Audio Steganography Technique for Communication Security
Info: 8339 words (33 pages) Dissertation
Published: 30th Nov 2021
Tagged: Communications
Chapter 1 INTRODUCTION
1.1 Introduction
As the need of security increases encryption needs a more secure method to hide the confidential matters. So stegnograpghy is the supplementary to encryption. It is not the replacement of encryption. But Steganography along with encryption gives more security to data. The word STEGANOGRAPHY is Greek word which means “concealed writing” from the Greek words stegnos meaning “covered or protected”, and graphei meaning “writing”. Steganography is the technique to hide the information in audio, image or video so that others can’t identify that information is hidden into that media. That media can be an audio, text, image or video. The information that to be hidden is called stego and the media in which the information is hidden is called host. The stego object can be text, image, audio or video. When the information is hidden into the audio then it is called Audio steganography. This process is described as selection of random samples to be used for embedding which may introduce low power additive white Gaussian noise (AWGN).
1.2 Objectives
A. Steganography
It is a technique of hiding information. Hideing necessary information by applying this steganography approach without causing any affect to the information is possible. Once the information is hidden, it cannot be identified easily.
B. Cryptography
It is a technique of converting plain text into cipher text. It is possible to encrypt highly secure data by applying cryptography approach. This approach helps to convert data in such a way that it can’t be understood. Only the authorised user can decrypt the encrypted data.
An effective steganographic scheme should posses the following desired characteristics for a secured transmission of message signal:
Secrecy: Disabling aperson to extract the covert data from the host medium without the prior knowledge of the proper secret password or key which is used in the extracting procedure.
Imperceptibility: The medium after being embedded with the covert data should be indiscernible from the original medium. One should not be so suspicious of the existence of the covert data within the medium.
High capacity: Highest length of the covert message that can be embedded should be as long as possible case can handle.
Resistance: The covert data should survive even when the host medium has been manipulated, for example by some lossy compression scheme .
Accurate extraction: The retrival of the covert data from the medium should be accurate and reliable.
1.3 Motivation
It is said that the steganography approach was first practiced during the Greece Empire. History of ancient Greece specifies that they practices melting wax off wax tablets and then they hides the message in the underlying wood. As the message was hidden under the wax, hence no one can have any suspect about the hidden message. Later on a microdot technique has been introduced for hiding secret messages. Microdots were used to permit the transfer of large amount of data and drawings invisibly. After that the concept of invisible ink came into existence and was much popular till world war-II. Certain drawbacks have been identified in such techniques and new hiding techniques has put forward time to time.
Since ancient ages, encryption is the popular approach for transferring important data securely. An encryption technique has been evolved since the Babylonian Era, and was evolving continuously as they were used in the military and political aspects. Hieroglyphics is the oldest encryption technique. Later, Scytale Cipher technique was used which involves use of cylinder and a parchment strip so that the text can be written on that strip. Caesar Cipher was another encryption technique which involved shifting of characters to encrypt the data. Substitution Cipher and Enigma are the most popular encryption techniques in the history of encryption. Every time an encryption technique introduced, someone finds out a decryption method for that. Hence considering drawbacks in existing techniques, newer techniques have been introduced day by day.
1.4 Problem statement
A a best secure technique which can implement audio data hiding using LSB algorithm. Thus we need an audio data hiding technique that can be used for a number of purposes other than covert communication or data storage, data tracing and finger printing. The sky is not the limit so is the same for development. Man is now decreasing his own boundaries to make every possible thought. So various operations described can be further modified as it is in the world of Information Technology.
1.5 Proposed Methodology
Different information hiding techniques are proposed to embed secret information. Among them we choose with audio file, Least Significant Bit (LSB) coding method as it is the simplest way to embed secret data in a digital audio file by replacing the least significant bit of audio file with a digital converted secret message. Hence LSB technique allows huge amount of secret data to be encoded into an audio file.
Steps to hide secret information using LSB are:
a. Conversion of the audio file into bit stream that is digitalization.
b. Convert each and every character in the secret message into digital bits.
c. Replace every LSB bit of audio file with every LSB bit of character in the secret message.
This method which is proposed thus provides great security and it is the best method for hiding the secret data from hackers and sent to the destination in an undetectable manner. This proposed system ensures that the quality of the file is not changed even after such encoding and it is made suitable for all types of audio file formats.
1.6 Overview of the project
Steganography is the science of hiding secret data in a cover file so that only sender and receiver can be able to detect the existence of the secret data. The main aim of our steganography technique is to communicate with full security with a completely undetectable manner and thus avoiding drawing suspicion to any intermediaries present transmission for a hidden data. It is not only prevents others from knowing the hidden information, but it also prevents others from thinking that the information even exists. If a steganography method makes intermediaries to doubt suspection that there is a some information in a carrier medium, then the method has failed. This technique Audio steganography consists of Carrier signal (Audio file), Message (text) and Password (key). Carrier is the cover-file, which conceals the secret information. Basically, the technique for audio steganography is shown in figure below. Message is the data type which the sender wishes to remain it to be confidential. Message may be a plain text, image, audio or any type of file. Password is the key, which ensures that only the recipient who knows the corresponding decoding key will be able to extract the message from a cover-file or else they can not retrive the file. The cover-file with the secret information is known as a stego-object in this audio steganography technique.
For hiding data into a medium the requirements are:
- The cover audio signal(C) that will holds the hidden data
- The secret message data (M), may be plain text, cipher text or any other type of data
- The stego or covered technique (Fe) and its inverse (Fe-1)
- An optional stego-password (K) is used to hide and during retrivalof the message.
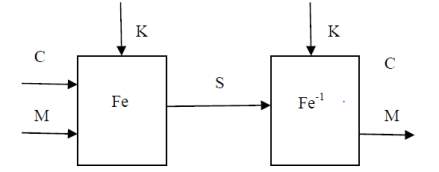
Figure 1: The Steganographic operation
Chapter 2 LITERATURE SURVEY
In recent years, several researchers have been developing algorithms for hiding data in an audio signal. Jisna Antony et al discuss about different audio steganographic techniques available in different domain. Lot of work is done in all these domains. Baritha and Venkataramani propose a new dictionary based text compression technique. Compression bits are hidden into the LSB bit of audio signals. In this secret message text is hidden or covered using an identifier or an algorithm. Identifier is hidden in audio along with it’s length and width. Identifier indicates if there is a hidden secret text or not.
This project is implemented in temporal domain. Ahmad Delforouzi and Mohammad Pooyan provides an algorithm or a method which embeds secret data in temporal domain. In this algorithm first estimate the embedding threshold in the time domain. Then it is used for data concealment in the time domain. Audio steganography’s drawback is in the temporal domain even though it is easy to hide data; it lacks security as well as has less hiding capacity compared to hiding in wavelet domain. Dora and Juan provides a new scheme of data hiding which takes advantage of the masking property of the Human Auditory System (HAS) to hide a secret (speech) signal into a host (speech) signal. In embedding process, the wavelet coefficients of secret signal are sorted and embedded again in the host signal wavelet coefficients. And their original positions are used as key. Delay is inserted in each cycle to achieve synchronization. This approach takes much time; the retrieved back secret signal is not same as the same as the original because there is error in reconstruction of host signal. Also it is evident that there is a need to store the positions of frames in stego signal, thus it reduces the hiding capacity of the host signal. Yongfeng Huang et al , proposed an algorithm which performs data embedding while pitch period prediction is conducted. Embedding the secret message data is done during low bit rate encoding. The technique’s drawback is that stego audio has been detected in steganalysis. Parul Shah et.al, developed an algorithm where modification of host audio is done by imposing a constraint which forces the modified value to be in the same range as its neighbourhood.
In this project, host signal is decomposed using wavelet packet up to third level, then selected band coefficients are sampled and then converted to 2D. This 2D matrix is then divided to 2X2 non overlapping blocks used to embed covert data using pseudorandom sequence. The secret data is embedded into host based on the trend mapping. Sajad Shirali-Shahreza and M.T. Manzuri-Shalmani proposed an audio steganography algorithm to hide text which uses lifting scheme to create perfect reconstruction. This secret data is to be stored based on the details coefficient value. For calculating the number of bits to hold data in a coefficient with value ‘c’, the biggest power of 2 named ‘p’ which is smaller than ’c’ i.e., 2p_ c
2.1 RELATED WORK
The primary tool used in the research of steganography and watermarking is the Internet. The first objective was to understand the various terminologies related to the field.
The following points can be attributed to the renaissance of steganography:
- Government ban on digital cryptography. Individuals and companies who seek confidentiality look to steganography as an important complementary since combining cryptography and steganography can help in avoiding suspicion and protect privacy.
- The increased need for protecting intellectual property rights by digital content owners, using efficient watermarking.
- The trend towards electronic communications and humans desire to conceal messages from curious eyes. With rapid advancement in technology, steganographic software is becoming effective in hiding information in image, audio or text files.
2.2 EXISTING APPROACH
In an equal interval of time, several concepts has been brought forward in order to provide an optimum solution to ensure security, privacy and authentication of the information while carrying out data transfer over network. These concepts involved certain data hiding and data encryption techniques. Considering security and privacy as a major concern, initially the vital data is to be sent after hiding it behind some digital media such as audio, video, images etc. This technique was quite popular, later on hackers found a way out, now it is possible to extract the hidden data from the digital media. With the advent in the field of cryptography, encryption becomes a gossiping fact among all. Afterwards encryption was used for the data transfer. This technique was better option among other but, only encryption or data hiding cannot provide full assurance towards the data. Recently, the concept of double layer protection technique has been put forward to fill this gap. The double layer protection technique is simply cryptography cum steganography approach which can definitely provide efficient security mechanism for transferring data among communicating parties.
The main disadvantage of using the existing methods is that there is an introduction of noise and decrease in robust-ness of the system.The human ear is highly sensitive to noise and can detect even small disturbances introduced due to steganography using the existing methods. In order to reduce noise introduction to a great extent we propose the following method of LSB modification.
2.3 MODIFIED APPROACH
The main goal of steganography is to communicate securely in a completely undetectable manner. Considering security to be a major aspect, the mostsuggested implementation is of a double layerprotection approach will helps user to send vital datawithout having any worry. We suggest an approach thatconstitutes both cryptography and steganography.We are considering a situation where user wants to share some sort of vital information with another party located over some distance. The medium of communication may be wired or wireless. Now the information that is to be sent should be delivered securely. So in order to achieve this, we are suggesting a system that will implement the double layer protection approach.
2.4 PROPOSED METHOD
The method we prpose is to hide encrypted text in cover audio signal. This method consists of two parts – embedding (or encoding) at the transmitter end and extraction at the receiver end. In embedding phase, encrypted text is hidden inside the cover audio signal. There is no distortion in the cover audio by hiding the secret data since only the LSB is being modified while keeping all other parameters unaltered. In extraction phase, the secret text is retrieved from the stego-object that is the audio file containing the secret data. Secret data here is text, which can be encrypted before embedding into the audio. These transformed values of text are then hidden in LSB’s of audio samples.
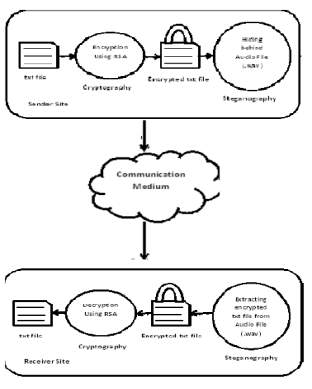
Figure 2. Proposed Method
This proposed method provides greater security and it is efficient method for hiding the secret data from hackers and sent to the destination in a safe and undetectable manner. This proposed system also ensures that the size of the file is not changed even after encoding and it is also suitable for any type of audio file format.
2.5.1 EMBEDDING PHASE
Step 1: Audio Processing
Perused the cover sound document. Sound specimens are put away in a vector and are marked skimming point values. At the point when a sound flag is changed to another area, then changed back to time space, the subsequent flag is not really whole number. So as to get number coefficients from sound specimens, sound examples must be changed over to numbers. This change is performed here.
Step 2: Apply LWT in light of lifting plan
This calculation utilizes whole number to whole number change which is executed utilizing lifting wavelet change (LWT). LWT utilizes Lifting Scheme (LS). In LS, among the different wavelets accessible, suitable wavelet is picked. As whole number coefficients are required, “int2int” change must be indicated. In light of the LS, apply the LWT to cover sound to get detail and guess coefficients, CD and CA individually. Change over CD to parallel.
Step 3: Calculate number of bits to be supplanted.
The quantity of bits used to hold information is ascertained utilizing the rationale clarified by Sajad Shirali- Shahreza and M.T. Manzuri-Shalmani. This calculation picks dynamic way to deal with discover the bits to hold the mystery content. Detail coefficients are chosen to hold the mystery content. Number of bits of CD to be supplanted (NBR) depends on the way that if the coefficient esteem is all the more, then changing more bits won’t bring about significant distinction in the flag. Thus, more mystery information bits are covered up in greater coefficients and less in littler coefficients.
Step 4: Read content record and scramble it.
Perused the content document. Locate the measure of the content to be covered up. The content is scrambled by subtracting ASCII estimation of each character by message measure. Figure content is then changed over to parallel string. Purpose for actualizing straightforward encryption system utilizing message size is that there is no compelling reason to shroud the encryption enter in cover sound. This permits more information to be covered up and furthermore gives security without diminishing the concealing limit.
Step 5: Embed the scrambled content.
This progression is sub separated into two sections: Hiding the measure of the content and concealing the real content. “Content” is likewise alluded as “message” in rest of the paper. It is important to install the mystery message estimate into the cover sound in light of the fact that amid extraction of content from stego-sound, beneficiary ought to know what number of bits must be separated from stego-sound. Likewise, recipient needs to decode the mystery content in light of message size. Initial 16 replaceable LSB’s are saved to store the message estimate, in light of NBR figured for each Compact disc esteem. Message measure bits, beginning from MSB, are put away in LSB’s of CD’s.
Shroud the real message
Staying replaceable bits of every CD are utilized to store the scrambled mystery message.Message bits beginning from MSB, are put away in LSB’s of every CD.
Step 6: Reconstruction of stego-sound flag.
Subsequent to inserting the mystery message into CD; utilizing CA and altered CD, stego-sound flag is recreated by applying backwards LWT. This stego-sound sounds same as the cover sound.
2.5.2 EXTRACTION PHASE
Step 1: Audio Processing
Perused the stego sound record. At that point change over the sound examples into whole numbers. This progression is same as step 1 in the implanting stage.
Step 2: Apply LWT in light of lifting plan
Select the same lifting plan which is utilized as a part of the implanting stage. In view of this LS, apply the LWT to cover sound to get detail and estimate coefficients, CD and CA separately. Change over CD to twofold.
Step 3: Calculate number of bits to be supplanted.
This is precisely same as step 3 in the implanting stage. Utilize same OBH esteem that is utilized as a part of the installing stage.
Step 4: Extract the shrouded message
This progression is sub separated into two sections: recover the extent of the message and recover the message. Recover message estimate. In view of NBR computed for every CD in step 3, 16 bits are recovered from LSB’s of CD’s to get the message measure.
Recover the message .Scrambled message bits beginning from MSB, are recovered from LSB’s of residual CD’s utilizing the message size and store it in a cradle.
Step 5: Decryption of message and composing it into a document.
In the wake of recovering, the encoded mystery message bits are changed over to decimal. Resultant message bits are then unscrambled utilizing extricated message size and changed over to character. This is again composed to a yield content document. Figure 3 portrays the extraction stage.
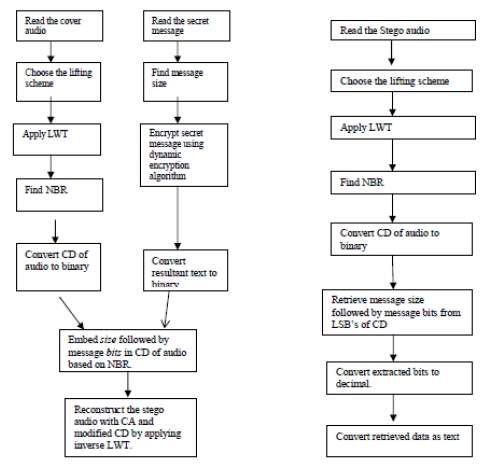
Figure 3. Embedded phase and Extraction Phase
Chapter 3 SYSTEM REQUIREMENTS
Implementation of Audio Steganography requires a message in text format which is to be sent, a carrier which is an audio file and then the basic computer requirements along with the MATLAB software.
3.1 Hardware Requirements
- A minimum of 300Mhz processor
- A minimum of 64 Mb RAM
- No strict specification about the hard disk.
3.2 Software Requirements
- Windows 9812000/XPplatform
- MatlabR2016a
- Wav file incase of data hiding in audio files, Bitmap/gif files in case of image files.
- Any file to embed(music, image etc.)
These are the various requirements that are needed.
Chapter 4 LSB TECHNIQUE IMPLEMENTAION
There have been many techniques for hiding information or messages in audio in such a manner that the alterations made to the audio file are perceptually indiscemible. Common approaches include :
4.1 LSB CODING
A very popular method is the LSB (Least Significant Bit) modification algorithm in which the least significant bit in some bytes of the cover file is replaced to hide a sequence of bytes containing the hidden data. That’s usually an effective technique in cases where the LSB substitution doesn’t cause significant quality degradation. In computing, the least significant bit (LSB) is the bit position (right most bit) in a binary integer giving the units value.
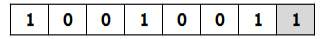
Figure 4: Binary representation of decimal 147
The binary representation of decimal 147, with the LSB highlighted is shown above. The MSB (1) in the 8-bit binary representation of the number represents a value of 128 decimal and the LSB (1) represents a value of 1. For example, to hide the letter “Z” (ASCII code 90, which is 01011010) inside eight bytes of a cover, the LSB of each byte could be modified like this:
00101010
01110011
00000010
10001011
11010011
10011010
01010011
10010010
During decoding the application reads the eight Least Significant Bits of the cover file bytes to recreate the hidden byte—that is 01011010—the letter “Z. In this method, each and every bit of the message byte is hidden into a cover byte. There is a fifty percent chance that the bit being replaced is the same as its replacement, in other words, half the time, the bit doesn’t change, which helps to minimize quality degradation.
Fig below illustrates how the message ‘HAI’ is encoded in a 16-bit sample of the cover file (audio file) using the LSB method. The secret information ‘HAI’ and the audio file are converted into bit streams and the least significant column of the audio file is replaced by the bit stream of secret information ‘HAI’.
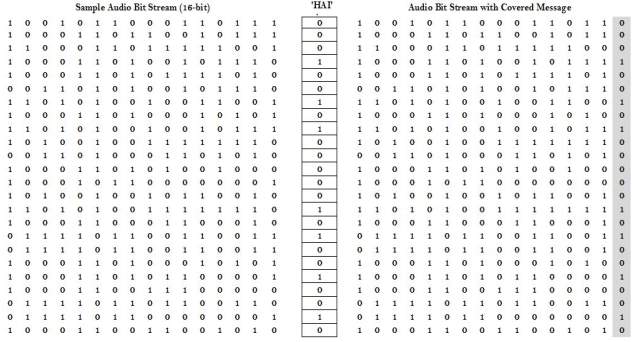
Figure 5. LSB coding example
Steganography can also be implemented using the other approaches as given below,but LSB technique is the best way with minimum BER.
4.2 PARITY CODING
Parity coding is one of the robust audio steganographic technique. Instead of breaking a signal into individual samples, this method breaks a signal into separate samples and embeds each bit of the secret message from a parity bit. If the parity bit of a selected region does not match the secret bit to be encoded, the process inverts the LSB of one of the samples in the region. Thus, the sender has more choice in encoding the secret bit. The parity coding procedure can be shown as follows:
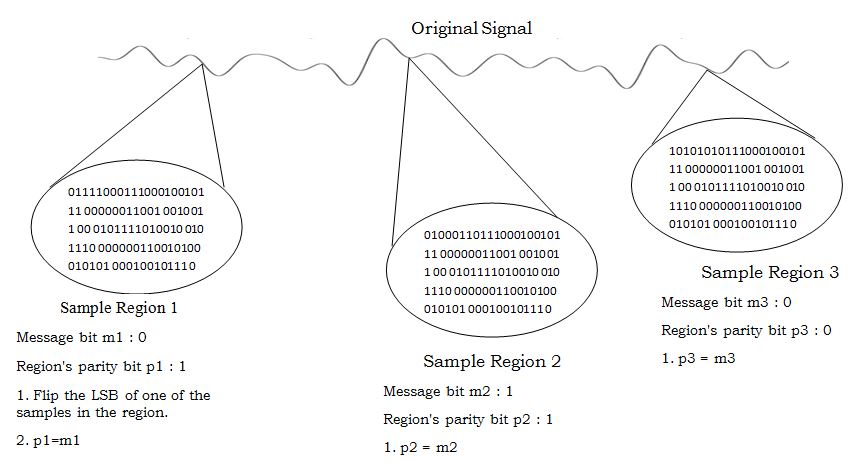
Figure 6. Parity coding
4.3 PHASE CODING
The phase coding technique works by replacing the phase of an initial audio segment with a reference phase that represents the secret information. The remaining segments phase is adjusted in order to preserve the relative phase between segments. Phase coding is one of the most effective coding methods in terms of signal to noise ratio. When there is a drastic change in the phase relation between each frequency component, noticeable phase dispersion will occur. However, as long as the modification of the phase is sufficiently small, an inaudible coding can be achieved. This method relies on the fact that the phase components of sound are not as perceptible tothe human ear as noise is.
Phase coding is explained in the following procedure:
- The original sound signal is divided into smaller segments such that length of each segment is same as the size of the message to be encoded.
- Matrix of the phases is created by applying Discrete Fourier Transform (DFT).
- Phase differences between adjacent segments is calculated.
- Using the new phase of the first segment a new phase matrix is created while preserving the original phase differences.
- The sound signal is reconstructed by applying the inverse Discrete Fourier Transform using the new phase matrix and original magnitude matrix and then concatenating the sound segments back together.
The receiver must know the segment length to extract the secret information from the sound file. Then the receiver can use the DFT to get the phases and extract the secret
Figure 7. Phase coding
4.4 SPREAD SPECTRUM
In audio steganography, the basic spread spectrum (SS) method attempts to spread secret information across the frequency spectrum of the audio signal. This is similar to a system which uses an implementation of the LSB that spreads the message bits randomly over the entire sound file. However, unlike LSB coding, the Spread Spectrum method spreads the secret information over the frequency spectrum of the sound file using a code which is independent of the actual signal. As a result, the final signal occupies a bandwidth which is more than what is actually required for transmission.
The Spread Spectrum method is capable of contributing a better performance in some areas compared to LSB coding, phase coding, and parity coding techniques in that it offers a moderate data transmission rate and high level of robustness against removal techniques. However, the Spread Spectrum method has one main disadvantage that it can introduce noise into a sound file. The steps followed in Spread Spectrum are as follows:
- The secret message is encrypted using a symmetric key, k1.
- The encrypted message is encoded using a low rate error-correcting code. This step increases the overall robustness of the system.
- The encoded message is then modulated using a pseudo-random signal that was generated using a second symmetric key, k2.
- The resulting random signal that contains the message is interleaved with the cover-signal.
- The final signal is quantized to create a new digital audio file that contains the message.
- This process is reversed for message extraction.
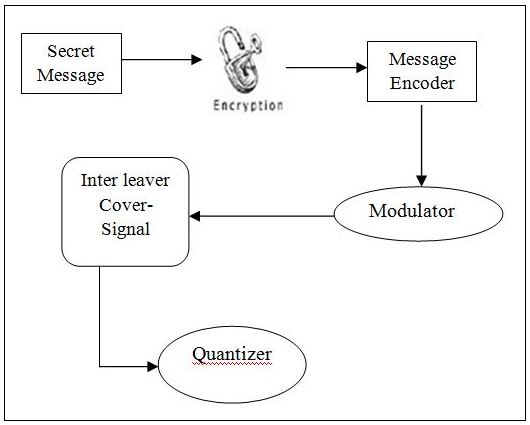
Figure 8. Spread Spectrum (SS)
4.5 ECHO HIDING
Echo hiding technique embeds secret information in a sound file by introducing an echo into the discrete signal. Echo hiding has advantages of providing a high data transmission rate and superior robustness when compared to other methods. Only one bit of secret information could be encoded if only one echo was produced from the original signal. Hence, before the encoding process begins the original signal is broken down into blocks. Once the encoding process is done, the blocks are concatenated back together to create the final signal [5, 20]. Echo Hiding is shown in Figure.
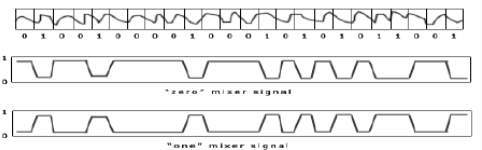
Figure 9. Echo hiding
Chapter 5 IMPLEMENTATION DESIGN FOR AUDIO STEGANOGRAPHY
5.1 BLOCK DIAGRAM
The block diagram depicting the proposed work is as follows:
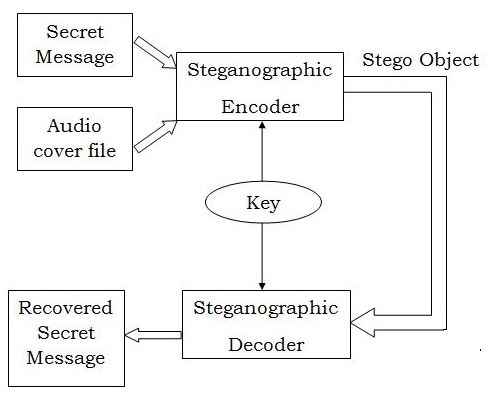
Figure 10. Block Diagram
Here, the secret message file and the cover audio file are opened and sent into the steganographic encoder. The result of the encoder is the cover audio file with the LSBs of all its bytes modified using the message bits. This file known as the Stego-object is sent to the reciever through a communication channel.
At the reciever end, the stego object is processed only if the exact key that was used at the encoder is given. Once the key is given by the user, the decoder extracts the message from the stego-object and gives back the secret message file with a minimum BER.
5.2 PROCEDURE
The algorithm used to implement the proposed method can be divided into four parts as mentioned below. The first two parts give the steps to embed the message into the cover audio file and the next two part give the steps to detect the message from the received signal.
5.2.1 Compatibility Check Algorithm
- Open the message file containing the secret text to be transmitted.
- Find the length of the message (number of bytes) and store it as L.
- Open the audio cover file.
- Convert the samples obtained into bytes of binary data and store them in an array.
- Find the length of the audio signal(number of bytes) and store it as N.
- Choose a key for steganography of length K.
- Check if the length of message and key together is less than or equal to one-eighth of the audio length.
- If the above condition is satisfied, print a suitable message and start the steganography process.
- If the above condition is not satisfied, print the suitable message and stop the execution.
The flowchart corresponding to the above compatibility check is shown below. The lengths of message and cover files are to be chosen carefully to avoid errors.
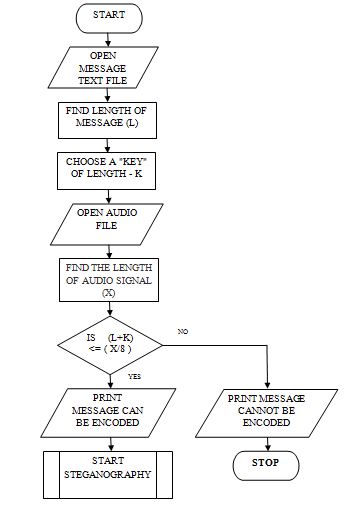
Figure 11. Encoding Flowchart
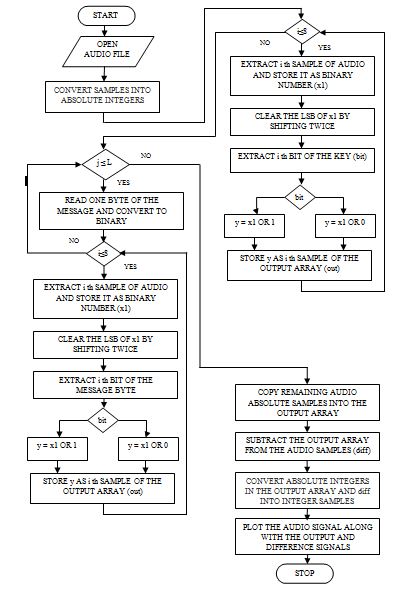
5.2.2 Encoding Algorithm
- Convert the chosen key into binary format.
- Extract one byte of the audio file at a time.
- Clear the LSB of the extracted byte.
- Choose one bit of the key and place it in the LSB of the extracted audio byte. Store the modified byte into another array.
- Continue the above steps(2-4) till all the bits of the key are embedded into the audio samples.
- Extract one byte of the message at a time.
- Repeat the steps from 2-4 for all the bits of the extracted message byte.
- Repeat steps 6-7 for all the message bytes.
- Copy all the remaining (unaltered) bytes of the audio signal array into the new array to avoid any modifications in the length of the audio signal.
- Convert the newly generated array of binary bytes into samples of the audio signal using the initial sampling frequency.
- Plot the initial audio samples and the newly generated audio samples in wave format. It can be observed that the two signal appear almost identical.
- In order to observe the difference created in the audio signal due to the message embedding, find the difference of the samples of the initial and newly generated arrays and store it in another array (difference array).
- Convert the binary difference array into samples of audio data using the same sampling frequency used above.
- Plot the difference of the two arrays. It can be observed that there are very minimal differences between the two signals.
- Generate the audio signal from the above samples and transmit it through the communication channel.
The complete encoding procedure can be depicted in a flowchart as follows:
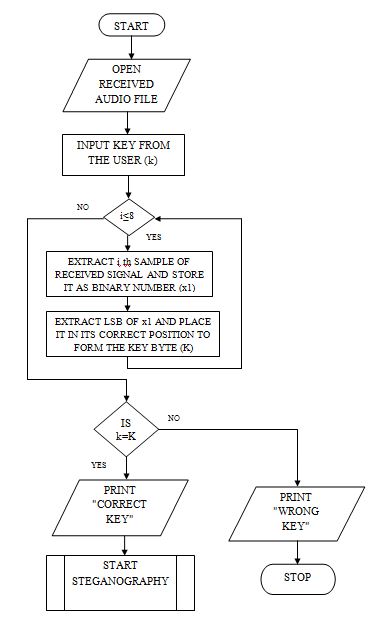
5.2.3 Algorithm to check correctness of the key
- Prompt the user to enter a key.
- Extract eight bytes of the received signal and convert them into binary values.
- Extract LSBs of all the eight bytes and form the corresponding message byte which is the key used while encoding.
- Compare the extracted key with the key entered by the user.
- If the correct key is entered, display a suitable message and go to decoding algorithm.
- If the entered key is wrong, display a suitable message and abort the reception process.
The above algorithm can be depicted as follows:
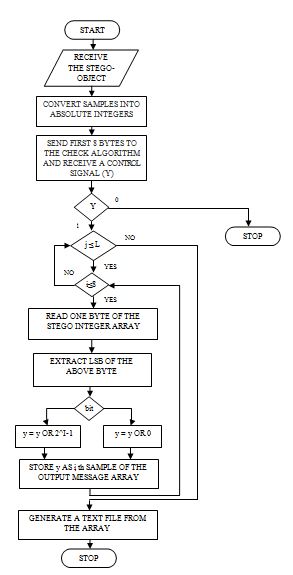
5.2.2 Decoding Algorithm
- Receive the stego-object from the communication channel.
- Convert the signal into samples using the sampling frequency.
- Convert the samples into absolute integers and subsequently into an array binary bytes.
- Send the first eight bytes to the checking algorithm (the above algorithm 6.2.2)and receive a control signal.
- If the control signal is positive, extract bytes of the stego array one at a time.
- Extract the LSB of each byte.
- Form eight bit groups of the extracted LSBs.
- Store such eight groups of bits in another array.
- Convert the newly generated array into characters and store it into a text file.
5.3 IMPLEMENTATION
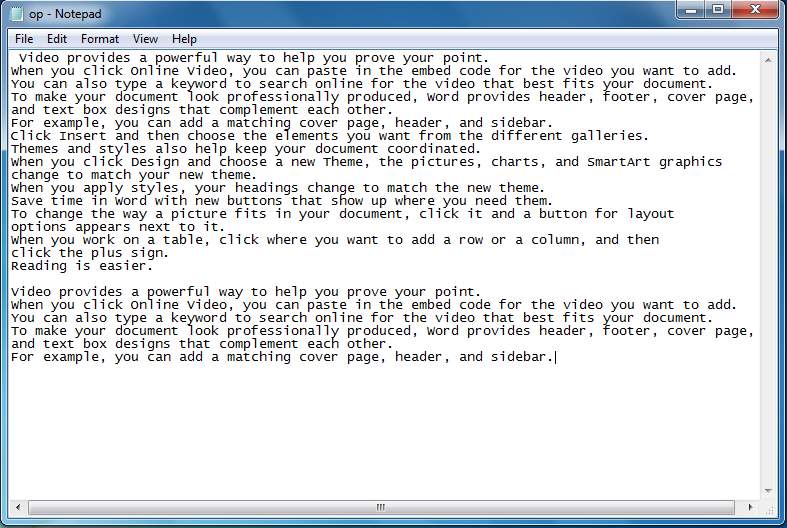
In this project, the message chosen is a paragraph of text stored in a “.txt” file and the cover audio is an audio signal stored in a “.wav” file. The two files are opened through Matlab using the “fopen” function. The message file is shown in the following figure:
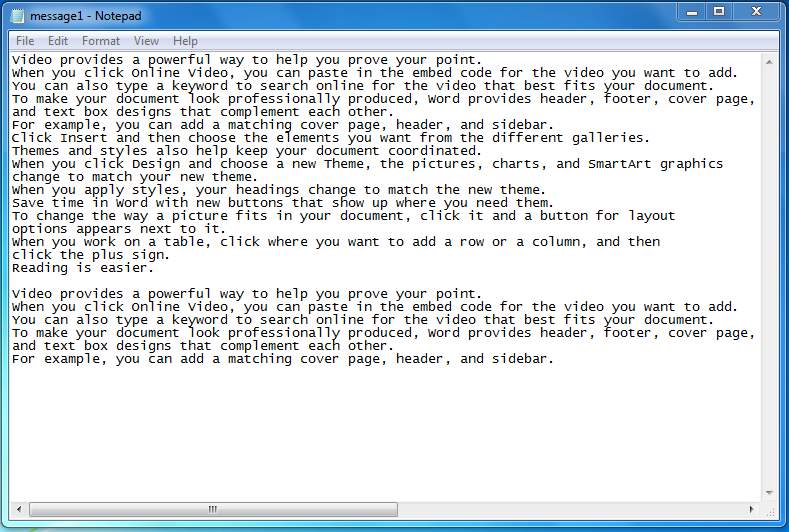
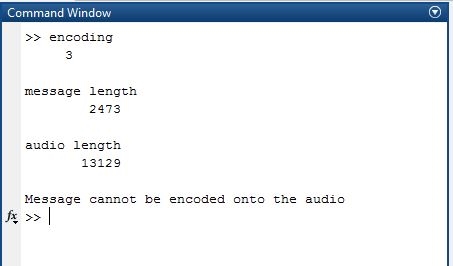
The first step of the proposed method of Audio Steganography involves checking the lengths of the secret message and the cover audio file. The lengths need to satisfy certain conditions to be compatible with each other. The output generated after measuring and comparing the lengths is as follows:
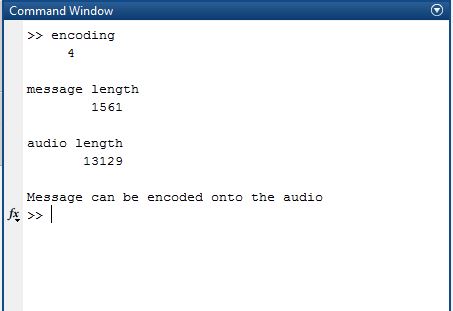
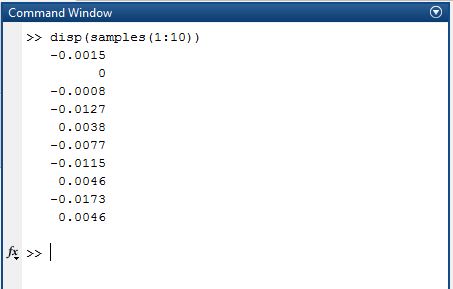
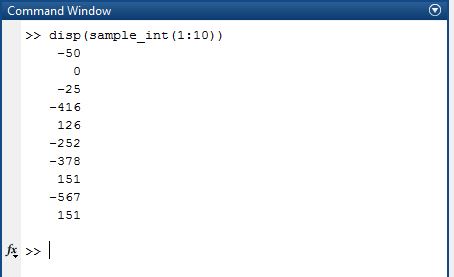
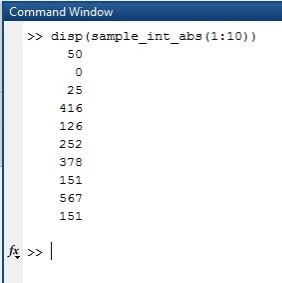
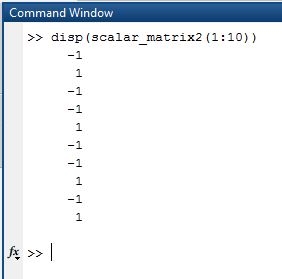
Once the “Message can be encoded onto the audio” message is displayed, the input audio file is sampled to obtain an array of sample values. The sample values are converted into integers and subsequently into absolute values while preserving the sign status in another array. The first few values of the samples before and after conversion into integers are shown in the following figure.
In case the lengths of the message and the audio cover do not satisfy the required conditions, the execution of the code is halted with a suitable message. Such a situation is shown in the following figure
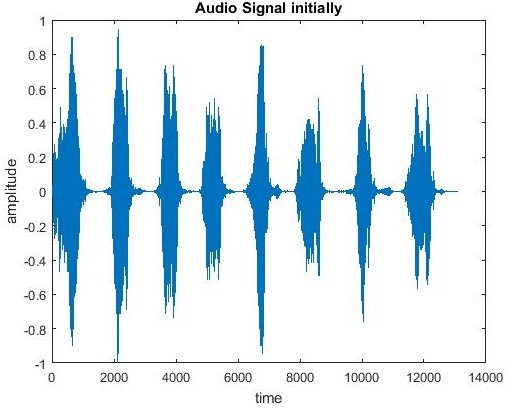
After converting the samples array into absolute values array, the audio signal is plotted with the obtained samples. The obtained plot is as shown below.
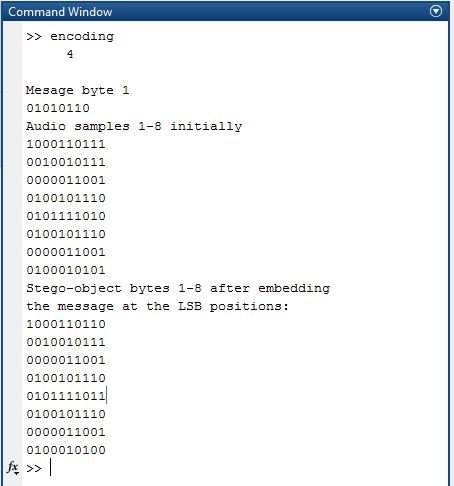
Embedding the message bytes onto the audio bytes is done as explained in the previous section. The process of embedding the first message byte into the audio samples is shown in the following figure
After the embedding is done, the absolute samples are converted back into audio signal samples using the procedure opposite to that used in the beginning. The final audio samples obtained are plotted as follows
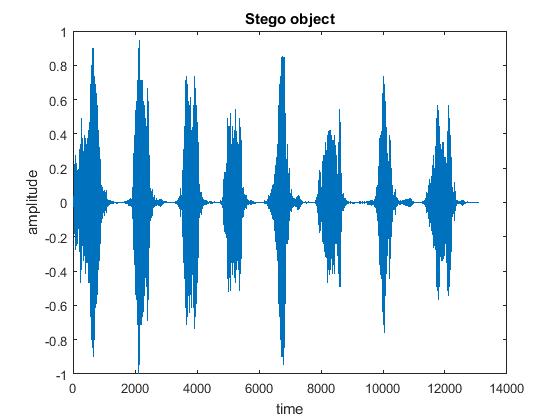
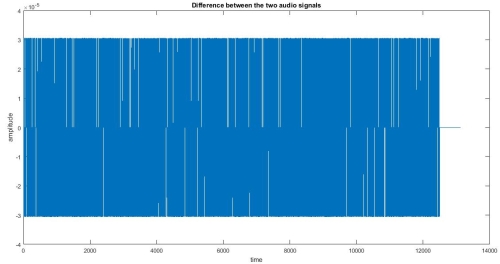
The difference between the audio signals before and after steganography is calculated and is plotted. The following plot shows that there is hardly any difference between the two signals thus making this procedure highly feasible as the BER is very minimal.
Thus, the process of embedding a text message into a cover audio file has been accomplished. The obtained output file known as the “Stego-Object” is transmitted along a communication channel to the intended receiver. Even if an eavesdropper gets his hands on the stego-object, he will not be able to recognize the presence of a message in the audio.
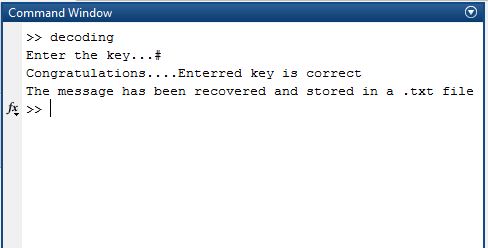
At the receiving end, the user is asked to enter the “Key” to ensure that he is the intended receiver. Upon receiving the entered key, the program checks the first eight incoming bytes and extracts the LSBs to form a byte. This newly formed byte was the key used during encoding. In case the keys match, the message can be recovered by the receiver. Such a case is shown below
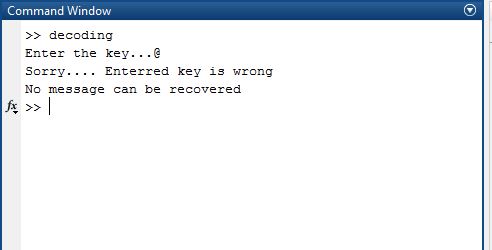
If the entered key is wrong, a suitable message is displayed and the execution stops. The output shown in this case is as follows
5.4 EVALUATION OF AUDIO STEGANOGRAPHY
5.4.1 ADVANTAGES
Audio Steganography has the following advantages
- It has the potential to conceal more information compared to image steganography since audio files are larger than images. Also, the human ear is very less sensitive to small changes in amplitude of the audio which can be used to store large amounts of information.
- It provides a variety of methods for data hiding thereby allowing different parties to implement it in different ways. Depending upon the requirements of the company, higher data hiding rates can be obtained by modifying various factors of the audio.
- It has an ability to combine with existing cryptography techniques.
- Already existing data security methods can be extended by including steganography as it involves no hardware modifications.
- Any kind of data can be hidden into an audio file. Thus steganography combined with high levels of encryption offer maximum data security..
- Greater amounts of information can be embedded without audible degradation thereby making statistical analysis more difficult.
- As emphasis placed on the areas of copyright protection, privacy protection, and surveillance increases, Steganography will continue to grow in importance as a protection mechanism.
- Many maliciousm attacks against image Steganography algorithms cannot be implemented against audio Steganography schemes. Consequently, embedding data into audio seems more secure method due to less steganalysis techniques for attacking to audio.
- Audio Steganography addresses key issues brought about by the MP3 format and the need for a secure broadcasting scheme that can maintain the secrecy of the transmitted information, even when passing through insecure channels.
5.4.2 LIMITATIONS
- Embedding additional information into audio sequences is a more tedious task than into images, due to dynamic supremacy of the human audio system over human visual system.
- Copyrights mark hidden in audio data using substitution could be easily manipulated or destroyed if any intermediaries comes to know that information is hidden this way.
- Compression of an audio file changes its structure completely. If the compression is lossy, it by removes all the frequencies that the human ear cannot hear. If audio containing hidden message is compressed, removal of certain frequencies during compression may lead to loss in data which is undesirable.
- As the length of the message increases, a larger audio file is required
5.4.3 APPLICATIONS
Audio data hiding is to be used whenever you want prevent unintended receivers from becoming aware of the existence of a secret message. It has applications in many fields including
- It can be used to hide secret chemical formulae or ideas or plans for new inventions.
- It is also used hide any secret information in the non-commercial sector.
- It can be used by terrorists to keep their communications secret and also to coordinate or plan their attacks
- It can be used in applications where text data or audio data can be hidden to protect the authenticity of words spoken or sounds used to convey important information.
- It is used in the music sector for guiding songs over the broadcast radio.
- It is of great interest for the security of copyrighted digital media, and to the government for information systems security and for covert communications.
5.4.4 CONCLUSION
Thus we can conclude that audio data hiding techniques can be used for a number of purposes other than information tracing, finger printing, tamper detection etc. Both steganography and cryptography have certain limitations, yet these are the most familiar aspects of security and privacy. Either steganography or cryptography cannot provide maximum trust towards security separately. Both combined steganography and cryptography forms a double layer protection approach which can yield better secure solution for information sharing. As the sky is not limit so is not for the development. Man is now advancing his own boundaries to make every thought or idea possible. So these operations mentioned above can be further modified as it is the world of Information Technology.
REFERENCES
[1] http://www.mathworks.com
[2] C. Yeh, C. Kuo, (October 1999)Digital Watermarking Through Quasi M- Arrays, Proc. IEEE Workshop On Signal Processing Systems, Taipei, Taiwan, Pp. 456-461.
[3] Dr. D Mukhopadhyay, A Mukherjee, S Ghosh, S Biswas, P Chakarborty (2005.) An Approach for Message Hiding using Substitution Techniques and Audio Hiding in Steganography, IEEE.
[4] IEEExplorehttp://ieeexplore.ieee.org/search/searchresult
APPENDIX A
MATLAB R2016a
4.1. Introduction to MATLAB
MATLAB is a superior dialect for specialized processing. It incorporates calculation, perception, and programming in a simple to-utilize condition where issues and arrangements are communicated in commonplace numerical documentation. Run of the mill utilizes incorporate
- Math and calculation
- Algorithm improvement
- Data securing
- Modeling, reproduction, and prototyping
- Data investigation, investigation, and perception
- Scientific and building design
- Application improvement, including graphical UI building
MATLAB is an intelligent framework whose fundamental information component is an exhibit that does not require dimensioning. This permits you to take care of numerous specialized processing issues, particularly those with grid and vector definitions, in a small amount of the time it would take to compose a program in a scalar non intuitive dialect, for example, C or FORTRAN.
The name MATLAB remains for framework research facility. MATLAB was initially composed to give simple access to lattice programming created by the LINPACK and EISPACK ventures. Today, MATLAB motors fuse the LAPACK and BLAS libraries, implanting the best in class in programming for grid calculation.
MATLAB has advanced over a time of years with contribution from numerous clients. In college conditions, it is the standard instructional device for early on and propelled courses in arithmetic, building, and science. In industry, MATLAB is the apparatus of decision for high-efficiency research, improvement, and examination.
MATLAB highlights a group of extra application-particular arrangements called tool stash. Important to most employments of MATLAB, tool stash permit you to learn and apply specific innovation. Tool stash are complete accumulations of MATLAB capacities (M – records) that extend the MATLAB condition to take care of specific classes of issues. Territories in which tool kits are accessible incorporate flag preparing, control frameworks, neural systems, fluffy rationale, wavelets, reenactment, and numerous others.
4.1.1 The MATLAB framework
The MATLAB framework comprises of five principle parts
1. Development Environment:
This is the arrangement of instruments and offices that help you utilize MATLAB capacities and documents. A large number of these devices are graphical UIs. It incorporates the MATLAB desktop and order window, a charge history, a manager and debugger, and programs for survey help, the workspace, documents, and the inquiry way.
2. The MATLAB Mathematical Function Library:
This is a boundless accumulation of computational calculations extending from basic capacities, similar to entirety, sine, cosine, and complex number-crunching, to more modern capacities like lattice reverse, grid Eigen values, Bessel capacities, and quick Fourier changes.
3. The MATLAB Language:
This is an abnormal state lattice/cluster dialect with control stream proclamations, capacities, information structures, input/yield, and question arranged programming highlights. It permits both “programming in the little” to quickly make down to business discard projects, and “programming in the extensive” to make substantial and complex application programs.
4. Graphics:
MATLAB has broad offices for showing vectors and lattices as diagrams, and in addition explaining and printing these charts. It incorporates abnormal state capacities for two-dimensional and three-dimensional information representation, picture preparing, liveliness, and introduction design. It likewise incorporates low-level capacities that permit you to completely alter the presence of design and additionally to construct finish graphical UIs on your MATLAB applications.
5. The MATLAB Application Program Interface (API):
This is a library that permits you to compose C and FORTRAN programs that connect with MATLAB. It incorporates offices for calling schedules from MATLAB (dynamic connecting), calling MATLAB as a computational motor, and for perusing and composing MAT-documents.
Different tool compartments are there in MATLAB for registering acknowledgment strategies, however we are utilizing IMAGE PROCESSING tool stash.
Cite This Work
To export a reference to this article please select a referencing stye below:
Related Services
View allRelated Content
All TagsContent relating to: "Communications"
Communications cover an array of systems and technologies used to send information, including radio, TV, phone, and computer systems. Communications studies also provide an understanding of effective conveyance of information in various sectors such as the press, broadcasting, film, advertising and digital media.
Related Articles
DMCA / Removal Request
If you are the original writer of this dissertation and no longer wish to have your work published on the UKDiss.com website then please:




