Message Queue Telemetry Transport Protocol for IoT networks
Info: 5036 words (20 pages) Dissertation
Published: 16th Dec 2019
Tagged: Internet of Things
Table of Contents
1.1. What is Internet of Things
1.3. Application Areas for the IoT
1.3.1. Building & home automation
1.3.4. Near Field Communication NFC
5. Application Layer IoT protocols
5.2.1. Characteristics of CoAP:
12. ACADEMIC HONESTY DECLARATION
ABSTRACT
The MQTT is a Client Server publish/subscribe messaging transport protocol. It is light weight, open, simple, and designed so as to be easy to execute. These characteristics make it perfect for use in many cases, including constrained environments such as for communication in Machine to Machine (M2M) and Internet of Things (IoT) contexts where a small code footprint is required and/or network bandwidth is at a premium. The protocol works over TCP/IP, or over other network protocols that provide ordered, lossless, bidirectional connections.
1. Introduction
Learn about how to send messages between mobile phone apps using MQ telemetry transport (MQTT). The protocol is intended for use on wireless networks and low bandwidth. A mobile app that uses MQTT sends and receives messages through calling an MQTT library. The messages are exchanged by an MQTT messaging server.The MQTT client and the server dealing the complexities of transmit reliable messages to mobile applications and maintain the cost of small network management.
MQTT apps run on mobile devices, like tablets and smartphones. MQTT is also used for telemetry to receive data from sensors, and to remotely control them. For mobile devices and sensors, MQTT offers a highly scalable publish/subscribe protocol with guaranteed delivery. To send and receive MQTT messages, you can add an MQTT client library to your app [1].
1.1. What is Internet of Things
The Internet of Things (IoT). is an emerging global Internet-based information, which started in 1999, that are connected to the Internet with a custom IP address as other traditional devices for facilitate the exchange of goods and services. The past years have witnessed increased interest in the internet of things.
Interest including the provision of information technology infrastructure to facilitate the exchange of (things) a reliable and safe manner, its function is to overcome the gap between the things in the physical world and its representation in information systems,ability of network devices to sense and collect data from the world around us, and then share that data across the Internet where it can be processed and utilized for various interesting purposes [2].
It is possible that these things are present with alarm household, automotive, smart TVs, and ATM machines, as well as a lot of things that are expected to invade our daily lives in the next few years that we can now be worn, such as smart watches, smart glasses and also smart shoes sports.
1.2. Why we need IoT
We need IoT to connect all potential objects to interact each other on the internet to provide secure, comfort life for human. Internet of Things (IoT) makes our world as possible as connected together. Interest including the provision of information technology infrastructure to facilitate the exchange of (things) a reliable and safe manner, its function is to overcome the gap between the things in the physical world and its representation in information systems, ability of network devices to sense and collect data from the world around us, and then share that data across the Internet where it can be processed and utilized for various interesting purposes.
It is possible that these things are present with alarm household, automotive, smart TVs, and ATM machines, as well as a lot of things that are expected to invade our daily lives in the next few years that we can now be worn, such as smart watches, smart glasses and also smart shoes sports [3].
1.3. Application Areas for the IoT
1.3.1. Building & home automation
IoT offers a wide range of new technologies for monitoring and controlling, of intelligent buildings and smart homes, by enhancing security to reduce energy and maintenance costs. With home automation control system we make our home devices smart. Smart in the sense that, the devices can be monitored or perform task according to the user‘s instructions. Such as, a door lock system where if anyone unknown person tries to enter into the house without authorization then the door lock will activate an alarm attached to the door and in this we can say our home is smart enough to provide us security.
1.3.2. Health care

Figure 1: Healthcare in IoT
In Figure 1 IoT is shaping modern technology to improve and enhance the quality and accessibility of digital product that are remodeling the health and fitness industries. For example, daily account your movement or your movement during intense physical activity and thereby estimate the number of steps you’ve walked and how many calories you burned.
The IoT brings many technologies in the field of health care that makes human life more comfortable. There are many apps that have been developed to track the heart beat and activity of nervous system of human body. They give the user day to day information of their health status.
1.3.3. Automotive

Figure 2: range of cutting-edge automation
In Figure 2 IoT provide a wide range of cutting-edge automation for the modern automobile from headlights to taillights and all systems in between. In cars there is a sensor that can sense whether the driver of the car is in drunk or not. This stop chances of road accidents by stopping the car automatically [4], [5].
1.3.4. Near Field Communication NFC

Figure 3: Participationservice
- In Figure 3 Participationservice: through this service you can share photos and files between two phones and it can be used in some games.
- Device connection: several devices are now available on the markets may be connected to the phone through this technology, such as some audio equipment and some headphones.
- Service advantage: it can read some paintings with this particular slide by moving some information to the phone to learn more about a place or read the menu in some restaurants or get train schedules at some stations[6].
1.4. The aim of this project
My aim in this project is to cover both the MQTT protocol and how it works. The MQTT is a Client Server publish/subscribe messaging transport protocol. In this project, in practical part I will learn to collect data from a temperature and humidity sensor (DHT11), I will process them with an Arduino chip with ESP8266 chip, send it via Wi-Fi to a server in the cloud (Thingspeak) and monitor the data with an application for Android.
2. MQTT history
MQTT was created with the aim of collecting data from many devices and after that, transfer that data to the IT infrastructure. It is lightweight, and thus ideal for remote monitoring, especially in connections M2M, that require a short code footprint or where network bandwidth is bounded.
MQTT was invented in 1999 by Dr. Andy Stanford-Clark and Arlen Nipper. inventor Arlen Nipper is the head of Cirrus Link Solutions, the company that improve the Cirrus Link MQTT Modules for Ignition[7].
3. How Does MQTT Work?
MQTT is a publishing / subscription protocol that allows edge devices from the network to publish for broker. The clients connect to this broker, which intercede and then contact between two devices. Each device can subscribe, or register, to confirm topics. When another customer posts a message to a shared topic, the broker redirects the message to any shared client.
The MQTT is bi-directional and keeps cycle awareness. If it loses a connection device from the network, all subscribers clients will be notify with the “Last Will and Testament” which is a feature of the MQTT server so that any authorized client in the system can share a new value back to the edge-of-network device, keep the bidirectional connection.
The efficiency and lightweight of MQTT makes it probably to significantly increase the amount of data being monitored or controlled. Before the invention of abomination, nearly 80% of the data was left in remote locations, although different business lines could use this data to choose smarter decisions. Now MQTT makes it possible to gather, move, and analyze more data that is collected.
Unlike the typical survey / response model for many protocols, which tend to over-saturate data connections with non-static data, a publish / subscription model increases the bandwidth available [8].
4. Who Uses MQTT?
It has been originally developed for low-bandwidth, high-latency data links used in the oil and gas manufacture. However, MQTT is now used in many apps outside oil and gas. From controlling the smart lighting systems to the Facebook Messenger app. Amazon Web Services recently declared that Amazon Internet of Things (IoT) is based on MQTT, it seems that MQTT is the protocol appropriate for control systems used by industrial organizations, and we can expect that their rate of adoption will only increase in the future [8].
5. Application Layer IoT protocols
5.1. MQTT
MQTT is designed as a lightweight protocol to provide publishes and subscribe message. The message subscriber subscribes to an MQTT topic provided by the message publisher. Then, if any change occurs in the MQTT topic, the subscriber receives a PUBLISH command to get information of the change[9].
The broker relays requests to subscribe to MQTT topics and messages in figure 9.
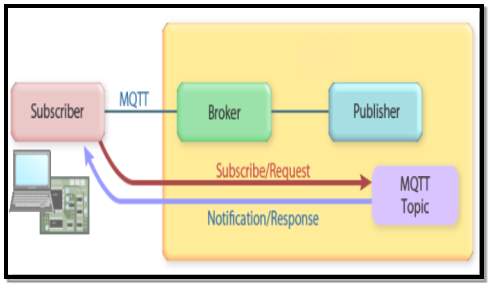
Figure 4: Overview of MQTT protocol.
5.2. Protocol CoAP
The Constrained Application Protocol (CoAP) is protocol a specialized web for use with restricted networks and limited nodes in IoT.It is the fifth layer of the Internet Protocol package, the application layer, which is used by Internet browsers and is called the user-agent. The gateway 5683 on the server is often used in collaboration with the fourth layer, specifically with the protocol (UDP)[10].
5.2.1. Characteristics of CoAP:
Work CoAP counterparty HTTP to the transfer of data in a way that is expressed as (Not consistent) between the server and the client. The system is adopted Client Server Response any system of response between the client and the server.
The CoAP is designed to maintain as much as possible on properties HTTP but in a simpler way, and a standard method of exchange between CoAP and HTTP was easily defined[10].
5.2.2. Means of CoAP:
The CoAP system identifies four of the eight devices known to the HTTP. These means or requests are sent to the server sometimes called (verbs) which describe the requested request on the attached source.
- GET
Request a proposal; it is the most widely used tool on the web today
- POST
Send information from the customer’s user to the attached target. Data is placed within a section (body) of the request.
- PUT
Download to target.
- DELETE
Clear the target.
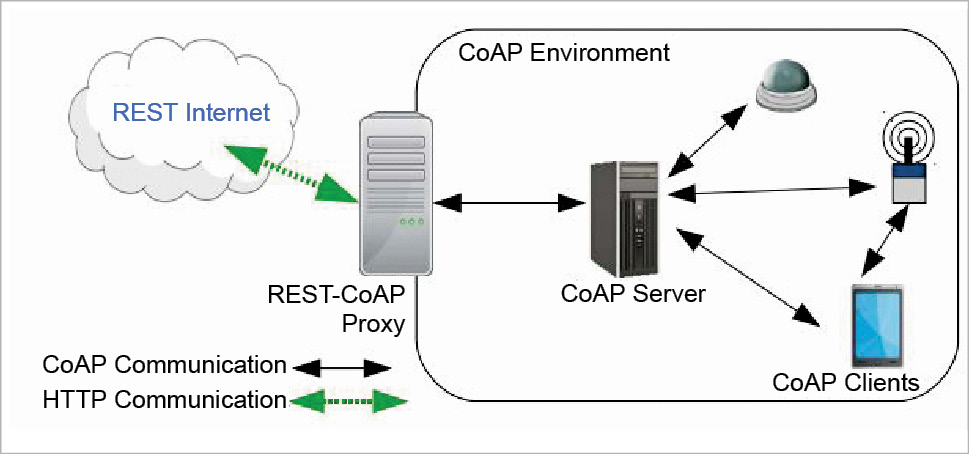
Figure 5: How CoAP works
5.3. Protocol HTTP
HTTP is a request/response protocol where clients request information from a server and the server responds to these requests. A request is basically made up of a method, a resource, some headers, and some optional content. A response is made up of a three digit status code, some headers and some optional content. This can be observed in the following diagram.
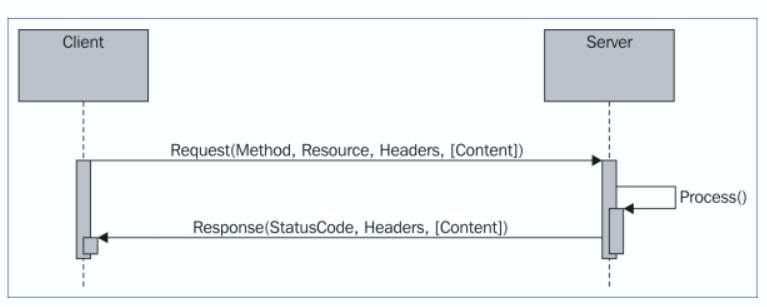
Figure 6: HTTP request/response pattern
Each resource, originally thought to be a collection of Hypertext documents or HTML documents, is identified by a Uniform Resource Locator (URL). Clients simply use the GET method to request a resource from the corresponding server. In the structure of the URL presented next, the resource is identified by the path and the server by the authority portions of the URL. The PUT and DELETE methods allow clients to upload and remove content from the server, while the POST method allows them to send data to a resource on the server, for instance, in a web form. The structure of a URL is shown in the following diagram in Figure 6[11].

Figure 7: Structure of a URL
5.4. Protocol LoRaWAN
LoRaWAN is protocol for iot wide area network, and control media access (MAC) for wide area networks. It is styles to allow low-power devices to communication with Internet-connected apps via long-range wireless connections. LoRaWAN can be set to the second and third layer of the OSI model.This is done at the top of the LoRa or FSK formation in the industrial, scientific and medical radio bands (ISM). Protocols LoRaWAN are defined via the LoRa Alliance and add official character in the specification of LoRaWAN. The LoRaWAN pile is show below [12].
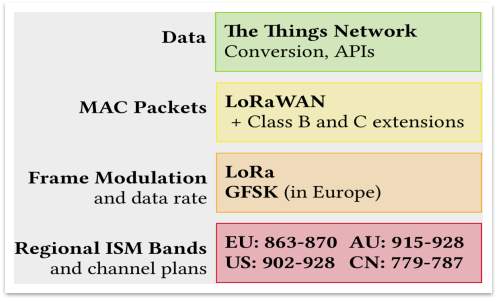
Figure 8: Overview of The IoT Network LoRaWAN stack
5.5. Protocol ZigBee
New Web protocol based on IEEE standard 802.15.4 Protocol, this latest radical shift in industry and homes it has built a network of wireless sensors and switch to connect Labs wireless. It is today used in smart homes. The Bluetooth protocol being consumes little energy enough battery for two years and also features a low transfer rate data from 50kb to 250kb and that’s enough to move the value of sensors and command transfer to other devices, and enjoys a good level of security as well as he can connect an unlimited number of nodes in the network unlike Bluetooth which allows only eight devices[13].
5.5.1. ZigBee features:
- Standard: ZigBee 3.0 based on IEEE802.15.4
- Frequency: 2.4GHz
- Range: 10-100m
- Data Rates: 250kbps

Figure 9: ZigBee can control your world.
5.6. Protocol Bluetooth
Bluetooth wireless technology is a specification for short-range, low-cost, using Bluetooth wireless data transfer is usually between two cell phones or connect your computer with peripherals such as a mouse or keyboard or headset, and latterly instrumental in connecting phones with wearable smart devices, such as fitness tracking systems and door locks and lights, that enables user-friendly connectivity among portable and handheld personal devices, and provides connectivity of these devices to the Internet.
6. MQTt architectures
Protocol MQTT is based on “Publish/Subscribe” style and “topic” idea. A client can be a publish, a subscriber or both. If it is a publish, it publishes a message on a topic; if it is a subscriber, it subscribes to a specified topic so that it can receive all the messages published on that topic. The topic is the technique via which clients exchange messages and technically it is a message queue; the broker have to manage all subscriptions to the queues (topics) and it have to relay messages from clients publishing messages to a specific topic to those who are subscribed to it. This style is also known as “Observer” because a client can monitor a topic for which it is interested in receiving published messages. This module allows distributing one to one and one to many and the publisher don’t need to know anything about subscribers; all of these features guarantee customers to disconnect and connect asynchronously.
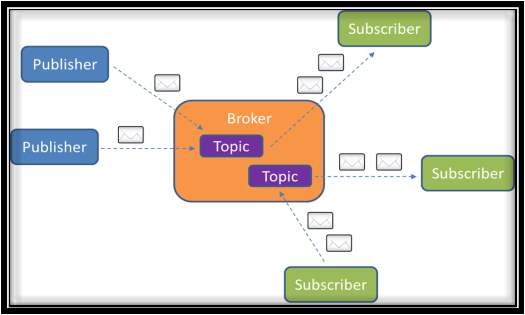
Figure 10: Topic based Publish/Subscribe pattern in MQTT
6.1. MQTT model A
The core elements of MQTT are clients, servers (brokers), sessions, subscriptions and topics[14].
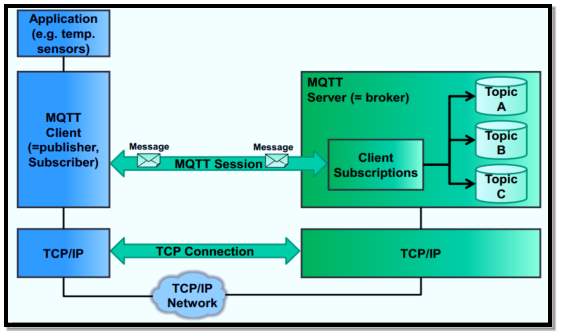
Figure 11:Architecture for core elements of MQTT
6.2. MQTT model B
MQTT client (=publisher, subscriber):
In Figure 11 clients subscribe to topics to share and receive messages. Thus subscriber and publisher are special roles of a client.
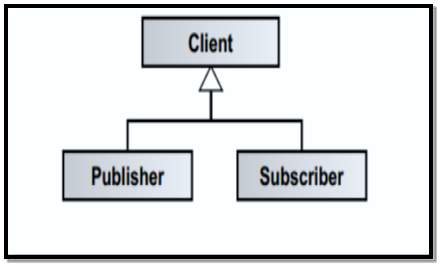
Figure 12: MQTT client = publish, subscribe
MQTT server (=broker):
Servers run topics, i.e. receive subscriptions from clients on topics, receive messages from clients and forward these, based on client’s subscriptions, to concerned clients.
Topic:
In Figure 12 technically, topics are message in queues. Topics support the publish/subscribe pattern for clients.
Logically, topics permit clients to exchange information with defined semantics.
Example topic: Temperature sensor data of a building [14].
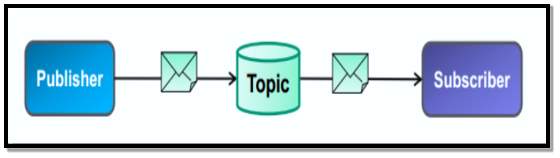
Figure 13 how topics support pattern for clients.
7. Advantages of MQTT
- publish information more efficiently.
- Increase scalability.
- Reduce network bandwidth consumption dramatically.
- Reduce update rates to seconds.
- Very well-suited for remote sensing and control.
- Maximize available bandwidth.
- Extremely lightweight overhead.
- Very safe with permission-based security.
- Used by the oil-and-gas industry, Amazon, Facebook, and other major businesses.
- Saves development time.
- Publish/subscribe protocol collects more data with less bandwidth compared to polling protocols.
8. disadvantegs of mqtt
- Flow control.
- Only control for publish/subscribe.
- Much physical machine to deploy.
- Not easy to implement.
9. ptactical part
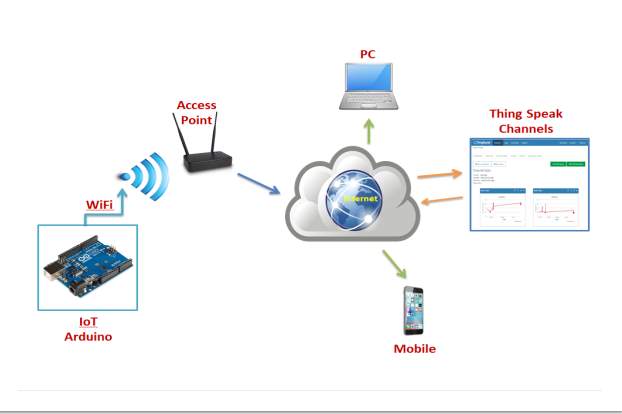
Figure 14: System Architecture
In Figure 13 the system architecture, for use IoT Arduino can connect to Access Point by ESP8266 Wi-Fi. After that, the Access Point send data to Internet, the Internet publish and subscribe to MQTT Program. Example, ThingSpeak, then, view the channel for temperature and humidity in website ThingSpeak and can see or display the temperature and humidity in Computer or Mobile phone by copy the channel ID.
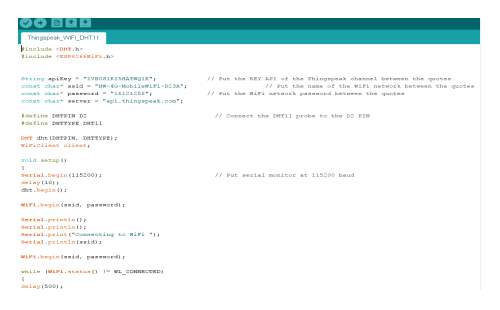
Figure 15: command from Arduino App.
In Figure 14 this code for my project in Arduino program, in line 3 put the ID channel of the ThingSpeak. Then, line 4 put the name of the Wi-Fi network. Next, line 5 put the password of the Wi-Fi network.
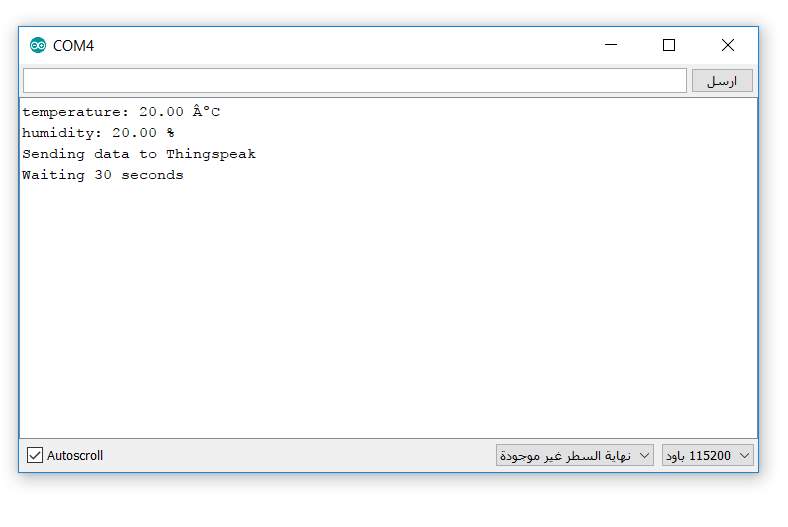
Figure 16: View Temp or Humidity in Arduino App.
In Figure 15this window for the data Temperature and Humidity and update data every 30 seconds.
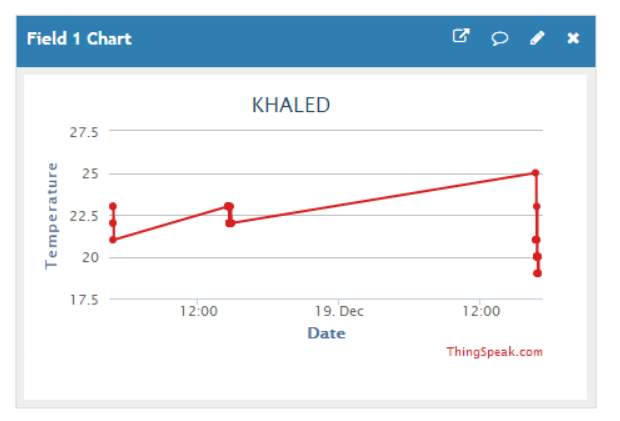
Figure 17: Temperature form ThingSpeak App.
In Figure 16I created this channel for the temperature inside the website ThingSpeak. And display temperature etches 30 second.
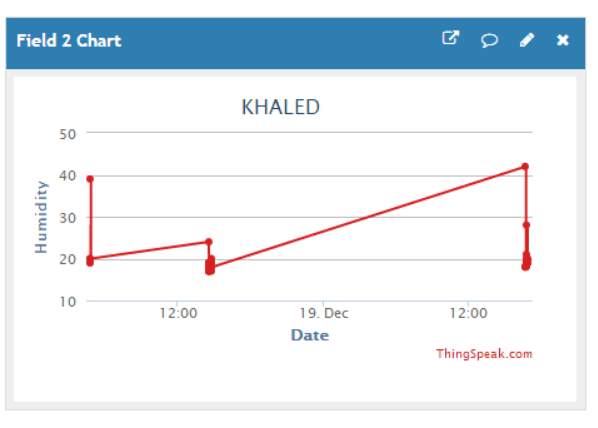
Figure 18: Humidity from ThingSpeak App.
In Figure 17 I created this channel for the Humidity inside the website ThingSpeak. And displays Humidity etch 30 second.
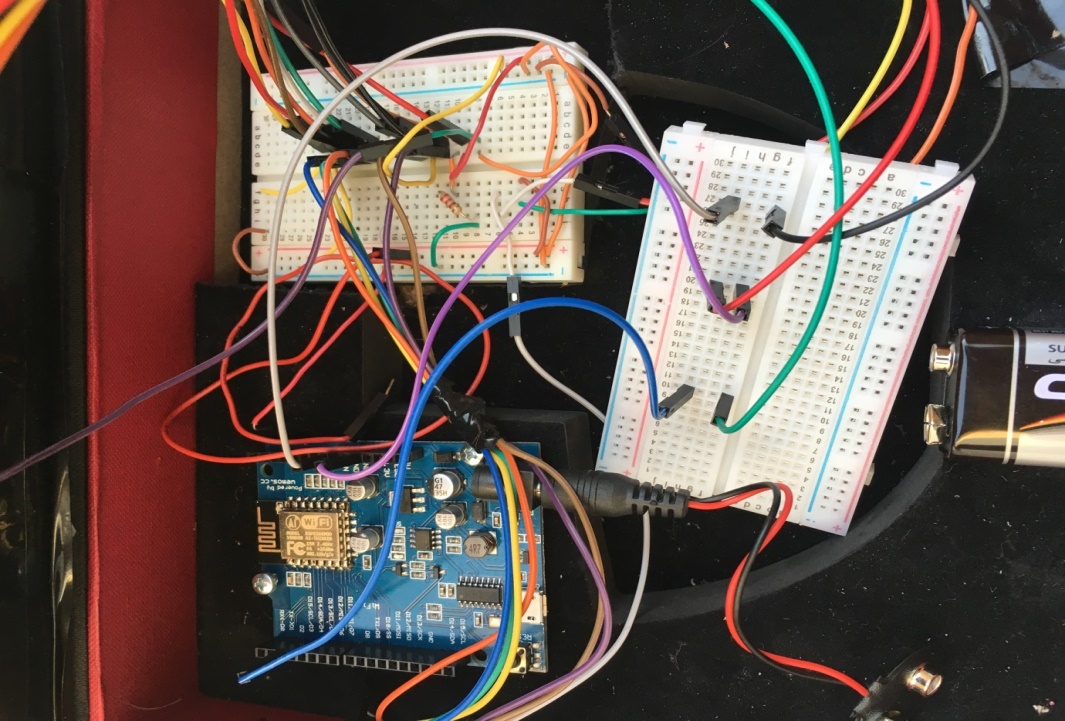
Figure 19: Picture for my practical
I use these tools for my project:
- Arduino UNO.
- ESP8266 Wi-Fi.
- Breadboard.
- DHT11 sensor.
- USB cable.
- Jumper cables.
Figure 20: picture for ThingView App.
In Figure 19 can Download Thingview App from App Store your iPhone, and can see the temperature or humidity for your channel by add the ID channel when your create in website ThingSpeak.
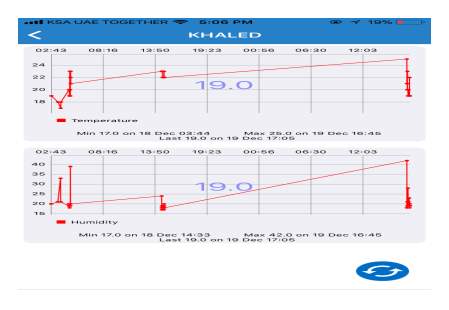
Figure 21: this data from the App ThingView.
In Figure 20after download the App Thingview open the channel and view the data for Temperature and humidity, in same time can see same data in website ThingSpeak from your channel.
10. Conclusion
In the end of my report I talked about many topics for MQTT. So I started with identify of the protocol MQTT. Second I definition of the IoT, which has the potential to improve the basic services in transportation, security, utilities, education, healthcare and other areas, while providing a new ecosystem for application development. Next, I wrote about the apps areas for the internet of things. Also, I wrote about some Apps layer IoT protocol such as, (Protocol CoAP, HTTP, LoRaWAN, and ZigBee). Next, I wrote about the MQTT architectures. After that, in chapter MQTT history I write about the creating protocol MQTT with the aim of collecting data from many devices. I wrote the most important tips about advantages of MQTT.
In the end the IoT is the new technology which can make life easier with use it, that works with make a communication between networks and apps with tangible devices. So, it is worth mentioning that the number of things connected to the Internet IoT is expected to reach 25 billion by 2020. So, it is a new step in the world of technology to improve the level of use of the devices by linked to the Internet.
Also, in my practical part I used an Arduino device which help to explain how IoT works and I specify to use a temperature sensor by connect to the motherboard of Arduino. Then, Arduino can connect to Access Point by ESP8266 Wi-Fi. After that, the Access Point send data to Internet, the Internet publish and subscribe to MQTT Program. Example, ThingSpeak, then, view the channel for temperature and humidity in website ThingSpeak and can see or display the temperature and humidity in Computer or Mobile phone by copy the channel ID. So, it was worked as an explanation of MQTT, and show how is it work. IoT is revelation technologies which can change the life to be easier with use it.
11. References
[1] A. Stanford-Clark and H. L. Truong, “Mqtt for sensor networks (mqtt-sn) protocol specification,” Int. Bus. Mach. IBM Corp. Version, vol. 1, 2013.
[2] R. H. Weber and R. Weber, Internet of things, vol. 12. Springer, 2010.
[3] C. Alcaraz, P. Najera, J. Lopez, and R. Roman, “Wireless sensor networks and the internet of things: Do we need a complete integration?,” in 1st International Workshop on the Security of the Internet of Things (SecIoT’10), 2010.
[4] J. Gubbi, R. Buyya, S. Marusic, and M. Palaniswami, “Internet of Things (IoT): A vision, architectural elements, and future directions,” Future Gener. Comput. Syst., vol. 29, no. 7, pp. 1645–1660, 2013.
[5] L. Coetzee and J. Eksteen, “The Internet of Things-promise for the future? An introduction,” in IST-Africa Conference Proceedings, 2011, 2011, pp. 1–9.
[6] R. Want, “Near field communication,” IEEE Pervasive Comput., vol. 10, no. 3, pp. 4–7, 2011.
[7] H.-C. Jo and H.-W. Jin, “Adaptive periodic communication over mqtt for large-scale cyber-physical systems,” in Cyber-Physical Systems, Networks, and Applications (CPSNA), 2015 IEEE 3rd International Conference on, 2015, pp. 66–69.
[8] V. Lampkin et al., Building smarter planet solutions with mqtt and ibm websphere mq telemetry. IBM Redbooks, 2012.
[9] K. Tang, Y. Wang, H. Liu, Y. Sheng, X. Wang, and Z. Wei, “Design and implementation of push notification system based on the MQTT protocol,” in International Conference on Information Science and Computer Applications (ISCA 2013), 2013, pp. 116–119.
[10] A. Al-Fuqaha, M. Guizani, M. Mohammadi, M. Aledhari, and M. Ayyash, “Internet of things: A survey on enabling technologies, protocols, and applications,” IEEE Commun. Surv. Tutor., vol. 17, no. 4, pp. 2347–2376, 2015.
[11] R. Bonetto, N. Bui, V. Lakkundi, A. Olivereau, A. Serbanati, and M. Rossi, “Secure communication for smart IoT objects: Protocol stacks, use cases and practical examples,” in World of Wireless, Mobile and Multimedia Networks (WoWMoM), 2012 IEEE International Symposium on a, 2012, pp. 1–7.
[12] J. de Carvalho Silva, J. J. Rodrigues, A. M. Alberti, P. Solic, and A. L. Aquino, “LoRaWAN—A low power WAN protocol for Internet of Things: A review and opportunities,” in Computer and Energy Science (SpliTech), 2017 2nd International Multidisciplinary Conference on, 2017, pp. 1–6.
[13] C.-W. Lu, S.-C. Li, and Q. Wu, “Interconnecting ZigBee and 6LoWPAN wireless sensor networks for smart grid applications,” in Sensing Technology (ICST), 2011 Fifth International Conference on, 2011, pp. 267–272.
[14] P. Desai, A. Sheth, and P. Anantharam, “Semantic gateway as a service architecture for iot interoperability,” in Mobile Services (MS), 2015 IEEE International Conference on, 2015, pp. 313–319.
12. ACADEMIC HONESTY DECLARATION
I, the undersigned, declare that the attached assignment/project is wholly my own work, and that no part of it has been:
- copied by manual or electronic means from any work produced by any other person(s), present or past,
- produced by several students working together as a team (this includes one person who provides any portion of an assignment to another student or students),
- produced by automatic tools or aids
- modified to contain falsified program output,
- or copied from any other source including web sites,
- Except as directly authorized by the instructor.
I understand that penalties for submitting work which is not wholly my own, or distributing my work to other students, may result in penalties.
Full name: Khaled Abdullah Alkhathami
Student Number: 202524037
___________________
Signature
Cite This Work
To export a reference to this article please select a referencing stye below:
Related Services
View allRelated Content
All TagsContent relating to: "Internet of Things"
Internet of Things (IoT) is a term used to describe a network of objects connected via the internet. The objects within this network have the ability to share data with each other without the need for human input.
Related Articles
DMCA / Removal Request
If you are the original writer of this dissertation and no longer wish to have your work published on the UKDiss.com website then please:




