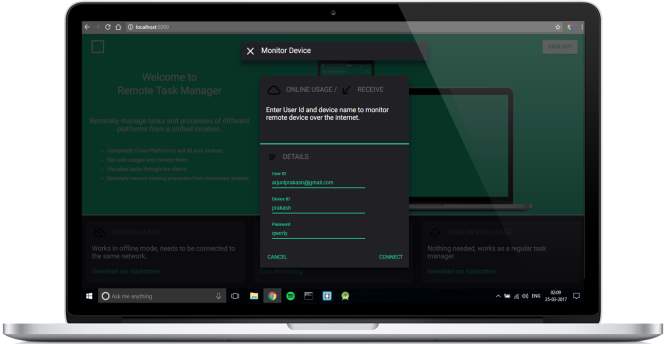
Fig 13 : Website Image
3.3 Implementation Detail and Issues
Design documentation is description of software product, that a software designer writes in order to give a software development team overall guidance to the architecture of the software project. An SDD usually accompanies an architecture diagram with pointers to detailed feature specifications of smaller pieces of the design. Practically, the description is required to coordinate a large team under a single vision, needs to be a stable reference, and outline all parts of the software and how they will work.
3.3.1 Use Case Diagram
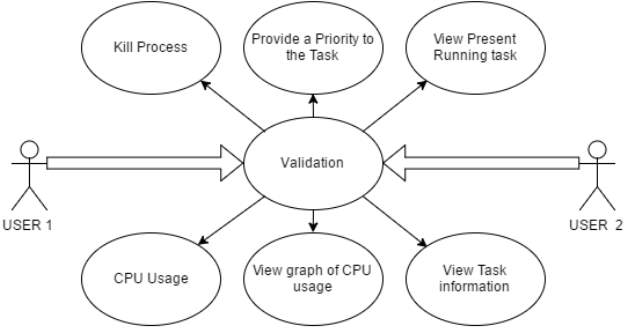
Fig 14 : Use case diagram
3.3.2Flow Diagram
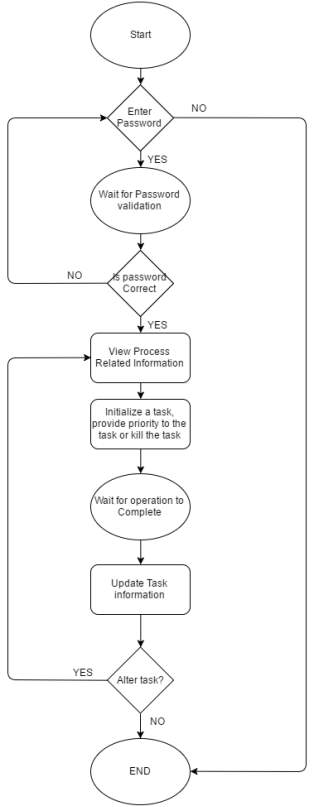
Fig 15: Flow Diagram
3.3.3 Sequence Diagram/Activity diagrams
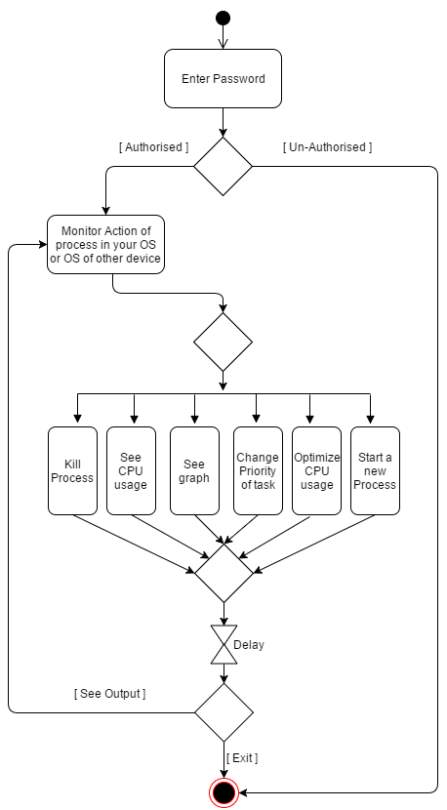
Fig 16: Activity Diagram
Chapter-4 Implementation details and issues
4.1 Issues
Issues are problems that are associated with one’s application. It may be related to the performance as well as implementation of the application.
User Level: It is require for user to have little bit idea about ip address to access our application, which might be a issue for a layman. Our application don’t have auto detect facilities, so it is not able to detect other devices by itself. User have to provide ip address explicitly.
Kernel Level: we used system calls to get the data about task/process from operating system. When kernel share the task information with application it undergo some error i.e. loss of data and infected information. So recovery of the lost information or infected information take time which leads to delay the application.
4.2 Implementation
To do an adequate job on security, a systems analyst must analyze the risk, exposure, and costs and specify measures such as passwords and encryption to provide protection. The backup copies of software and recovery restart procedures must be available when needed.
SECURITY AGAINST UNAUTHORIZED ACCESS:
- Use of administrator passwords:
The password provides security to the administrator of Associates user so that unauthorized user cannot access the facility of Associates User.
- User related checks and validations:
For this software, the developer uses user related checks and validations from the user.
- User authorization keys:
Password checking for logging of Users.
SECURITY AGAINST DATA LOSS:
Provision of efficient data backup system : In this software an efficient system is used for adequate backup facility .
Offline data storage: This system is capable for offline data Storage.
Multiple database backup: the efficient system is use for this Software to give multiple data backup.
User Level: User are does not change the task information, only monitor data. Its only View Information and its allowed after entering the password. A system is sending its data through sockets to another device after proper authentication. User can change priority and kill the process according to his/her requirement.
Kernel Level:
To design our application we needed some system data from kernel. We used system calls and commands to achieve our goal. We run our system calls in the back end and access the information provided by the operating system. We use these information to display our result in optimised way.
4.3 Risk Analysis and Mitigation Plan
| Risk ID | Description of Risk | Risk Area | Probability
(P) |
Impact
(I) |
RE
(P*I) |
Risk Selected for Mitigation (Y/N) | Mitigation Plan (if Y) | Contingency Plan (if N) |
| 1 | Making
User Interface Thread Safe |
User-Interface | M | H | 15 | Y | Uses GLib tools instead of traditional threading | |
| 2 | Size of files too big to send | Back-end | M | M | 9 | Y | Reduce the size for faster sending | |
| 3 | Activity monitoring
And data retrieval |
Back-end | M | M | 9 | Y | Look for API call that interface with the devices | |
| 4 | Data overload
And data congestion |
Back-end | L | L | 1 | N | Congestion avoidance algorithm |
Table 2: Risk analysis
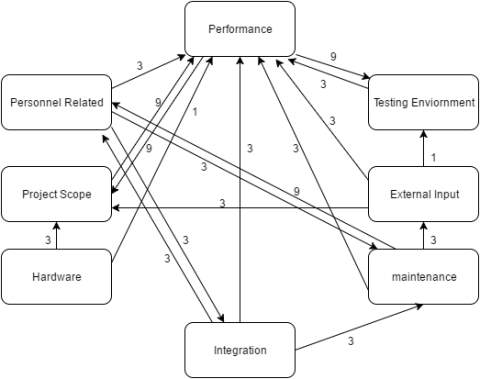
Fig 17: Weighted Interrelationship Graph of Project
| S.N | Risk Area | # of Risk Statements | Weight(In & out) | Total Weight | Priority |
| 1 | Performance | 9 | 3+9+1+3+3+3+9 | 31 | 1 |
| 2 | Project Scope | 4 | 9+3 | 12 | 2 |
| 3 | Maintenance | 4 | 9+3 | 12 | 3 |
| 4 | Personnel Related | 3 | 3+3 | 6 | 4 |
| 5 | Testing | 3 | 1+3 | 4 | 5 |
| 6 | Integration | 3 | 3 | 3 | 6 |
| 7 | External Input | 4 | 3 | 3 | 7 |
| 8 | Hardware | 2 | 0 | 0 | 8 |
Table 3: Risk Detail
Chapter-5 Testing
Software testing is a process of executing a program or application with the intent of finding the software bugs. It can also be stated as the process of validating and verifying that a software program or application or product meets the business and technical requirements that guided it’s design and development. Works as expected. Can be implemented with the same characteristic.
Let’s break the definition of software testing into the following parts:
1) Process: Testing is a process rather than a single activity.
2) All Life Cycle Activities: Testing is a process that takes place throughout the SDLC.
5.1 Testing Plan
The test plan includes testing the formulated algorithm against various benchmark functions. It also includes testing the algorithm on various data sets and comparing the results of various already proposed algorithms.
| Type of Test | Will Test be Performed | Comments/Explanation | Software Components |
| Requirement Testing | Yes | This is to keep track whether the application is developed as per requirements. | All modules |
| Unit | Yes | To check whether all units are working as intended. | Applied toall modules |
| Integration | Yes | To check if integration of all individual module is successful.(the code has been integrated) | Applied toall modules |
| Performance | Yes | The performance of project is up to the mark or not | All modules |
| Time | Yes | Whether the distance is minimized or not | Distance calculating module |
| Comparison | Yes | Result received is good or bad as compared toother results | Main module |
| Security | Yes | Security plays a major role | The implemented project is secure. |
| Load | Yes | Load due to sockets overheads in the application. | All module. |
Table 4 : Test detail
5.2 Component decomposition and type of testing required
| Role | Name | Specific Responsibility/Comments |
| Android Client | Arjun Prakash | Android which handles client side of application in android. |
| Python Client | ShivamPandey | Python code which deals with the client side of the application. |
| UI Design (Ubuntu) | Shivam Vijay | Design the UI in ubuntu using GTK Lib. |
| UI Design (Android) | Arjun Prakash | Design the UI in Android. |
| Research | Arjun Prakash, ShivamPandey, Shivam Vijay | Study the research papers and read about the implementation of the projects on internet. |
| Requirement Gathering | ShivamPandey | Determine the software requirement of the application. |
| Algorithm Design | Shivam Vijay | Optimise the data handling received from operating system. |
| Android Server | Arjun Prakash | Android which handles server side of application in android. |
| Python Server | ShivamPandey | Python code which deals with the server side of the application. |
| Socket Handling | Shivam Vijay | Receiving and sending data through sockets. |
| Optimization | Arjun Prakash, ShivamPandey, Shivam Vijay | Code optimisation, memory optimisation. |
| Asset Design | ShivamPandey | Used Photoshop to design logo. Used rational rose to design various UML. |
| Content Design | Arjun Prakash | Data portrait to the user and description of the application. |
| Code Conversion | Shivam Vijay | Converted c code into python. |
| Documentation | ShivamPandey
Arjun Prakash |
Documentation designing and analysis. |
| C code | ShivamPandey, Shivam Vijay | C code implementation of the code. |
| Google-firebase | Shivam Vijay
Arjun Prakash |
Manage database for management of task remotely. |
| Google-firebase website | ShivamPandey | Website to operate task of different device remotely through firebase. |
| Android UI improvement | Shivam Vijay | Addition of more functionality to application. |
Table 5 : Team Detail
5.3 Test Schedule
| Activity | Start Date | Completion Date | Hours | Comment |
| Synopsis | 08/25/16 | 09/02/16 | 22 | Entire process require some information gathering. |
| Task Manager in c for ubuntu | 09/15/16 | 09/29/16 | 64 | We implemented task manager in c for ubuntu. |
| Code optimisation | 10/01/16 | 10/18/16 | 33 | Optimise the c code |
| Initial Documentation | 10/10/16 | 10/18/16 | 25 | Documentation for Mid evaluation |
| Demo Connection of ubuntu with android | 10/05/16 | 10/18/16 | 20 | Basic code written in android. |
| Conversion of c code into python | 11/03/16 | 11/20/16 | 60 | Due to compatibility problem entire c code is converted in python |
| Analysis of python code and adding functionality | 11/20/16 | 11/30/16 | 41 | Integrate the functionality into python code |
| Android code development | 12/01/16 | 12/18/16 | 50 | UI of android and activity development in android |
| Entire Code integration | 12/01/16 | 12/18/16 | 40 | Connectivity between different operating system |
| Documentation | 12/06/16 | 12/19/16 | 40 | Entire Documentation |
| Discussion | 10/01/17 | 15/01/2017 | 30 | Further discussion and enhancement of project |
| Android UI Enhancement | 17/01/2017 | 30/01/2017 | 60 | Entire user interface was changed in more appropriate way. |
| Android application Integration | 01/02/2017 | 08/02/2017 | 30 | Integration of entire android application |
| Android Application Testing | 17/02/2017 | 25/02/2017 | 43 | Testing of android application. |
| Google firebase | 27/02/2017 | 10/03/2017 | 45 | Understanding and integration of google firebase. |
| Website | 15/03/2017 | 21/03/2017 | 45 | Website for firebase. |
| Mid evaluation documentation | 21/03/2017 | 24/03/2017 | 36 | Documentation of report |
Table 6: Test Schedule
5.4 Test Environment
5.4.1 Software Item
Operating System:We used ubuntu, android and windows operating system as our testing environment.
Tools :We used JDK1.8 for java program testing and Android studio for android application testing. We also used android phone for testing. We used virtual machine for running the ubuntu system where we done the testing of ubuntu application. we used google chrome and opera for website testing.
5.4.2 Hardware Item
- Hard disk of 40 GB space.
- RAM of 4 GB.
- Laptop with HD resolution.
- Router for internet connection.
- Intel I5 4th generation processor.
5.5 List of All test case in Prescribe Format
| Test Case ID | Input | Expected o/p | Status |
| 1 | Valid IP | Validation | Pass |
| 2 | Valid Port | Validation | Pass |
| 3 | Valid Password | Validation | Pass |
| 4 | CPU Usage | Percentage of CPU usage | Pass |
| 5 | Memory Usage | Percentage of memory usage | Pass |
| 6 | Task of same Machine | Task Detail | Pass |
| 7 | Task of same machine | Kill Task | Pass |
| 8 | Task of same
machine |
Priority | Fail |
| 9 | Task Other device | Task Detail | Pass |
| 10 | Task Other device | Kill Task of other device | Pass |
| 11 | Task Other device | Provide Priority to task of other system | Fail |
| 12 | Firebase Implementation | Task are accessible through firebase. | Pass |
| 13 | Website for firebase | Task accessible through website by using firebase. | Pass |
| 14 | Online functionality integration. | User will be able to sign in through google account to access their task remotely. | Pass |
| 15 | Coding in C | Proper functioning. | Fail |
Table 7: Test case for Different Component
5.6 Error and Exception Handling
| Test Case ID | Test Case | Debugging Technique |
| 8 | Unable to provide task of same machine. | Not Possible |
| 12 | Unable to provide task of other machine. | Not Possible |
| 15 | No Scalability | Post-Mortem |
Table 8 : Debugging Table
5.7 Limitations of the solution
- Android has persistent task, so even if we kill those tasks, they are again started by the operating system. Android is not giving us permission to kill those tasks.
- Till now, we are not able to provide priority to different task according to user choice.
- System delay is one of the major factor. Since we used system calls for getting information from operating system, so there may be possibility of some delay due to false information and loosing of information in the path.
- We are not able to propose solution for iOS.
- Memory management is not optimal in our project.
Chapter-6 Findings and Conclusion
6.1 Findings
- Given the program we can calculate its CPU time, file input/output time and the memory requirement before execution. The predictions were made on the basis of previous execution of the program.
- In real-time interactive application development model on the Android platform, the information of server can be displayed in real time to the android device, and user can operate according to the real-time situation.
- Multiple OS could be connected by making proper use of sockets. Connection android and ubuntu through socket is easy because both developed on the same platform i.e. Linux.
- Irrespective of scheduling algorithm, there always be some probability of delay or error in getting data from OS kernel.
- In android task are persistent, so even if you kill them, OS will retrieve its task all by itself again.
- Activity Manger Services(AMS) helps to receive and respond to user requests. AMS is the first service that boots up during the launch of an application.
6.2 Conclusion
Task Manger is operating system tool to control task, monitor CPU usage of task, monitor memory usage of task manger, kill and create process. Every operating system has its own task manger to manage task.
We develop the enhance version of task manger that we have right now. Our task manager works on android as well ubuntu operating system. User can control task, kill process, monitor CPU usage, monitor memory usage and manage background task of ubuntu system from his/her android system and also can control task, kill process, monitor CPU usage, monitor memory usage and manage background task of android system from his/her ubuntu system. User can control or manipulate task of his/her own android as well as ubuntu system along with other ubuntu or android system.
We used google firebase to provide facility of remote task access through internet. One can login through google account and use firebase to tp access their task or manage them in proper way. To provide the functionality of firebase we design a website, which is also password protected and will be used to access the task through internet.
Entire connection is established with the help of sockets, we sockets to transfer data between different system. Here sockets act as a door way between different system. We also keep track of security from user point of view. No one can access remote system without its permission. Users have to enter the password the system they want to access before monitoring that system.
We have used different technology while developing this application i.e. android, python, GTK, glade and java. We ran multiple testing to check weather our application is working fine or not. We have provided the proper user interface for users, so that even person from non programming background could use our application. We have used GTK library for developing UI for ubuntu system. In android we have inbuilt UI. We have provided the user interface for both desktop or stand alone application and mobile devices.
Task management is the process of managing a task through its life cycle. It involves planning, testing, tracking and reporting. Task management can help either individuals achieve goals, or groups of individuals collaborate and share knowledge for the accomplishment of collective goals. Tasks are also differentiated by complexity, from low to high. Our application only work for ubuntu as well android based system, we will extend the functionality of our for windows and iOS also in future.
6.3 Future Work
- Delay management by using proper data structure to store the information of task in optimised way.
- We will extend our application for windows as well as iOS systems.
- Enable user to provide priority to task according to their need.
- We will manager memory usage by managing the background task. If there is some task which is not used in long time we will kill that process automatically. This will make our application fast and memory management easier.
- We will classify application by using advance neural network and machine learning. We will predict the approximate memory usage, CPU utilisation and burst time for any application before it even start.
- We will extend the connection on internet along on the lan to provide greater connectivity and functionality.
- We will auto detect the available device in our surrounding and able to provide a stable connection with them.
References
[1] Optimized Chat Server Protocol for Server Side Scripting Languages: 2010.http://ieeexplore.ieee.org/document/5578709/ . Accessed: 2010-08-01.
[2] A Study of High-Performance Communication Mechanism for Multicomputer Systems:1996.http://ieeexplore.ieee.org/document/508042/ . Accessed: 2014-11-21.
[3] Predictability of Process Resource Usage: A Measurement- Based Study on UNIX:1989. http://ieeexplore.ieee.org/document/58769/. Accessed: 2010-08-01.Accessed: 1989-12-11
[4] Research and Design of a Real-time Interactive Application Development Model Based on the Android Platform :2013.http://ieeexplore.ieee.org/document/6804804/ . Accessed: 2013-07-10
[5] A Memory Management Scheme for Enhancing Performance of Applications on Android: 2013.http://ieeexplore.ieee.org/document/7488407/ .Accessed: 2013-06-22
[6] A Software Component for Network Based Data Acquisition and Control Applications: 2006.http://ieeexplore.ieee.org/document/4350346/ .Accessed: 2006-09-24
[7] Design and Implementation of Remote Control System between Android Platform:2016. http://ieeexplore.ieee.org/document/7816692/. Accessed: 2016-09-24
[8] Design and Implementation of an Application with android with remote management of a smartphone:2015.http://ieeexplore.ieee.org/document/7152090/ . Accessed: 2016-06-15
[9] Web Link Reference:
https://developer.gnome.org/gtk3/stable/
Objective:
Gnome GTK documentation.
[10] Web Link Reference:
https://www.youtube.com/results?search_query=android+ui+design+tutorial
Objective:
Video Tutorial
[11] Web Link Reference:
https://developer.android.com/training/basics/firstapp/index.html
Objective:
Android documentation
[12] Web Link Reference:
https://glade.gnome.org/
Objective:
Glade documentation.
[13] Web Link Reference:
https://www.tutorialspoint.com/java/java_basic_syntax.htm
Objective:java tutorial
[14] Retrieved from https://en.wikipedia.org/wiki/Android_(operating_system)
[15] Retrieved from https://en.wikipedia.org/wiki/Python_(programming_language)
[16] Retrieved from https://www.java.com/en/download/faq/whatis_java.xml
[17] Retrieved from https://glade.gnome.org/
[18] Retrieved from https://en.wikipedia.org/wiki/Firebase
[19] Retrieved from https://en.wikipedia.org/wiki/Qt_Creator
Appendix A
| TASK (Semester 7) | PERSON | DATE |
| RESPONSIBLE | ||
| Project Discussion | Group | 25.08.2016 |
| Synopsis | Group | 26.08.2016 |
| Requirement | ||
| Gathering | Group | 31.08.2016 |
| Working Prototype | Group | 19.09.2016 |
| Timeline of project | Group | 20.09.2016 |
| Designing | Group | 02.10.2016 |
| Implementation | Group | 05.12.2016 |
| Debugging | Group | 07.12.2016 |
| Testing | Group | 15.12.2016 |
| Partial Completion | Group | 19.12.2016 |
Table 9 :WorkPlan(Odd Semester)
| TASK (Semester 7) | PERSON | DATE |
| RESPONSIBLE | ||
| Project Discussion | Group | 10.01.2017 |
| Synopsis | Group | 17.01.2017 |
| Requirement | ||
| Gathering | Group | 25.01.2016 |
| Working Prototype | Group | 08.03.2016 |
| Timeline of project | Group | 25.03.2016 |
| Designing | Group | 10.04.2016 |
| Implementation | Group | 15.04.2016 |
| Debugging | Group | 27.04.2016 |
| Testing | Group | 02.05.2016 |
| Partial Completion | Group | 11.05.2016 |
Table 10 :WorkPlan(Even Semester)
Cite This Work
To export a reference to this article please select a referencing stye below:
Related Services
View allRelated Content
All TagsContent relating to: "Information Technology"
Information Technology refers to the use or study of computers to receive, store, and send data. Information Technology is a term that is usually used in a business context, with members of the IT team providing effective solutions that contribute to the success of the business.
Related Articles
DMCA / Removal Request
If you are the original writer of this dissertation and no longer wish to have your work published on the UKDiss.com website then please:




